Top 4 mobile security threats and challenges for businesses
Mobile devices are a target for hackers, with several ways to steal data. These threats -- from network spoofing to phishing texts -- endanger organizations as much as individuals.
There is a common misconception that mobile devices don't get malware or viruses or need protection. However, just like malicious software on a desktop computer, mobile malware can come in the form of ransomware, spyware, Trojan horses and more.
According to Pew Research Center studies, about 90% of Americans own and use smartphones. Organizations are expanding work-from-home practices and BYOD and COPE strategies for mobile devices to enable an on-the-go workforce. While many organizations have invested in mobile device management (MDM) tools, a significant number of mobile endpoints still lack protections against cyberthreats such as phishing, malware and mobile OS exploits.
To protect these critical endpoints, organizations must understand the top mobile security threats and the steps IT can take to combat them.
1. Phishing
As mobile phones continue to gain prevalence in the workplace, spam messages and spam calls can be a serious threat to enterprise security. Phishing is one of the most common points of entry for a cyberattack. Phishing describes a wide range of attacks in which the bad actor poses as a reputable person or organization, usually via email or phone call. Mobile devices hold a lot of data, and a lot of it is in email, text and other messaging apps.
Many organizations invest in web gateways, proxies and next-generation firewalls for security. Hackers find holes in those security measures, such as attacking via an employee's personal email and text messages instead of corporate email. In 2022, video game publisher Activision suffered a data breach after an employee clicked on a malicious link from an SMS phishing (smishing) message. The hackers behind the attack were then able to access sensitive employee information.
How social engineering weaponizes phishing
Cybercriminals can use social engineering to research users they would like to attack, looking for key attributes such as the company where they work, job status, recent posts and updates. This approach is sometimes called spear phishing. That info reveals entry points for hackers to gain users' trust, usually through email or other social posts and messaging. They aim to get the user to share sensitive corporate data and information. While technology plays an important role in helping to proactively secure devices and users, the danger of social engineering is that it relies on human error, allowing a bad actor to infiltrate through phishing sites and malicious applications.
Phishing sites are often URLs opened from a link. These malicious links often look like an authentic site to trick users into thinking they are on the legitimate site for their organization or another business. Phishing attackers use the following methods to get users to open fake websites or files that contain malware:
- Email, both corporate and personal.
- SMS texts or messages from applications such as Facebook Messenger, WhatsApp and iMessage.
- Social media platforms such as Facebook, LinkedIn and Instagram.
Preventive measures for phishing attacks on mobile devices
The best first line of defense against phishing is to train mobile users. Inform employees and anyone else with corporate access about how phishing attacks look, including different phishing methods, such as smishing and voice phishing (vishing). Employees should know how to recognize a phishing message and what to do when they receive one.
Additionally, mobile threat defense (MTD) can help secure devices and end users from phishing attacks. MTD tools secure devices through on-device scanning and detection, using advanced algorithms and filters to prevent attacks in real time. If a device does get hacked, MTD software can quickly quarantine it, preventing potential data breaches.
2. Malicious applications
Hackers design malicious mobile apps to collect corporate and personal data and transmit it to third parties.
Official app stores such as the Apple App Store and Google Play Store have many checks and balances in place to prevent malicious code. Apple enforces a stringent review process for apps in the store, while Google constantly scans apps for malware through its Google Play Protect service. However, some malicious apps can still get through. Additionally, with open source mobile OSes such as Android, users can install applications from other sources, increasing the exposure to malicious attackers.
How to block malicious app downloads
Organizations can invest in MDM as a first line of defense against malicious apps. IT admins can blocklist various mobile applications and allowlist others for the devices they've enrolled in the MDM system. MDM tools also have other security policies to prevent data loss. For more advanced protection in real time, organizations can supplement MDM with an MTD tool. MTD software detects and combats malicious behavior from an app or a zero-day attack, wherein hackers exploit a vulnerability in legitimate software before the vendor can patch it. MTD tools quarantine or disconnect the device to minimize the attack's effects.
Inform mobile device users about security risks and changes to thwart both phishing and malicious app downloads. Develop a mobile device security policy so these users understand the importance of device security and how to use a device that accesses corporate data. These policies must account for all sorts of factors that users and IT admins could encounter during their workday. Include acceptable use policies, device ownership guidelines, mobile update strategy, extensions of existing security policies and more. IT admins can enforce this policy through a combination of tools and platforms such as MTD, MDM and enterprise mobility management, along with soft management methods such as end-user training and documentation.

3. Insecure Wi-Fi and network spoofing
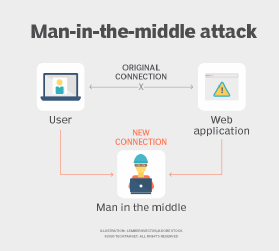
Workers must be careful about how they connect to corporate resources because of spoofing and insecure networks. Attackers can easily mimic Wi-Fi networks to intercept device traffic. Open or "free" Wi-Fi hotspots are notorious for man-in-the-middle and similar attacks where the bad actor intercepts and eavesdrops on device network traffic. The user, in many cases, does not need to perform any actions on the device for the attack to happen. For example, a smartphone might connect to a known network, such as a coffee shop. The smartphone will always try to automatically join a known network if it is in range again. With a tactic called spoofing, the hacker can impersonate the identical Wi-Fi service set identifier (SSID), which is the network's name. Cybercriminals use this method to collect sensitive information without the mobile device user's knowledge.
How to stop network spoofing
IT organizations can use MDM to enforce Wi-Fi policies on corporate-owned and BYOD endpoints, including allowlisting certain SSIDs. Additionally, an MDM can enforce data loss prevention and encryption policies to secure mobile devices. Organizations can also supplement an MDM setup with an MTD tool for more advanced detection of malicious behavior, such as man-in-the-middle attacks.
4. Poor update habits for devices and apps
Keeping endpoints and applications updated is one of the best ways to ensure that sensitive data is secure. Updates and patches fall under the category of cyber hygiene, along with complex passwords and multifactor authentication. Unpatched devices and applications often contain exploits and vulnerabilities that attackers try to use to collect personal and corporate data.
How to stay up to date
Both Apple and Google publish updates to patch security vulnerabilities and exploits to prevent future attacks, limiting the potential for zero-day vulnerabilities. For Android, Google has started publishing monthly security patches that other device manufacturers can implement for their customers. Apple is also proactive with multiple mobile OS updates a year, ensuring devices are secure. Organizations can enforce device update policies and manage application updates via an MDM tool.
Editor's note: This article was originally published in 2021 and was updated in 2024 to improve the reader experience.
Michael Goad is a freelance writer and solutions architect with experience handling mobility in an enterprise setting.






