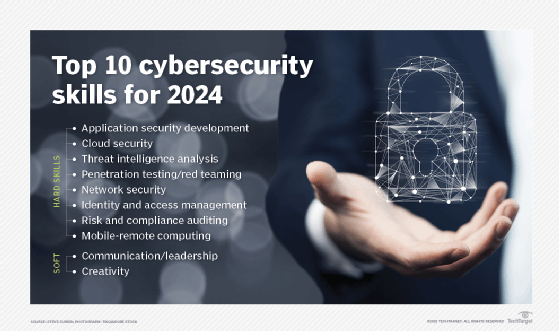
10 must-have cybersecurity skills for career success in 2024
Looking to advance your cybersecurity career? Here are the skills you'll need to win that CISO job, land a gig as a threat hunter and snag other security positions in high demand.
The talent shortage in cybersecurity shows little sign of abating. Research from TechTarget's Enterprise Strategy Group and the Information Systems Security Association found that 95% of respondents said the cybersecurity skills shortage and its associated impacts have not improved over the past few years, while 44% said it has only gotten worse.
Moreover, more than half of organizations polled (57%) said the skills shortage is taking a toll on their current workforces, citing increased workloads (62%), unfilled open job requisitions (38%) and high burnout among staff (38%) as concerning issues.
While the cyber skills shortage presents all sorts of headaches for IT security leaders and the companies they aim to protect, the demand for cybersecurity experts offers tremendous opportunities for security professionals.
Here are the technical skills and soft skills that security industry professionals said are the most important for building a successful career -- and for putting organizations in the best position to remain effective.
Top technical skills needed to advance your cybersecurity career
- Application security development. Companies need security people who are skilled in DevSecOps concepts and can work closely with the software development engineering teams. Communication skills are important here because engineering departments are often focused on getting a product out the door or on the product's functionality versus its security. People interested in this area, therefore, need to be flexible because application security development often falls under business units outside the security team's direct control. In addition, security professionals are often primarily focused on keeping the bad guys out rather than on building security into products from the get-go. Honing your skills in application security development requires adapting to a new security mindset and culture.
- Cloud security. As more companies look to cloud infrastructure to store data and run applications, they need people who understand the underlying infrastructure and how to tie identity management and authentication to running basic SaaS applications securely. Many cloud breaches happen because of fake pages set up where credentials are stolen. Companies need people who are familiar with these tactics and can manage the cloud security tools that monitor and identify these kinds of schemes. As companies adopt multi-cloud strategies, they also need people who understand how to use the new tools designed to work across multiple public cloud platforms.
On the business side, companies also need people who understand the contract clauses in agreements with the vendors that offer these cloud services; in particular, cloud security experts need to understand the company's responsibility for security in the vendors' shared responsibility agreements. People with experience managing the big platforms -- such as AWS, Microsoft Azure and Google Cloud Platform -- are in high demand. - Threat intelligence analysis. There are any number of threat intelligence tools on the market, but people who can use the tools properly and contextualize and analyze security threat trends are in short supply. Companies tend to have a hard time finding people with this talent -- and an even harder time training them. The job requires strong analytical skills, curiosity and the ability to handle high-stakes pressure. Threat intelligence experts are skilled in analyzing digital forensics. They often have some programming skills, especially in Python. Security people interested in this area can develop experience working on incident response teams, where many of these skills also come into play. There is also a growing need in this area for people who understand the threats affecting machine learning and AI environments.
- Penetration testing/red teaming. People with pen testing/red teaming skills are offensive security types: experts who can go into companies and tell them what's broken and how to fix it. It takes several years of training and experience to do this work well, and that's why companies have a hard time finding these people. The best pen testers believe that they can hack anything. It takes a lot of confidence and bravado, but it also requires a lot of skill that's gained in the classroom, in hands-on seminars and on the job. There's also an increased need for blue teamers, or people who work as defenders.
- Network security. Network security skills are basic skills that everyone in the security field should have. Some of the best security people come from a network security background. This is precisely because the basics of security stem from understanding how networks work: You can't defend networks if you don't understand how routers work, know what the firewall logs mean or haven't mastered the fundamentals of intrusion detection and prevention. Many would argue that the best career track for security professionals is to start in computer support, then work as a network administrator and build security skills over time from there.
- Identity and access management. The vast majority of breaches -- more than 80% -- are caused by compromised, weak and reused passwords. Once again, communication skills are important. Companies need security professionals who can explain the threats to people and teach them how they can improve their password practices by using Google Authenticator, Authy or other passwordless tools -- fingerprints, face IDs and retina scans, for example -- in their daily work lives. Companies also need people who can manage identity and access management tools and know how to set network privileges and manage them properly so the organization stays vigilant against intruders. Experts in this area must be able to define levels of access to certain data sets and set privileges tailored to employee roles and responsibilities.
- Risk and compliance auditing. The skills required in this area depend in part on the industry or part of the business you work in. Companies focused on e-commerce need people who understand how to comply with PCI DSS regulations; just about every type of organization, on the other hand, has to deal with HIPAA compliance for sensitive medical data. Organizations also need people who are familiar with the various data privacy regulations, whether they are based on the European Union's GDPR or the California Consumer Privacy Act. Companies need people who can assess the noncompliance risks and understand what paperwork to file and which security protocols to put in place to comply with the regulations.
- Mobile-remote computing. Many companies have found that the work-from-home model works well for them, so security teams continue to need people who understand how to manage VPNs and RDP servers and work with people on how to segment their home networks for greater security.
Strategies for addressing the cybersecurity skills shortage
As the competition for cybersecurity professionals grows more intense, companies must look for new ways to plug the skills gaps in their existing workforce, two cybersecurity experts said.
Simone Petrella, CEO at cybersecurity workforce development company CyberVista, said the most effective CISOs today view themselves as "workforce architects." This means they take the time to evaluate the skills required to keep pace with current security needs compared with the skill maturity and competence of their existing workforce and hire or train strategically to plug the holes.
Candy Alexander, board president of the Information Systems Security Association and CISO at NeuEon, agreed that, while organizations are acutely aware of the cyber skills talent shortage, many have failed to adjust their hiring and training strategies. "We are still pleading for organizations to look at not just experience, but also skill sets," she said.
Organizations like ISSA have been urging security leaders for years to identify and pull in talent from other parts of the company, she said. "For example, a data analyst deals with data -- and security is all about the data. We have been talking about cross careers for years, and organizations are starting to recognize talent in other parts of the company that they can pull in."
All-important soft skills to advance your cybersecurity career
- Communication/leadership. Experts in the security training field say that soft-side communication and leadership skills are sorely lacking in the security business. Of course, this has always been an issue in the technology field, but it's become more important in business today because security experts have to develop an ability to explain technical concepts in ways that businesspeople understand. The most talented threat hunters or red teamers won't advance their careers if they can't explain basic security concepts to business leaders. That means avoiding in-the-weeds analyses of the impact of intrusion attempts or security incidents on KPIs in favor of plain talk: Explain to top management what the risks are to the company's sales, profits and reputation if it is hit with a data breach.
- Creativity. While the least technical skill, creativity is the one intangible that can catapult people to the top of their cybersecurity careers. Creative security people are able to "think like a hacker," entertaining many what-if scenarios and staying one step ahead of the cybercriminals. Sometimes, the work is like an elaborate chess game. Sometimes, it's like a police stakeout, where hackers infiltrate the company's network for months and the security team just waits for them to make their move. Other times, it's understanding that some hackers are lazy and just go for the low-hanging fruit. Whatever the criminal motivation is, great security people are able to figure it out. They feed their creativity by reading the latest cyber novels, keeping up on current affairs and social media trends, playing musical instruments, designing a video game, learning some of the basics of computer animation or getting involved in the community by coaching a sports team or working with kids. Interpreting logs and analytics charts, coding and developing hard skills core to a red team certainly open doors for you in cybersecurity, but having a creative streak and a curiosity about life and people takes you even further.
Meet the experts
Here are the industry experts who helped develop our security skills list:
- Candy Alexander, board president of ISSA International, and CISO, NeuEon.
- Ryan Corey, co-founder and former CEO, Cybrary.
- Brandon Hoffman, chief strategy officer at Intel 471.
- Jon Oltsik, distinguished analyst and fellow, Enterprise Strategy Group.
- Simone Petrella, founder and CEO, CyberVista.
- Lisa Plaggemier, executive director, National Cyber Security Alliance.
Steve Zurier is an independent freelance technology writer covering IT security, networking and cloud computing.






