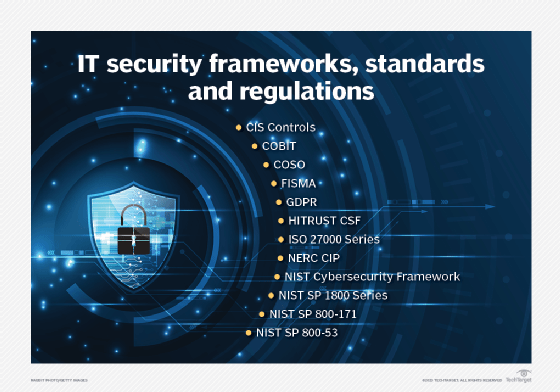
Top 12 IT security frameworks and standards explained
Several IT security frameworks and cybersecurity standards are available to help protect company data. Here's advice for choosing the right ones for your organization.
Information security management encompasses many areas -- from perimeter protection and encryption to application security and disaster recovery. IT security is made more challenging by compliance regulations and standards, such as HIPAA, PCI DSS, Sarbanes-Oxley Act and GDPR.
This is where IT security frameworks and standards are helpful. Knowledge of regulations, standards and frameworks are essential for all infosec and cybersecurity professionals. Compliance with these frameworks and standards is important from an audit perspective, too.
To help manage the process, let's look at what IT security standards, regulations and frameworks are, as well as a few of the more popular options to choose from and how they are used.
What are IT security standards and regulations?
Standards are like a recipe; they list out steps to perform. A well-managed IT organization must comply with requirements set forth in a standard.
Regulations, in contrast, have a legal binding impact. The way they describe how to do something indicates government and public support for the rules and processes set forth in the regulation. Failure to comply with IT-focused regulations can result in financial penalties and litigation.
What is an IT security framework?
An IT security framework is a series of documented processes that define policies and procedures around the implementation and ongoing management of information security controls. These frameworks are a blueprint for managing risk and reducing vulnerabilities.
Information security professionals use frameworks to define and prioritize the tasks required to manage enterprise security. Frameworks are also used to help prepare for compliance and other IT audits. The framework must, therefore, support specific requirements defined in the standard or regulation.
Organizations can customize frameworks to solve specific information security problems, such as industry-specific requirements or different regulatory compliance goals. Frameworks also come in varying degrees of complexity and scale. Today's frameworks often overlap, so it's important to select a framework that effectively supports operational, compliance and audit requirements.
Why are security frameworks important?
Frameworks provide a starting point for establishing processes, policies and administrative activities for information security management.
Security requirements often overlap, resulting in "crosswalks" that can be used to demonstrate compliance with different regulatory standards. For example, ISO 27002 defines information security policy in Section 5; Control Objectives for Information and Related Technology (COBIT) defines it in the "Align, Plan and Organize" section; the Committee of Sponsoring Organizations of the Treadway Commission (COSO) framework defines it in the "Internal Environment" section; HIPAA defines it in the "Assigned Security Responsibility" section; and PCI DSS defines it in the "Maintain an Information Security Policy" section.
Using a common framework, such as ISO 27002, an organization can establish crosswalks to demonstrate compliance with multiple regulations, including HIPAA, Sarbanes-Oxley Act (SOX), PCI DSS and Graham-Leach-Bliley Act.
How to choose an IT security framework
The choice to use a particular IT security framework can be driven by multiple factors. The type of industry or compliance requirements could be deciding factors. Publicly traded companies, for example, may wish to use COBIT to comply with SOX, while the healthcare sector may consider HITRUST. The ISO 27000 series of information security frameworks, on the other hand, is applicable in public and private sectors.
While ISO standards are often time-consuming to implement, they are helpful when an organization needs to demonstrate its information security capabilities via ISO 27000 certification. While NIST Special Publication (SP) 800-53 is the standard required by U.S. federal agencies, it can be used by any organization to build a technology-specific information security plan.
These frameworks help security professionals organize and manage an information security program. The only bad choice among these frameworks is not choosing any of them.
Examples of IT security standards and frameworks
1. ISO 27000 series
The ISO 27000 series was developed by the International Organization for Standardization. It is a flexible information security framework that can be applied to all types and sizes of organizations.
The two primary standards -- ISO 27001 and 27002 -- establish the requirements and procedures for creating an information security management system (ISMS). Having an ISMS is an important audit and compliance activity. ISO 27000 consists of an overview and vocabulary and defines ISMS requirements. ISO 27002 specifies the code of practice for developing ISMS controls.
Compliance with ISO 27000 series standards is established through audit and certification processes, typically provided by third-party organizations approved by ISO and other accredited agencies.
The ISO 27000 series has 60 standards covering a broad spectrum of information security issues, for example:
- ISO 27018 addresses cloud computing.
- ISO 27031 provides guidance on IT disaster recovery programs and related activities.
- ISO 27037 addresses the collection and protection of digital evidence.
- ISO 27040 addresses storage security.
- ISO 27799 defines information security in healthcare, which is useful for companies that require HIPAA compliance.
2. NIST SP 800-53
NIST has developed an extensive library of IT standards, many of which focus on information security. First published in 1990, the NIST SP 800 series addresses virtually every aspect of information security, with an increasing focus on cloud security.
NIST SP 800-53 is the information security benchmark for U.S. government agencies and is widely used in the private sector. SP 800-53 has helped spur the development of information security frameworks, including NIST Cybersecurity Framework (NIST CSF).
3. NIST SP 800-171
NIST SP 800-171 has gained popularity due to requirements set by the U.S. Department of Defense regarding contractor compliance with security frameworks. Government contractors are a frequent target for cyber attacks due to their proximity to federal information systems. Government manufacturers and subcontractors must have an IT security framework to bid on federal and state business opportunities.
Controls included in the NIST SP 800-171 framework are directly related to NIST SP 800-53 but are less detailed and more generalized. It's possible to build a crosswalk between the two standards if an organization must show compliance with NIST SP 800-53, using NIST SP 800-171 as the base. This creates flexibility for smaller organizations -- they can show compliance as they grow using the additional controls included in NIST SP 800-53.
4. NIST CSF
NIST Framework for Improving Critical Infrastructure Cybersecurity, or NIST CSF, was developed under Executive Order 13636, released in February 2013. It was developed to address U.S. critical infrastructure, including energy production, water supplies, food supplies, communications, healthcare delivery and transportation. These industries must maintain a high level of preparedness, as they have all been targeted by nation-state actors due to their importance.
Unlike other NIST frameworks, NIST CSF focuses on cybersecurity risk analysis and risk management. Security controls in the framework are based on the five phases of risk management: identify, protect, detect, respond and recover. Like all IT security programs, these phases require the support of senior management. NIST CSF is suitable for both public and private sectors.
5. NIST SP 1800 series
The NIST SP 1800 series is a set of guides that complement the NIST SP 800 series of standards and frameworks. The SP 1800 series of publications offers information on how to implement and apply standards-based cybersecurity technologies in real-world applications.
The SP 1800 series publications provide the following:
- Examples of specific situations and capabilities.
- Experience-based, how-to approaches using multiple products to achieve the desired result.
- Modular guidance on implementation of capabilities for organizations of all sizes.
- Specifications of required components and installation, configuration and integration information so organizations can easily replicate the process themselves.
6. COBIT
COBIT was developed in the mid-1990s by ISACA, an independent organization of IT governance professionals. ISACA offers the well-known Certified Information Systems Auditor and Certified Information Security Manager certifications.
COBIT originally focused on reducing IT risks. COBIT 5, released in 2012, included new technology and business trends to help organizations balance IT and business goals. The current version is COBIT 2019. It's the most used framework to achieve SOX compliance. Numerous publications and professional certifications address COBIT requirements.
7. CIS Controls
Center for Internet Security (CIS) Critical Security Controls, Version 8 -- formerly the SANS Top 20 -- lists technical security and operational controls that can be applied to any environment. It does not address risk analysis or risk management like NIST CSF; rather, it is solely focused on reducing risk and increasing resilience for technical infrastructures.
The 18 CIS Controls include the following:
- Inventory and Control of Enterprise Assets.
- Data Protection.
- Audit Log Management.
- Malware Defenses.
- Penetration Testing.
CIS Controls link with existing risk management frameworks to help remediate identified risks. They're useful resources for IT departments lacking technical information security experience.
8. HITRUST Common Security Framework
HITRUST Common Security Framework (CSF) includes risk analysis and risk management frameworks, along with operational requirements. The framework has 14 different control categories and can be applied to almost any organization, including healthcare.
HITRUST CSF is a massive undertaking for any organization due to the heavy weight given to documentation and processes. As a result, many organizations end up scoping smaller areas of focus for HITRUST. The costs of obtaining and maintaining HITRUST certification add to the level of effort required to adopt this framework. The certification is audited by a third party, which adds a level of validity.
9. GDPR
GDPR is a framework of security requirements that global organizations must implement to protect the security and privacy of EU citizens' personal information. GDPR requirements include controls for restricting unauthorized access to stored data and access control measures, such as least privilege, role-based access and multifactor authentication.
10. COSO
COSO is a joint initiative of five professional organizations. Its Internal Control -- Integrated Framework, released in 1992 and updated in 2013, helps companies achieve a risk-based approach for internal controls. It covers the following five components:
- Control environment.
- Risk assessment and management.
- Control activities.
- Information and communications.
- Monitoring.
COSO released its Enterprise Risk Management (ERM) -- Integrated Framework in 2004 and updated it in 2017. The framework, which aims to help organizations improve their cyber-risk management, covers 20 principles across the following five components:
- Governance and culture.
- Strategy and objective setting.
- Performance.
- Review and revision.
- Information, communication and reporting.
A guidance paper, "Managing Cyber Risk in a Digital Age," released in 2019, offers advice on how to prepare and respond to enterprise cyberthreats. It aligns with COSO ERM Framework.
11. FISMA
The Federal Information Security Modernization Act (FISMA), which aligns closely with NIST Risk Management Framework, provides a security framework for protecting federal government data and systems. Introduced in 2002 and updated in 2014, FISMA was suggested for an update in 2023; legislation is pending.
FISMA requires federal agencies and their third-parties, contractors and vendors to develop, document and implement security policies and practices, including the monitoring of their IT infrastructure and conducting regular security audits.
12. NERC CIP
North American Electric Reliability Corporation Critical Infrastructure Protection is a framework of 14 ratified and proposed standards that applies to utility companies within the bulk power system. The standards outline recommended controls and policies to monitor, regulate, manage and maintain the security of critical infrastructure systems.
CIP standards include the following:
- CIP-004-6 Cyber Security -- Personnel and Training.
- CIP-008-6 Cyber Security -- Incident Reporting and Response Planning.
- CIP-013-1 Cyber Security -- Supply Chain Risk Management.
- CIP-014-1 Physical Security.
Bulk power system owners, operators and users must comply with the NERC CIP framework.





