timing attack
What is a timing attack?
A timing attack is a type of side-channel attack that exploits the amount of time a computer process runs to gain knowledge about or access a system. There are practical implementations of timing attacks against some encryption methods.
How do timing attacks work?
Timing attacks measure how long a computer takes to perform a certain operation to gain knowledge about the data the system is working on. While there are many factors that can influence processing time, the attacker can take many measurements to determine an average time. Even partial knowledge of the data can make traditional brute-force attacks more effective. Statistical models and machine learning can take partial knowledge from a timing attack to reproduce the data.
Some timing attacks exploit race conditions, where two things are happening simultaneously, and the outcome changes depending on which finishes first. The attacks exploited a race condition to access data that the attacker was not permitted to obtain.
Timing attacks are difficult to implement but they can be exploited successfully. This is because they often target high-value data such as encryption keys, cryptography, passwords, or API keys. They often leave no trace on the compromised system so the attacker may have ample time to implement the attack.
Example timing attacks
Most users and programmers want their computers to run as fast as possible. So programs are optimized for speed. Making the program run as fast as possible can sometimes reveal information about the system to a careful attacker.
Imagine a website that used a character string to validate the user with a password or an API key. The system would take 10 ns (nanoseconds) to validate each correct letter and would immediately stop reading any other characters the moment it encountered an incorrect one. This system would be quite fast but vulnerable to a timing attack. A determined attacker could send attempts changing one character each time and measure how long it took to get a reply. Using the precise timings of replies and averaging out the results, the attacker could eventually narrow down to the correct string with much fewer attempts than with a brute-force method.
One mathematical function used in Diffie-Hellman key exchange and RSA keys is linearly time-dependent on how many 1s are in the binary string to calculate. This can reveal how many 1s there are in the binary number, but not how many 0s. While this doesn't directly reveal the key, if an attacker can observe enough encrypted data, it can yield additional information to help crack the encrypting used.
The Spectre and Meltdown attacks exploit a race condition in modern processors to perform a timing attack to read cache memory that the attacking program should not have access to. Because modern CPUs are so fast and memory is relatively slow, they begin to pre-cache data it predicts will be called even before the calling functions are finished. Exploiting this, the attacker makes a call to data that it does not have access to, then reads the pre-cache before the calling function has time to finish and determines that it does not have permission to the data.
How to protect against timing attacks
The best way to protect against timing attacks is to keep systems and software up to date. This includes updating dependencies and open source products. As new attacks are developed, programmers and vendors will update their products to be resistant to them. Attackers can leverage timing attacks against known vulnerable software versions.
Do not disclose information about systems or software. While security through obscurity is not a good primary defense, it is still good practice as part of an overall strategy. An attacker could use knowledge about the hardware or software to find known timing attacks or target the specific system to develop a novel attack.
Timing attacks against public systems often require many attempts to collect enough information. Implementing rate limiting or fail-to-ban systems can prevent the attacker from collecting enough data to execute a timing attack.
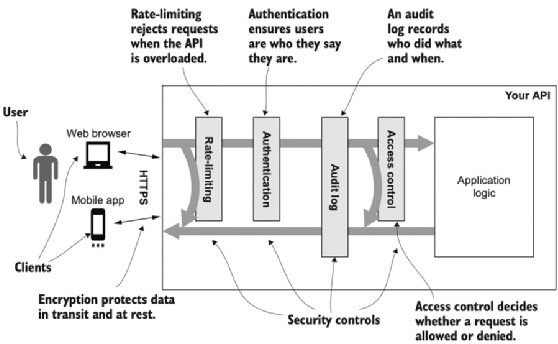
Programmers should identify security critical functions and create them to be constant time. This may result in slightly slower program execution but will eliminate the opportunity for a timing attack. Another option is to insert random timing jitter into a program's execution.
Check out the ultimate guide to cybersecurity planning for businesses. See why experts warn cryptography techniques must keep pace with threats and explore the importance of security and data encryption in the cloud. Learn about the different kinds of hackers and how to fix the top five cybersecurity vulnerabilities.







