one-time password
What is a one-time password (OTP)?
A one-time password (OTP) is an automatically generated numeric or alphanumeric string of characters that authenticates a user for a single transaction or login session.
An OTP is more secure than a static password, especially a user-created password, which can be weak and reused across multiple accounts.
OTPs might replace traditional authentication login information or may be used in addition to it to add another layer of security.
One-time password examples
OTP security tokens are microprocessor-based smart cards or pocket-size key fobs that produce a numeric or alphanumeric code to authenticate access to the system or transaction. This secret code changes every 30 or 60 seconds, depending on how the token is configured.
Mobile device apps, such as Google Authenticator, rely on the token device and PIN to generate the one-time password for two-step verification.
OTP security tokens can be implemented using hardware, software or on demand. Unlike traditional passwords that remain static or expire every 30 to 60 days, the one-time password is used for one transaction or login session.
How to get a one-time password
When an unauthenticated user attempts to access a system or perform a transaction on a device, an authentication manager on the network server generates a number or shared secret, using one-time password algorithms. The same number and algorithm are used by the security token on the smart card or device to match and validate the one-time password and user.
Many companies use Short Message Service (SMS) to provide a temporary passcode via text for a second authentication factor. The temporary passcode is obtained out of band through cellphone communications after the user enters his username and password on networked information systems and transaction-oriented web applications.
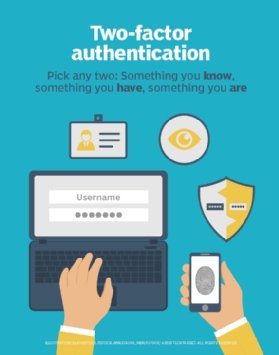
For two-factor authentication (2FA), the user enters a user ID, traditional password and temporary passcode to access the account or system.
How a one-time password works
In OTP-based authentication methods, the user's OTP app and the authentication server rely on shared secrets.
Values for one-time passwords are generated using the following factors in conjunction with one another:
- HMAC, or Hash-based Message Authentication Code, algorithm.
- A moving factor, such as time-based information -- e.g., a time-based OTP (TOTP) -- or an event counter that tracks the number of authorization attempts -- e.g., HMAC-based OTP (HOTPs).
The OTP values have minute or second timestamps for greater security. The one-time password can be delivered to a user through several channels, including an SMS-based text message, an email or a dedicated application on the endpoint.
Security professionals have long been concerned that SMS message spoofing and man-in-the-middle attacks can be used to break 2FA systems that rely on one-time passwords.
The U.S. National Institute of Standards and Technology (NIST) considered deprecating SMS for 2FA and one-time passwords in 2016. Ultimately, however, the organization decided that while using SMS as a second authentication factor is not the most secure option, it is more effective than single-factor authentication.
Experts such as those at NIST recommend enterprises consider one-time password delivery methods besides SMS -- and avoid delivering OTPs via SMS to email addresses or VoIP numbers, which cannot prove device possession.
Benefits of a one-time password
The one-time password avoids some common pitfalls of password security. With OTPs, IT administrators and security managers do not have to worry about composition rules, known-bad and weak passwords, sharing of credentials or reuse of the same password on multiple accounts and systems.
Another advantage of one-time passwords is that they become invalid in minutes -- in the case of TOTPs -- or once they have been used -- in the case of HOTPs. In this way, one-time passwords prevent attackers from obtaining the secret codes and reusing them.
Editor's note: This article was written by Ivy Wigmore in 2014 and subsequently updated by Kathleen Richards. TechTarget editors revised it in 2023 to improve the reader experience.






