
Denys Rudyi - Fotolia
6 persistent enterprise authentication security issues
Some authentication factors are considered more secure than others but still come with potential drawbacks. Learn about the most common enterprise authentication security issues.
Purloining a person's electronic authenticity is the most insidious way of invading individual privacy. When masquerading as another person, there are unlimited ways to compromise the privacy and integrity of anyone's online data. For this reason, it is important for IT leaders to understand authentication security issues associated with the various authentication methods.
The most important requirement for safeguarding IT is to positively and reliably assure the authentication of a user that requests access to valuable network services. All privacy safeguards in place are quickly nullified if a hostile intrusion can be disguised as coming from a trusted source. For this reason, security practitioners must keep up to date with persistent authentication issues in network security.
1. The problems with password authentication
Passwords are by far the most used and most easily subverted method of authentication. Some organizations have instituted policies to ensure secure passwords, such as frequently changed alphanumeric upper- and lowercase combinations of at least 10 characters. Too often, the inconvenience to the user is so great that such a policy is violated.
If security personnel enforce a policy of elaborate passwords, employees may write down the incomprehensible codes for easy access -- usually in places where such paper records are easily compromised. If an organization does not impose tight rules for password management, users may be tempted to create passwords with easily memorable words -- and, therefore, insecure.
Most security pros are weary of passwords, and they're not alone -- typical end users experience password fatigue as well. Just about every online business prompts users to set up unique personal authentication, as well as a new password. To many individuals, this presents a potentially overwhelming challenge if they hope to avoid using an identical password twice. As a result, some may reuse old passwords, thus increasing their risk of further compromise.
2. The problems with SSO
To address authentication security issues due to overly simple or identical passwords, organizations have turned to single sign-on (SSO). With SSO, a single access code will unlock a central password vault that will then automate authentication processes. Though the concept of a single access master password solves many of the problems with password authentication, it also creates a single point of failure. Critically, this saddles the authentication process with the risk that, if access to the password vault is compromised, the whole organization may become compromised.
The potential effects of a malicious attacker's exploit of SSO would be widely dispersed. If Facebook's SSO was compromised, for example, the attacker essentially gains a master key to access third-party applications and data. Though there are steps organizations can take to protect users in the event of an SSO compromise, few actually put SSO best practices and protections into practice.
Additionally, SSO does not necessarily meet security requirements that third-party applications may necessitate. Learn how users may be locked out of multiple applications when the primary application account availability is lost in the video below.
3. The problems with smart cards
When a user seeks access to a computer via a smart card, the assumption is that the computer has not been compromised. But this ignores the fact that the computer or any other application installed or device implanted in the machine could be compromised. For example, the computer may be infected by hidden malware that exploits the user's identity after authentication has been accomplished. Most routine security incidents occur due to unpatched software or running unauthorized programs. Smart cards cannot prevent these issues.
When users authenticate themselves to a potentially compromised computer, they are not secure in their subsequent online transactions. In these cases, bad actors can steal the users' credentials and inflict various amounts of harm. To steal user credentials authenticated with a smart card, attackers may manipulate the card's client software. Certain types of malware can receive commands from smart cards, sniff sensitive information and enable man in the middle (MitM) attacks.
4. The problems with biometrics
Biometrics have long been touted as the next big thing in enterprise authentication. Certainly, a fingerprint or iris scan can identify an individual. Unfortunately, the means for acquiring biometric records are neither convenient nor inexpensive. Plus, biometrics present their own authentication security issues.
First, obtaining a copy of an individual's biometrics can be trivial. For example, there are devices capable of capturing iris images of a person walking within a few feet of a video camera to enable duplication and use for illegitimate purposes.
Second, after an individual's biometrics have been compromised, they are compromised for life and cannot be secured again. Third, there are technical challenges to consider, including inaccuracy, false positives and bias, as well as the nefarious use of AI to simulate or compromise biometrics.
Last but not least, one of the most significant authentication security issues with biometrics is its reliance on a central database that contains the identifying graphic templates. If such a database is compromised, then the biometrics of every user in the database are compromised for life.
5. The problems with MFA
Multifactor authentication (MFA) is typically considered more secure than transactions that only require a single authentication credential. This belief is reflected in government guidance that suggests online banking transactions in the U.S. have MFA implemented to improve security.
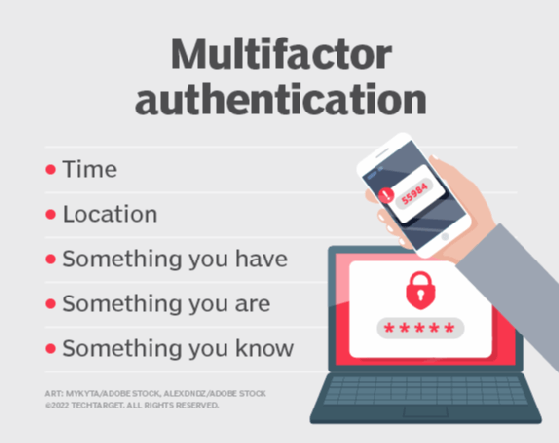
An organization that implements MFA is not immune from MitM attacks via malware or social engineering. Additionally, there is the potential for MFA services themselves to be on the receiving end of attack. In 2011, RSA's SecurID two-factor authentication (2FA) product suffered a data breach caused by spear phishing, which put clients' enterprise networks around the world at risk.
While many organizations rely on 2FA -- the most commonly used form of MFA -- to authenticate end users, it authenticates the user's device and not the user's identity. This is problematic because it assumes the device is in possession of its owner. On top of this, 2FA often involves the use of a one-time password (OTP), which presents authentication security issues of its own.
6. The problems with OTPs
The most common second authentication factor used in 2FA is an OTP -- typically preceded by a personal password. OTPs can be either hardware- or software-based. A routine exploitation of text 2FA is SIM swapping, in which bad actors swap a user's phone number to a mobile device in their possession, which is easily and commonly done. A successful SIM swap attack gives the attacker access to incoming text messages, including the text message containing an OTP for 2FA. Thus, the attacker can exploit the OTP on the new device, resulting in authentication and access to a network or application, for example.
OTPs are also susceptible to interception via MitM attacks, Trojans and other malware attacks.







