
stock.adobe.com
10 ways to prevent computer security threats from insiders
Whether via the spread of malware, spyware or viruses, insiders can do as much damage as outside attackers. Here's how to prevent computer security threats from insiders.
The 2001 unmasking of insider Robert Philip Hanssen as a Russian spy taught the FBI a harsh lesson that most organizations have yet to learn: There's great danger from those we trust the most.
We've gotten pretty good at protecting our perimeters, but most of us do a less-than-adequate job protecting our enterprises from employees (current and former), business partners, contractors, interns and even customers. While most of our attention is focused on internet-based attacks, insiders cause the vast majority of security incidents and can do the most damage. It makes sense: They have intimate knowledge of our network layouts, applications, staff and business practices.
Institutional laxity invites insider problems. In a revealing report, the Department of Justice's Office of the Inspector General cited not Hanssen's brilliance as a spy, but rather the bureau's failure to implement and enforce strong insider security procedures as a prime reason for his success over 20 years.
The FBI isn't unique on this score. Insiders are typically subject to very few controls -- organizations tend to rely on trust rather than any sort of technical or procedural countermeasures. The result can be sabotaged systems, destroyed data, stolen credit card information, etc. The DOJ's list of computer intrusion cases is a litany of inside jobs. Consider just a few:
- A worker in GTE's Network Service Support Center in Tampa, Fla., wiped data and caused more than $200,000 in damage.
- A computer programmer for North Carolina-based Lance, angered over a demotion, planted a logic bomb that took field sales reps' computers offline for days.
- A pair of Chase Manhattan Bank employees stole credit card numbers, which they used to steal nearly $100,000.
How to prevent insider security threats
It's not just malicious actors, either. Employees can unwittingly sabotage systems and create computer security threats through sheer ignorance. Simple mistakes such as clicking rigged links in emails, messaging apps and advertisements invite hackers to surveil companies and organizations with massive consequences. The following are some key terms to remember when considering how to prevent computer security threats from insiders.
Your Editable Incident Response Plan (IRP) Template
Use this as starting point for developing an IRP for your company's needs.
Download now
Virus. A computer virus is malignant code that can steal passwords, spam contacts, corrupt files, log keystrokes and even take over the infected device. To become infected, someone must purposely or accidentally spread the infection. The city of Akron, Ohio, suffered a virus attack in January 2019 that was traced back to ransomware set off after two employees opened fake invoices sent through spam emails.
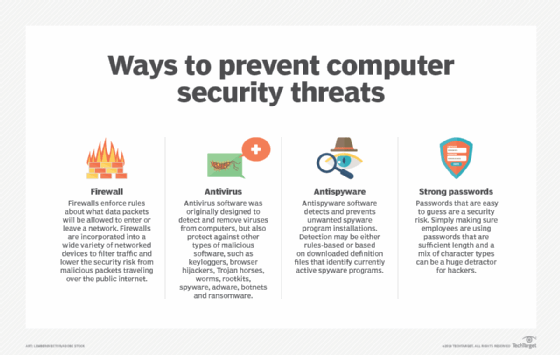
Antivirus. Antivirus software is designed to detect, remove and prevent malware infections on a device or network. Though specifically created to eliminate viruses, antivirus software can also aid against spyware, adware and other malicious software. Basic antivirus programs scan files for the presence of malicious software, allow users to schedule automatic scans and remove any malicious software.
Spyware. Any software installed on a device without the end user's permission is classified as spyware, even if it is downloaded for a harmless purpose. Adware, Trojans and keystroke loggers are all examples of spyware. Without antispyware tools, spyware can be difficult to detect. To prevent spyware, network administrators should require remote workers to access resources over a network through a virtual private network that includes a security scan component.
Users can take preventative measures by reading terms and conditions before installing software, avoiding pop-up ads and only downloading software from trusted sources. Last year, Amnesty Internal became a victim of the Pegasus spyware when an employee clicked on a rigged WhatsApp message. The resulting spyware installation allows the employee's device to be remotely monitored while granting hackers' access to messages, calendars, contacts and its microphone.
Malware. Malicious software, also known as malware, can steal, encrypt or delete private information, monitor computer activity without user permission or alter core computing function of the device. Spyware and viruses are examples of malware. In 2017, health insurance company Anthem paid $115 million in a class-action lawsuit after a record-breaking number of customers' data was left vulnerable because of a security breach. Links to malware in a targeted spear phishing email campaign began in 2014 and went undetected for months. After one employee clicked the links, malware provided hackers with remote access to computers in the network and access to personally identifiable information -- all the tools needed for identity theft.
With so many other high-profile cases of phishing schemes in the news, such as the 2018 DNC hack and 2016 Russian election meddling, it's no wonder insider threats keep security personnel up at night. As the case of Anthem insurance shows, it only takes one person to click the wrong link and release the breach floodgates.
Your organization could be next. What can you do about it? Here are 10 tips to help you develop and implement an insider threat mitigation strategy. Some may be complex and costly over the long haul, but others simply involve reviewing your processes and policies and applying best practices. The main point is to turn your information security radar inward.
1. Security policy first
At a minimum, your security policy should include procedures to prevent and detect misuse, as well as guidelines for conducting insider investigations. It should spell out the potential consequences of misuse.
Start by reading through your existing security policies, especially those regarding incident handling. Rework sections that rely on trusting insiders. For example, your incident-handling plan shouldn't require your team to contact the administrator of a suspect system to gain access; he or she may be the culprit.
Next, make sure that your policy details the limits on access to and dissemination of personal data about your employees, temps and others who might be targets of investigations. Mishandling this data can have severe consequences, including legal action. Specify who is allowed to access what data, under which circumstances, and with whom they are allowed to share this information.
Finally, to protect the organization from allegations of unfair or unequally applied penalties, make sure your security policy spells out the consequences of misusing company resources.
2. Don't neglect physical security
Regardless of whether you "own" physical security, consider it your No. 1 priority. Simply keeping people away from your critical infrastructure is enough to prevent most insider incidents.
Consider what happened to Red Dot, a Seattle-area heating and cooling company, where two janitors combed through garbage cans, desks and filing cabinets, stealing employee and customer personal information. They obtained fraudulent credit cards and illegally accessed bank accounts, stealing tens of thousands of dollars before they were arrested.
Isolate high-value systems in restricted areas, and apply tight access control. You may be tempted to rely on keycards -- they're flexible and inexpensive -- but they're only single-factor authentication and can be lost, stolen or borrowed. The audit log may show that Alice entered the computer room at 10:03:34 a.m., but what if it was really Bob using her key?
Two-factor authentication -- for example, using a PIN and a keycard -- to augment keycards will thwart card thieves, but obliging employees will still loan their cards and PINs to colleagues.
Consider biometric authentication. Fingerprint scanners and similar devices are popular, albeit expensive choices.
But securing your computer systems isn't enough. Thieves, or overly curious colleagues, will grab sensitive information from unsecured hard copy. Make sure all your employees have at least one lockable drawer in their desk or file cabinet for securing sensitive information.
3. Screen new hires
In general, the more time you spend investigating an applicant's background, the better. If your organization considers background checks too time-consuming, consider outsourcing.
Background checks don't always tell the whole story, however. For example, a typical check might verify the applicant's current address, but would fail to reveal that someone living at the same address is a known con artist or a disgruntled ex-employee.
Services such as Systems Research & Development's NORA (Non-Obvious Relationship Awareness) can find such relationships. By combining information from seemingly unrelated corporate databases, NORA can perform personnel checks -- on employees, subcontractors and vendors -- as well as prospective hires.
4. Use strong authentication
Passwords are passé. Password-cracking technology is quite advanced, and stronger passwords spawn forests of Post-it notes on monitors. And many employees share passwords.
The alternatives are expensive, and general deployment is beyond the means of most organizations. A more cost-effective compromise is to apply strong multifactor authentication only to particularly sensitive applications or systems, such as HR or accounting.
If you do deploy multifactor authentication -- combining user IDs and passwords with tokens, smart cards or fingerprint readers, etc. -- be aware that these methods may not plug all the holes. Once your session is established, a knowledgeable insider may be able to spoof new transactions under your name or simply use your computer while you've stepped away. Windows stations can be set to lock out users after a fixed period of inactivity and require reauthentication.
5. Secure your desktops
You can't depend on users to be responsible for all their configurations, but if you're using Microsoft's Active Directory service, you can use group policies to lock down desktops across your enterprise.
Group policies allow a security manager to set configuration details for the OS and its components (Internet Explorer, Windows Media Player, etc.), as well as other apps. For example, you can change the settings for each of Internet Explorer's security zones, enforce the use of your organization's content filtering internet proxy and even forbid the use of unsigned third-party macros in Microsoft Office apps. Windows itself comes with a number of sample template files, and more are available from Microsoft's website or from the Windows or Office Resource Kits. In addition, make sure access rights to network folders are applied on a strict need-only basis.
6. Segment LANs
Host- or network-based intrusion detection systems deserve a prominent place on the roster of your internal defenses, but finding good monitoring points can be challenging.
Host-based systems usually deploy agents, but network-based systems rely on LAN sniffers. Monitoring a single internet connection is easy, but finding good locations -- choke points -- inside often-chaotic LANs can be more difficult. Ideally, you'd have one sniffer for each LAN segment. In a large network, this is unwieldy, impractical and will probably overwhelm you with worthless alerts.
A better tack is to treat your LAN as a series of enclaves, each of which comprises its own zone of trust, segregated by firewalls at the point where each connects with the corporate backbone.
7. Plug information leaks
Sensitive information can flow out of your organization through email, printed copies, instant messaging or by people simply talking about things they should keep to themselves. Combine security policy and technology to stanch the bleeding.
First, make sure your policy details restrictions on disseminating confidential data.
Technology can help, starting with the intrusion detection system (IDS). Scan your business plan for unique phrases that you wouldn't expect to find anywhere else and configure your IDS to alert you whenever it sees these telltale snippets on the network.
Email firewalls can scan the full text of all outgoing email.
Digital rights management tools restrict distribution of documents by assigning access rights and permissions.
8. Investigate anomalous activities
You probably collect reams of log data from your internet-facing servers: Unix syslogs, Windows event logs, firewall logs, IDS alerts, antivirus reports, dial-up access logs or any of a number of other different audit trails. But what about your internal LAN?
Unlike external attackers, insiders generally aren't careful about covering their tracks. "It's as if the attacker doesn't expect to be caught. Generally, none of the insider attacks we have seen were difficult to investigate," said Peter Vestergaard, former technical manager at Danish security consultancy Protego. "The biggest problem has been that companies don't have sufficient logging. In one case, almost no one knew that logging on a nondomain controller NT/Win2K server is disabled by default. Therefore, little or no log material was available."
Once you've got the log files, you're left with the often-difficult task of sorting through them for suspicious activity. "In all the noise, it's hard to identify a particular person trying to get information on the network," said an information security officer for a large U.S. insurance and financial services company, who requested anonymity. His company uses a home-brewed analysis engine that combines information from several different logs and looks for questionable patterns.
If you have the money, network forensic analysis tools can analyze the flow of information throughout your network.
9. Refocus perimeter tools and strategies
By applying your perimeter tools to the inside of your network, you can greatly increase your security posture, often at little cost. Step one is internal patching. You wouldn't dream of putting unpatched web or email servers on the public internet, so why should you settle for them on your LAN?
Step two is securing hosts by eliminating unused services and locking down configurations.
Once you've got the basics covered, you can add more external tools to your internal repertoire. If you're already using vulnerability assessment tools for your internet-facing services, scan your internal network for very little additional cost. Begin by scanning your most critical servers, like internal email, web and directory servers, then prioritize other systems and scan them in order.
10. Monitor for misuse
Your security may require direct Employee monitoring -- from video cameras to keystroke logging. Research suggests that as many as one-third of all employers perform such monitoring to some degree.
Before jumping on the bandwagon, though, make sure you know what tools are available to you and what constitutes legal monitoring in your jurisdiction.
Web content filters are useful tools, since they can be set to block pornography, competitors' websites and hacker tool repositories, all of which figure prominently in common insider security threats. In general, you can safely employ these as a matter of policy for all your workers.
If you need more detailed information about what specific employees are doing, you must exercise a bit more discretion, but you still have plenty of options that offer keystroke recording, application activity and window title logging, URL visit history and more.









