Hash-based Message Authentication Code (HMAC)
What is Hash-based Message Authentication Code (HMAC)?
Hash-based Message Authentication Code (HMAC) is a message encryption method that uses a cryptographic key in conjunction with a hash function. It provides the server and the client each with a private key that is known only to that specific server and client, providing a more secure means of encrypting data than a simple Message Authentication Code (MAC).
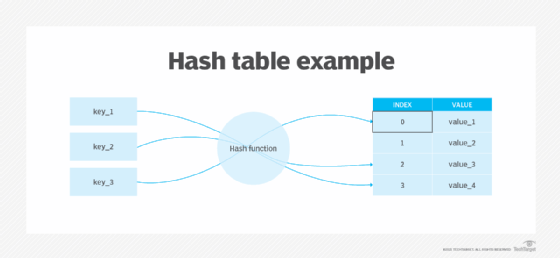
HMAC is a technique for cryptographic authentication. It uses both a cryptographic hash function and a shared secret key to encrypt information and protect it from unauthorized access. A hash function is an algorithm or mathematical function that converts a message that consists of a variable number of characters into a string with a fixed number of characters. The output value is known as the message digest, hash value or simply hash. The secret cryptographic key is what enables a user to make an encrypted message readable after it has been encrypted by an algorithm.
In an HMAC transaction, the client and server must agree on the secret key. This provides a way to decode messages, which must stay secret, to maintain the transaction's integrity. The parties must also choose and agree on the hash function for their messages.
HMAC can be used to check for data integrity and to authenticate the parties involved in a transaction. Many communication and transfer protocols use HMAC, including HTTPS, SFTP and FTPS. The cryptographic hash function in HMAC is typically SHA-1, SHA-256, MD5 or RIPEMD-128/160.
How Hash-based Message Authentication Code works
HMAC provides a valid and reliable way for transacting parties to ensure that their messages have not been tampered by an unauthorized or malicious party, also referred to as a threat actor. The HMAC code or key consists of two parts:
- A shared set of cryptographic keys for the sender (client) and recipient (server). The sender and recipient use the same key to generate and verify the HMAC.
- A generic cryptographic hash function, like SHA-1 or RIPEMD-128/60.
The formula for HMAC is represented as the following:
HMAC = hashFunc(secret key + message)
In a messaging transaction between a client and a server involving HMAC, the client creates a unique HMAC or hash by hashing the request data with the private keys and sending it as part of a request. The server receives the request and regenerates its own unique HMAC. It then compares the two HMACs. If they are equal, the client is trusted and considered legitimate, and the request is executed. This process is often called a secret handshake.
Security in Hash-based Message Authentication Code
HMAC is more secure than MAC because the key and the message are hashed in separate steps:
HMAC(key, msg) = H(mod1(key) || H(mod2(key) || msg))
The client first hashes the data with a private key and sends it as a part of the request to the server. The server then makes its own HMAC. This ensures the process is not susceptible to extension attacks that can cause elements of the key to be leaked as successive MACs are created.
Also, once the process is complete, the sent message becomes both irreversible and resistant to hacking. Even if a malicious party tries to intercept the message, they won't be able to guess its length or decrypt it because they won't have the decryption key. In effect, the HMAC process renders the message contents unreadable and useless to the hacker.
Applications and benefits of HMAC
HMAC is considered a secure method to authenticate messages because it is difficult to forge if the potential forger doesn't know the secret shared key. The method is also resistant to dictionary attacks, where an attacker uses brute force to decode their way into a password-protected device by running through common words and phrases in a dictionary. That said, it's important to use a strong and unique secret key to maximize the security benefits of HMAC.
Since HMAC provides dual levels of protection, it is ideal for applications involving sensitive data, like personally identifiable information or credit card numbers. It provides more extensive security than traditional measures, making it suitable for use in regulated industries, like healthcare or finance.
HMAC encryption is also suitable for internet of things environments, high-performance systems like routers and verification of a user's email address. HMACs can also be used in security-critical applications where public key systems are either inadequate or prohibited. Possible applications include the following:
- Authenticate form data sent to a client browser and resubmit.
- Generate secure hashes for storing passwords.
- Generate unique session management tokens.
Hash-based Message Authentication Code vs. digital signature
A digital signature is a way to validate the authenticity and integrity of a digital document and sender with the help of asymmetric public key cryptography. Like HMACs, digital signatures also employ a hash function and a shared key. However, HMACs use a symmetric key -- i.e., the same key is shared between the sender and recipient -- while a digital signature uses asymmetric keys, meaning the sender and recipient use two different keys.
Both HMACs and digital signatures ensure the integrity and authenticity of the message. Integrity means that the message has not been altered. If it is, the hash function gives a different value in return, so the recipient knows that someone has tampered with the message. Authenticity indicates that the recipient is confident that the message originates from the sender. Both methods ensure integrity and authenticity because the keys that encrypt the hash are unknown to a third party -- who may be a malicious adversary -- thus proving to the recipient that the message came from the expected sender.
In addition to ensuring integrity and authenticity, digital signatures are also used for nonrepudiation, which means that neither the sender nor recipient can deny having processed the information once it has been sent. HMACs are generally not used for nonrepudiation purposes.
See how MAC and HMAC use hash function encryption for authentication, and learn the differences between symmetric vs. asymmetric encryption.






