15 benefits of outsourcing your cybersecurity operations
For companies battling data breaches and cyberattacks, MSSPs can offer lower costs, better reliability, broader experience, more skills and other benefits.
Cybersecurity executives are increasingly seeking to outsource some or all of their organization's enterprise security tasks, driven partly by the growing complexity of the work and the need to keep ahead of proliferating cyberthreats.
The use of managed security service providers (MSSPs) is already significant -- and it's likely to continue rising. In a survey conducted for a report on cyberdefense initiatives published in June 2023 by advisory services firm Kroll, 28% of the 1,000 senior IT security decision-makers who responded said their organization had outsourced its cybersecurity operations. Another 49% said they were using a combination of in-house functions and outsourcing.
In addition, 98% of the respondents whose organization had yet to outsource any cybersecurity activities said it had made or was considering plans to do so, according to the report. Fifty-one percent said their organization intended to start outsourcing cybersecurity work in the next 12 months.
Gaining confidence in cyberdefenses was cited as outsourcing's biggest advantage, chosen by 40% of the survey respondents who were working with outside providers. Being confident about security protections is especially critical given the growing number and sophistication of cyberattacks that organizations face and the potential costs -- both financial and reputational -- of successful attacks.
What can you outsource and what should you keep in-house?
Deciding whether to outsource some, most or all enterprise security tasks requires a high-level examination of an organization's security risk profile and an understanding of its tolerance for the identified risks as well as its current and future capacity to fulfill cybersecurity requirements. Based on those assessments, each organization must reach its own conclusions about what it should outsource and keep in-house.
A company that determines its cybersecurity team doesn't have the time, talent, ability or bandwidth to properly execute key tasks should opt for outsourcing, said Jeff Pollard, a vice president and principal analyst at Forrester Research. Similarly, an organization whose internal security professionals don't want to handle certain tasks because they're focused on more critical, high-priority functions should outsource the lower-priority work. And an organization that decides its in-house team shouldn't handle some security activities, such as evaluating insider threats, should likewise hire an MSSP for those responsibilities.
Few organizations outsource their entire cybersecurity operations, according to experts. "Most organizations are looking to create a hybrid: some outsourcing with some internal expertise in specific areas," Pollard said. Hybrid models typically have in-house security executives, managers and senior experts handling strategic tasks, while MSSPs perform lower-level tasks, like monitoring of networks to detect attempted attacks.
What are the benefits of outsourcing cybersecurity?
The benefits that MSSPs can deliver vary based on each individual scenario and how a company crafts the contract and service-level agreements (SLAs) it has with the provider. However, organizations typically see the following benefits when using an MSSP:
- Lower costs. Like most managed service providers, MSSPs bring economies of scale and thus are often able to provide cybersecurity capabilities at a price that's lower than what an in-house security team would cost.
- Fixed or nearly fixed costs. Going to an MSSP can switch big chunks of the security budget from Capex to Opex, which can afford certain accounting advantages for the organization and create predictability in the budgeting process.
- 24/7 year-round coverage. Most organizations, particularly those in the small to midsize category, can't afford to build out a round-the-clock security operations center. But, because of their larger size, MSSPs can attract and afford the talent needed for nonstop operations.
- Reliability and sustainability. Due to their larger size, MSSPs can also typically handle turnover more easily, whereas an organization with only an in-house security team "can get blindsided when one or two of their key people leave," said Alan Brill, a senior managing director in the cyber-risk practice at Kroll.
- Quicker path to maturity. "You get to leapfrog forward a lot of capabilities by bringing in an organization that's already matured them," said Rick McElroy, principal cybersecurity strategist at Broadcom's Carbon Black business unit.
- Threat detection and response. MSSPs can provide better insights into existing and emerging threats and how to detect and defend against them. "Service providers have larger data sets, so they should have better intelligence," McElroy explained.
- More experience than a typical in-house team. "An external organization handles far more alerts and breaches than a typical in-house organization will, so their level of experience tends to be better," Brill said. "Because of that experience, an external organization, in many cases, can do a more nuanced job of turning an alert into an actionable recommendation."
- Broader experience. Outsourcing providers commonly work in different vertical industries and with companies of different sizes, which gives them a wide breadth of experience that they can use to advise clients. "They generally have really good wisdom and guidance to help set a strategic vision," McElroy said.
- Continuity. Gartner predicted in February 2023 that nearly half of CISOs and other cybersecurity leaders will change jobs by 2025, due partly to the stress of their roles. A multiyear contract with an MSSP can deliver stable services and continuity of operations even when senior security leadership changes within an organization.
- Early warnings on emerging threats. "Many outsourcing companies have arrangements with major software vendors," Brill noted. "So, as zero days and other threats emerge, they're usually the ones who receive that information right upfront."
- Documented compliance with security standards. Cyber insurance providers, business partners and even customers are increasingly looking for proof that an organization has satisfied certain compliance requirements and implemented cybersecurity standards. An MSSP "represents more of a known," Brill said, and can often confirm to those third parties that security best practices are in place and being followed.
- In-depth knowledge of regulatory requirements. Since they have broader experiences, many MSSPs provide a thorough knowledge of varying state, national and international regulations, including GDPR, HIPAA and SOC 2. "That's the business of the right provider," said Tony Coulson, executive director of the Cybersecurity Center and a professor in the Jack H. Brown College at California State University, San Bernardino.
- Earlier implementation of emerging technologies. Outsourcing providers are more incentivized to pilot -- and can more readily afford -- new technologies, including AI tools for cybersecurity, that have the potential to deliver better results, said Rahul Mahna, a partner and head of the outsourced IT services team at consulting and auditing firm EisnerAmper.
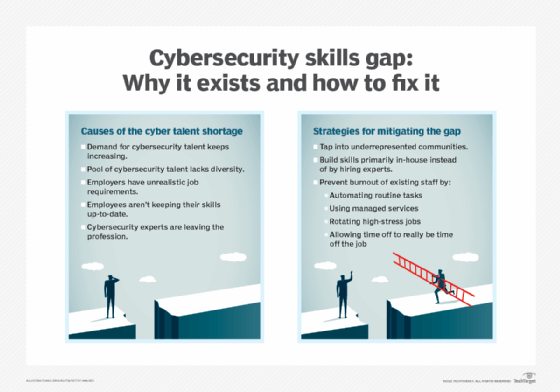
- Better access to talent. "Oftentimes, enterprise service providers are more capable in being able to hire cybersecurity talent, and they have partnerships and can reach into colleges and universities," Coulson explained. Considering the overall shortage of needed cybersecurity workers, outsourcing might be the only way an organization can fill the gap and get the skills it requires, he added.
- More cybersecurity specialists. MSSPs can also afford to have more specialized talent on staff to work across multiple clients that individually might not have enough work to justify the cost of specialists on their own staff.
Potential drawbacks of outsourcing cybersecurity
Although hiring an MSSP can bring many benefits, outsourcing cybersecurity services can have drawbacks, especially if company executives don't carefully consider what they're outsourcing and how they structure the MSSP contracts. Here are some of the potential drawbacks:
- Insufficient understanding of the organization's unique needs and internal culture, which could greatly influence risk tolerance, security requirements and user security needs.
- Limited or no cost savings if the relationship isn't well managed -- not what's typically expected with outsourcing.
- High rotation of external workers if the outsourcing provider makes frequent changes to contractor assignments.
- An overly generic approach to cybersecurity that doesn't include enough customization to fit all the organization's needs.
4 best practices for outsourcing cybersecurity
To maximize the benefits and minimize the drawbacks of hiring an MSSP, experts advised companies to do the following:
- Take a targeted approach to outsourcing cybersecurity by thoroughly evaluating security requirements and outsourcing only what the organization can't, doesn't want to and shouldn't perform in-house.
- Vet potential providers and select an MSSP with the experience and expertise that match the company's specific needs.
- Craft SLAs tailored to the organization's security requirements.
- Build in flexibility so the MSSP can scale services up and down to accommodate changing organizational needs.






