PKI (public key infrastructure)
What is PKI (public key infrastructure)?
PKI (public key infrastructure) is the underlying framework that enables entities -- users and servers -- to securely exchange information using digital certificates. The entities that facilitate and use PKI typically involve general internet users, web clients or browsers, and company servers -- though this can extend to other virtual machines (VMs) as well.
The word infrastructure describes PKIs since it does not refer to one single physical entity. Instead, it refers to the components used to encrypt data and authenticate digital certificates. These components include the hardware, software, policies, procedures and entities needed to safely distribute, verify and revoke certificates.
In technical terms, PKI is a two-key asymmetric cryptosystem that supports various information technology (IT) systems in their pursuit of high-level information confidentiality, encryption and confidence. The two keys, in this case, are also the two main pieces that facilitate this secure data management: a public key and a private key.
Digital keys are like regular keys, except they are used to lock and unlock digital materials. In this case, lock describes encryption. Encryption is the process by which digital information is scrambled to protect it from unauthorized viewers. By using a key, users can lock and unlock data as they please. The unique part about keys is that they can also be shared with others. If someone accessed another person's digital key, they would be able to decrypt their encrypted data and messages. PKI involves the use of two digital keys to ensure the safety of the entities and data involved.
How PKI works
Imagine that person A wants to send person B an encrypted message over the internet. One way to secure this exchange is by using PKI. If person A chooses to use PKI, they will first need person B's public key before they can send a message. A public key enables any user to encrypt information for a specified entity. The only way to decrypt a public key is by using its respective private key.
| Public key features |
Private key features |
| Used to encrypt data |
Used to decrypt data |
| Can be distributed and used by anyone |
Should not be distributed or shared |
| Can only be decrypted with the associated private key |
Can only decrypt information encrypted by associated public key |
| Not a secret |
Is a secret |
Person B, in this example, provides person A with one of their two keys, the public key. Person A then uses this key to encrypt the message, data or digital materials they want to send. Once encrypted and sent, person B can decrypt and access the information using their private key. This is the simplest form of PKI's two-key asymmetric cryptosystem. However, this is usually not sufficient for securing a digital conversation between two entities.
Other systems need to be put in place to verify the identity of the entities or users involved -- systems that would be able confirm that the public key being sent to them belongs to their intended recipient. Without additional security measures, entities may engage in sensitive data exchanges with users pretending to be people they aren't. Such an outcome would undermine the security, confidentiality and confidence of the entire interaction. This is where digital certificates come into play.
Elements of PKI
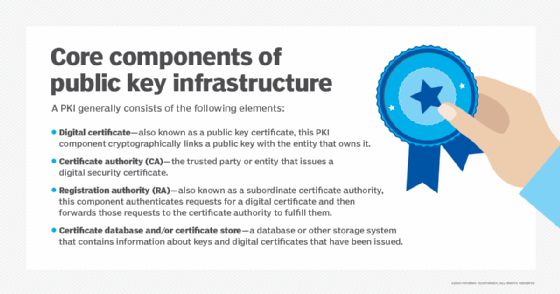
A typical PKI includes the following key elements:
- Certificate authority. A trusted party provides the root of trust for all PKI certificates and provides services that can be used to authenticate the identity of individuals, computers and other entities. Usually known as certificate authorities (CAs), these entities provide assurance about the parties identified in a PKI certificate. Each CA maintains its own root CA, for use only by the CA.
- Registration authority. This is often called a subordinate CA and issues PKI certificates. The registration authority (RA) is certified by a root CA and is authorized to issue certificates for specific uses permitted by the root.
- Certificate store. This is usually permanently stored on a computer but can also be maintained in memory for applications that do not require that certificates be stored permanently. The certificate store enables programs running on the system to access stored certificates, certificate revocation lists (CRLs) and certificate trust lists (CTLs).
- Certificate database. This database stores information about issued certificates. In addition to the certificate itself, the database includes the validity period and status of each PKI certificate. Certificate revocation is done by updating this database, which must be queried to authenticate any data digitally signed or encrypted with the secret key of the certificate holder.
What is a PKI certificate?
A PKI certificate -- or digital certificate -- is a data package that authenticates the identity of the server associated with the public key. This package includes a variety of digital files, documents and cryptographic data used to validate an entity's identity. In simple terms, a PKI certificate is like a digital passport. To send information using PKI, users need to be able to verify who they are and who their recipient is.
It helps to think of PKI like an airport: It is the infrastructure that enables individuals to safely travel from one place to another. In the case of PKI, the traveler is the data or message that is supposed to be sent, and the two parties are the arrival and departure terminals. For data to board the plane, it needs to first go through customs. The PKI equivalent of customs involves servers and clients validating each other's passports or digital certificates prior to the exchange. However, this still provides users with an opportunity to manipulate the digital certificate. To avoid additional opportunities for corruption, PKIs often require additional verification. Digital certificates, like passports, need to be issued by credible institutions to confirm their legitimacy.
How to obtain a digital certificate
The easiest way to obtain a digital certificate is to get one made and signed by a publicly trusted CA -- such as Sectigo or DigiCert -- that issues, distributes and revokes digital certificates to various entities based on country- or company-specific legislation. Individual companies can use their own in-house CA system if they believe they require an added level of security and/or have the necessary infrastructure to support it.
After a digital certificate is issued, it can be distributed by anyone to anyone, not unlike a public key. This is because a digital certificate can be individually validated, as it contains no private information. Most digital certificates are implicitly trusted by client software, such as web browsers, and don't require additional validation.
When is PKI required?
One of the most common applications of the PKI framework is Secure Sockets Layer (SSL) protocols. SSL -- and its successor, Transport Layer Security (TLS) -- help establish the authenticated and encrypted links between different networked computers used in PKI. The applications of these protocols can extend to a number of activities, most of which are browser-related. Below are a few of the modern uses of PKI:
- digital signature software/applications
- email encryption
- internet of things (IoT) security
- network security
- server-hosted communication protection
- password recovery
- file description
- smart card authentication
- web communications security
Problems with PKI
PKI provides a chain of trust so that identities on a network can be verified. However, like any chain, PKI is only as strong as its weakest link. There are various standards that cover aspects of PKI -- such as the Internet X.509 PKI Certificate Policy and Certification Practices Framework, or Request for Comments (RFC) 2527.
The CA/Browser Forum is an industry consortium founded in 2005 whose members include CAs, browser software publishers and other system providers that use X.509 digital certificates for encryption and authentication. The CA/Browser Forum publishes guidelines and best practices for CAs, browser and other parties involved in PKI as it relates to the use of digital certificates.
Although a CA is often referred to as a trusted third party, shortcomings in the security procedures of various CAs in recent years have jeopardized trust in the entire PKI on which the internet depends. If one CA is compromised, the security of the entire PKI is at risk. For example, in 2011, web browser vendors were forced to place all certificates issued by Dutch CA DigiNotar on a blocklist after discovering more than 500 fake certificates.
In 2017, Google engineers identified problems with certificates issued through Symantec's CA business, which led to subsequent distrust of certificates issued by Symantec prior to the sale of its CA business to DigiCert.






