alphaspirit - Fotolia
Social engineering: You got nailed!
Move beyond prevention to fast detection to combat a stealthy social engineering attack.
No prevention is 100% effective against the relentless social engineering attacks on enterprises. In 2014 alone, RSA pegs the cost of phishing attacks on global organizations at an astounding $4.5 billion in losses.
So what’s a beleaguered enterprise to do? Along with imparting a solid understanding of impersonation, elicitation and phishing -- and encouraging and rewarding employees for reporting any suspicious or odd activities -- it’s critical for security programs to start expanding beyond prevention.
Today enterprises “use a lot of physical security against social engineering and other threats,” says John Kindervag, Forrester Research vice president and principal analyst serving security and risk professionals. “If an attacker gets access to an internal network, it’s a successful attack -- no one monitors the internal network.”
One way to strengthen defenses beyond prevention strategies is by adopting data-centric detection approaches. Organizations are using automated detection and behavioral analytics to watch critical information and how it’s accessed -- when, where, why and by whom.
“All of information security is moving from prevention to detection, mainly because once a prevention system is defeated the attackers are in,” says Dan Kaminsky, co-founder and chief scientist of New York security firm White Ops, which specializes in deterministic botnet detection and sophisticated digital fraud prevention
Complex ‘dance’ of social engineering
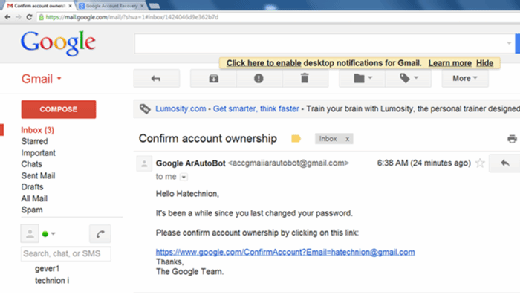
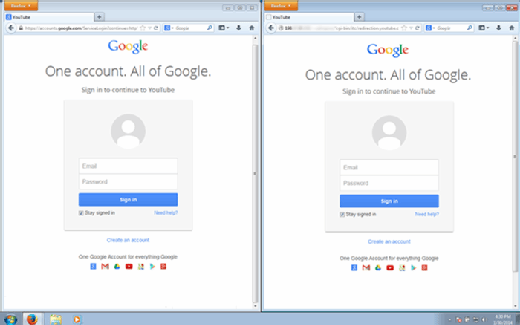
Email phishing campaigns targeting enterprises are easy to pull off, thanks to social media sites such as LinkedIn, which help attackers exploit the fact that employees tend to trust calls or links in emails from “co-workers.”
“A social engineer can go get a list of a company’s employees and then generate emails pretending to be from one employee to another, with irresistible bait like a video on YouTube,” says Tal Klein, vice president of strategy for cloud application security firm Adallom Inc., in Palo Alto, Calif. “They’re tying social elements to phishing, which makes it less likely to detect you’ve been compromised when you click a link.”
The cloud is another attack surface for social engineers who are looking to commit fraud. “Social engineering is more significant than any new virus or backdoor you can imagine,” Klein says. Adallom focuses on protecting enterprise employees from phishing and cloud account hijacking attacks, as well as protecting data files inside cloud services, by auditing and ensuring the data side is secure and encrypted and has an audit trail attached to it. Individual behavior can be monitored to establish a behavioral standard deviation, in a manner similar to how banks detect fraud, issuing challenges or alerts to users when unusual activity is detected.
Netskope and SkyHigh Networks are also offering services within this realm, although none of the three are using exactly the same techniques.
Social engineers are often extraordinarily skilled at tapping into and manipulating relative trust. “Nobody wants to be the person to step on someone else’s toes,” says Kaminsky, who is well-known within security circles for his research that exposed a DNS caching flaw. “So we’re always looking for our role to play, the appropriate thing we’re supposed to do based on however we’re interacting with someone.” And as humans, our default is usually to adopt a cooperative role, which social engineers are all too willing to exploit.
Enterprises are frequently targeted with calls to employees by social engineers -- a technique known as pretexting -- claiming to be the IT department: “I need your password to fix something of yours.” And employees give it up. “Then attackers use these credentials to break in and quickly have their beachhead into the system,” he says.
If companies want to lower their risks of becoming victims of social engineering, they need to make employees feel comfortable with slowing down extraordinary requests and validating them. “Make it culturally okay to check,” Kaminsky advises. “Take a moment to make sure someone who claims they work for IT actually does. … Say you’re going to send them a quick email and make sure they can read it. You’re not saying no; you’re saying wait a minute. Enterprises need a reporting framework for any weird calls or emails.”
Employees should also be encouraged to ask more questions, especially if they think something seems unusual or out of place. “Do we ever stop the UPS person with a package from just walking right into an office?” asks Klein. “No, we always trust the UPS person, or any man or woman in a uniform. We used to do red team data audit tests of data center security, and our goal was to walk into a data center and take our picture right next to our customers’ servers. … A janitor uniform makes it extremely easy.”
Faster detection and response
While employee awareness and education can help, enterprises clearly need to do more to stop the malware and other criminal activities that result from social engineering and phishing attacks.
Security vendors are rolling out breach detection systems designed to improve incident response times to help organizations keep pace with attackers. The technologies monitor network communications and use behavioral analytics to help security teams recognize and respond to potential threats.
Several of these vendors are striving to have their systems become big data analytics engines by providing the confidence to allow automation of the breach response. Some of the companies and products in this group include BAE Systems’ Applied Intelligence, CSG International, Damballa, IBM’s Q1 Labs, Intel/McAfee’s Nitro, LogRhythm and RSA Security Analytics. “If we don’t automate, we’ll never be able to respond to breaches fast enough,” says Kindervag.
“Forward-leaning CISOs and IT security teams are realizing the need to invest in the ability to detect and respond to attacks getting through -- that’s where automated breach detection systems can provide a platform that enables IT to detect and respond to attacks quickly,” says Brian Foster, CTO at Damballa Inc., in Atlanta. Automated breach detection systems can alert you to an infection that can lead to a breach -- within seconds and minutes of it occurring, rather than months afterward.
Damballa’s system, for example, analyzes inbound/outbound Internet traffic and doesn’t need to sit in the email stream per se, which is where most social engineering occurs through phishing. When the company studied customers’ data and the initial installment of malware over a six-month period, it discovered that 20% of files downloaded were from people clicking on malicious email links or inadvertently logging into bad websites. “So one in five was the direct result of social engineering,” Foster says.
Some of these technologies may ease the load for security teams. “We simply do not have the resources to identify, contain and remediate malicious attacks on our systems,” says an IT specialist for a Global 500 energy and utilities company that uses Damballa’s technology. “It has been key in identifying and containing those attacks until they can be remediated. And its custom threat module has finally allowed us to respond effectively to phishing attacks.”
Attackers want data
The real secret to protecting data against theft is by adopting a data-centric approach, which relies on securing sensitive data through encryption and other means. “This tends to protect against risks that are electronic digital hacking versus physical risks of someone social engineering their way into your data center and stealing backup tapes,” Kindervag says.
A data-centric strategy is also conducive to big data environments, because it doesn’t rely on perimeters to contain the data.
The data-driven security process hinges on getting to know your enterprise assets and classifying the data. “CISOs and CIOs need to identify what their key data is -- such as intellectual property -- and the IT systems that support it, as well as any risks to the data and systems,” explains Foster. “Once you understand this, simple calculations help to figure out how to mitigate the risks … and the costs involved. Then you go invest where it makes sense.”
While data classification is no small task, expensive breach cleanups and damaged reputations can be more costly than making the effort to mitigate risks.
“This whole digital life of ours is less than a century old, so it’s difficult to think about our digital assets as being physical assets,” says Adallom’s Klein. “An incremental change in contextual awareness would make a hacker or social engineer’s job much more difficult. We need to treat our digital life with the same scrutiny we treat our physical life.”
Cloud service providers “do a great job of securing their infrastructure, which was proven time and time again in the breaches of last year,” he says. “But none of our existing enterprise controls are effective at protecting data inside the cloud.” Firewalls, antivirus and intrusion prevention systems just aren’t effective when users are interacting with data in the cloud from unmanaged devices over public networks. “Putting your data in cloud services like Box, Google Drive or Cloud 365 is actually a lot more secure than on-premises data storage,” he adds.
Expect to see more companies come out of stealth mode with automated breach detection offerings in 2015. “This will be a huge cultural shift in the security world, which is very concerned with change,” Kindervag points out. “But attackers aren’t constrained by the same things that we are, so we need to become much more agile to win this battle.”
The big three
Earlier detection strategies may help organizations that have relied on prevention approaches, which are clearly not effective. However, the three biggest problems in security have helped to create a perfect storm for social engineering. “We can’t authenticate, we can’t write secure code, and we can’t bust the bad guys,” says Kaminsky. “It’s not absolutely impossible, but … we can’t do any of the three in a way that will scale. And all three of these problems translate to social engineering.”
The biggest factor fueling social engineering today is “a lack of consequences for the criminals,” he adds. If you can’t punish the violator of social rules, society will punish the victim, because they want to establish that the victim is unique in some way: That’s why they got hit and we didn’t. “No one talks about this, but everyone knows it,” Kaminsky says. Be sure this doesn’t happen to employees reporting social engineering; reward them instead.
Sally Johnson is a freelance technology and science journalist. Previously, she was the features writer for TechTarget’s Networking Media and Security Media Groups.







