
ERP (enterprise resource planning)
What is ERP (enterprise resource planning)?
ERP, or enterprise resource planning, is software designed to manage and integrate the functions of core business processes like finance, HR, supply chain and inventory management in a single system.
Widely used in businesses of all sizes, ERP is considered a must-have for large enterprises and is increasingly being deployed in growing small businesses. The complexity of the global economy and modern consumer demands have made streamlining business processes and managing and optimizing data critical. ERP is typically the foundation of these capabilities.
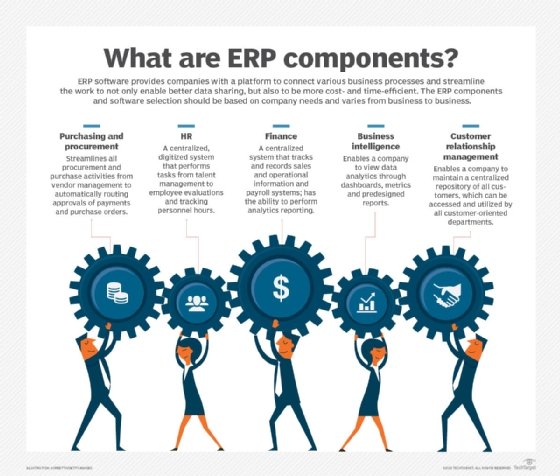
Key components of an ERP system
An ERP system consists of software components, or modules, each of which focuses on a distinct business process. Certain modules are considered "core" to nearly every type of business and the first to be deployed:
- The ERP finance module automates basic accounting, invoicing, financial analysis, forecasting and reporting. It is often the main reason a company moves to ERP from standalone accounting software. The growing complexity of the business makes apparent the need to have a single system to manage all of the financial transactions and accounting for multiple business units and product lines.
- Human resources (HR), also known as human capital management (HCM) is another core process that companies try to improve with ERP. Basic HCM handles employee records, benefits management and payroll but often adds talent management functions, such as recruiting and performance management.
- Other ERP modules common to most businesses include order management, customer relationship management (CRM) and purchasing (procurement).
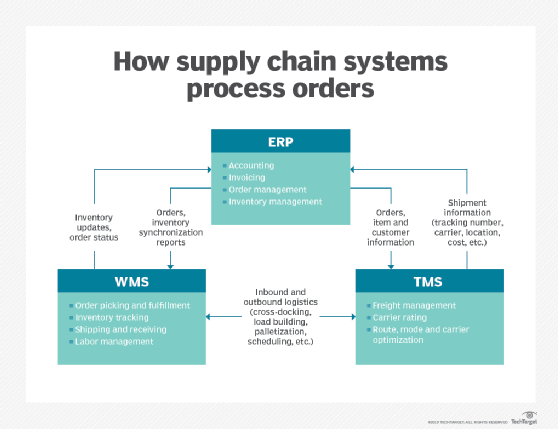
Companies involved in manufacturing or distribution typically add a supply chain management (SCM) module to track inventory levels and manage warehouses and transportation across the supply chain. If their business needs are complex, they might add a warehouse management system (WMS) and transportation management system (TMS) -- perhaps from different software vendors -- to manage these logistics functions.
This article is part of
The ultimate guide to ERP
These additional modules, which companies often buy when they outgrow the typically more basic modules included in their ERP system, are often called "best of breed."
How do ERP systems work?
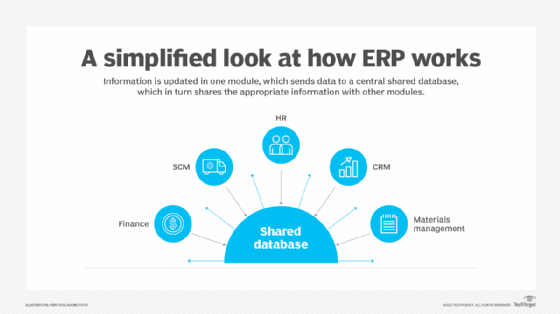
ERP is distinguished from standalone applications by its central database that records information from the business transactions and other actions carried out in the modules, and by integration that allows the modules to communicate with each other and with the common database.
The centralized database provides what's known in IT as a single source of truth ensuring that every module has up-to-date information (see Figure 1).
An ERP system is also likely to have a consistent look and feel across modules, unlike a collection of business management software from different vendors.
Here's an abbreviated example of how these connected modules share information to help an ERP user complete a set of tasks called order to cash -- the process of entering customer orders, delivering products, then receiving and recording payment.
The ERP user enters information about the customer, such as contact information, and creates a sales order in the order management module. Then, they check availability of the product in the inventory management module (or a part of order management with access to inventory data) and return to order management to arrange shipping.
When confirmation arrives that the customer received the shipment, the user creates an entry in the accounts receivable section of the general ledger, the collective name for the accounts in the ERP finance module. There, they generate an invoice and send it to the customer. When payment arrives, the user enters the payment in the general ledger or a cash-management module, and the revenue is recorded and reconciled with the company's bank account.
If the workflow is mostly automated, much of this manual data entry is performed by the ERP system, perhaps in a dedicated order-to-cash module, and some data fields will already be filled in with information from other modules. Behind the scenes, ERP modules are exchanging messages with each other or changing records in the database to ensure that the data is accurate. For example, when the user requests an order shipment, data accessed by the inventory management module must change to reflect the reduction in available inventory.
Figure 2 shows how ERP interacts with a WMS and TMS to process orders.
Why are ERP systems important for businesses?
ERP is the digital nervous system of all but the smallest businesses. When the software is first installed, it almost immediately provides the traditional advantages of computerization: the partial automating and digitizing of manual, paper-based processes. But the advantages of ERP go far beyond that.
Transactions and record keeping usually speed up and become more accurate and predictable. Workers in every department gain access to timely information, which improves communication, decision-making and coordination of business processes. Businesses thereby become more agile and able to respond to changing market conditions. Internet access extends ERP to customers, suppliers and partners, helping to align supply with demand and ultimately boost profits.
Benefits of ERP systems
ERP offers numerous benefits, most of which come from information sharing and standardization. Because ERP modules can share data more easily than disparate systems, they can make cross-departmental business processes easier to manage. They can also enable better insights from real-time data and business intelligence, especially with the newer technologies that many ERP systems are including, such as advanced analytics, artificial intelligence (including machine learning) and the industrial internet of things.
In addition, ERP software provides several other advantages:
- Boosts efficiency by automating data collection.
- Enables growth by managing increasingly complex business processes.
- Helps lower risk by enabling better compliance.
- Fosters collaboration through communication and data sharing.
- Improves customer service.
- Improves supply chain management.
- Saves money by streamlining processes.
- Enables greater, often real-time visibility into parts of the business, such as inventory, that are critical for meeting customer needs.
- Supports better reporting and planning thanks to more timely and accurate data.
Types of ERP systems
ERP products generally vary by the size of the company they're intended for, the type of computing infrastructure they run on and whether they have features specific to a particular industry.
Small businesses vs. midmarket vs. large enterprises
For the small business market, some vendors make entry-level ERP that comes with core HR, finance and other commonly used modules, such as order management and CRM, and is relatively easy to implement.
Other products are meant for the so-called midmarket. Definitions vary, but midmarket is generally defined as companies with several hundred employees and annual revenues between $50 million and $1 billion. Midmarket ERP adds more optional modules, such as SCM and WMS, and can accommodate more users than entry-level ERP.
Some vendors of entry-level ERP sell to both small and midmarket (also called medium-sized) businesses -- often lumped together as SMBs -- and claim their products can scale to accommodate growth.
The top category is large enterprises: companies with more than $1 billion in revenue and typically thousands of employees. Not surprisingly, large ERP systems usually have the most modules, with more capabilities in each module and capacity for thousands -- even hundreds of thousands -- of users.
On-premises vs. cloud vs. hybrid
The first ERP systems sold in the 1970s through the 1990s all ran on premises, i.e., on the company's computers. Nowadays, ERP is just as likely to run in the cloud on systems maintained by the vendor or a service provider, and users access the software over the internet from their desktop or mobile devices. Some systems combine on-premises and cloud modules in what's called hybrid ERP.
The different deployment models (as the industry calls cloud, on-premises and hybrid ERP options) have a major impact on an ERP product's capabilities, user-friendliness, cost, implementation speed and target market.
On-premises ERP typically must be paid for upfront, with a software license for a certain number of users. It usually takes the longest to implement -- projects can go on for years -- and upgrading to new versions can be slow. But on-premises ERP has two big advantages over most types of cloud ERP: It can be customized to meet a unique business requirement and is often easier to integrate with other on-premises systems that are critical to business performance, such as factory automation or warehouse systems (see Figure 3).
Some companies are reluctant to put such mission-critical systems in the cloud for a variety of reasons, including perceived security risks or loss of data control. Others in highly regulated industries or government might be restricted by where systems and data must be located, which often means keeping the system on premises.
In contrast, cloud ERP usually requires less upfront money because it is paid for typically through a monthly subscription; however, over time, the fees can cost more than a license. The biggest savings usually come with multi-tenant SaaS ERP, a type of cloud ERP where different customers share the same copy of the software, which provides economies of scale that allow the vendor to pass some savings along. SaaS ERP also tends to be more streamlined and supports fewer business processes than on-premises ERP, but this simplicity usually makes it easier to use.
Because of the cost savings and deployment speed of the cloud, many ERP products targeting SMBs are SaaS, though there are still some on-premises brands. Large enterprises have historically preferred on-premises ERP, mostly because they had more resources -- time, people and money -- to implement and maintain the complex systems. However, in the past decade or so, many large enterprises have moved to a hybrid model, adding cloud modules for HCM, finance and SCM.
Some ERP systems have features that are needed in specific industries, such as oil and gas, automotive manufacturing, food and beverage, retail and utilities. Often, the ERP vendor partners with a software developer with expertise in a specific industry to create add-ons to a general-purpose ERP system.
History of ERP
Manufacturing beginnings. ERP's roots start in material requirements planning (MRP), a system for calculating the materials and components needed to manufacture a product that was developed by IBM engineer Joseph Orlicky in 1964. By the 1970s, MRP software was a mainstay of manufacturing operations.
In 1983, management expert Oliver Wight developed manufacturing resource planning (MRP II), which extended MRP to other kinds of operations, including financials, and added support for capacity planning and shop floor control, among others.
Back-office software emerges. Separately, vendors in the 1970s -- including two startups, SAP and Baan -- began developing mainframe software for managing financial processes on a single database. The modular, integrated business software grew to encompass other so-called back-office business functions, including HR.
By 1990, analysts at research firm Gartner concluded this category of software needed its own name, dubbing it enterprise resource planning to denote its general-purpose role.
MRP didn't go away, and the still-distinct purposes of MRP and ERP ensure a role for both. Today, ERP software suites sold to manufacturers typically have an MRP module. The term MRP II, on the other hand, has become synonymous with ERP and is rarely used.
Deployment evolves. In the early days of ERP-like systems in the 1970s, the software ran on mainframe computers. By the 1990s, mainframe ERP vendors began migrating the software to the client-server model, where desktop devices communicate with a central server computer. ERP was now accessible to more users more affordably. User-friendliness improved from the clunky character-based user interfaces (UIs) of mainframe days as ERP vendors added Microsoft Windows-style graphical user interfaces to client software and, soon, Windows itself. By the mid-1990s, as the web grew in popularity, client-server ERP was being retrofitted with web browser-like UIs.
The arrival of cloud ERP in the late 1990s was the next fundamental shift in how ERP was delivered and consumed. Cloud computing's internet connectivity made it easier for companies to connect their ERP systems to customers, suppliers and partners. It also made web browsers the standard UI for most new ERP systems.
In recent years, ERP vendors have focused most of their research and development on their cloud products to enable AI and machine learning, blockchain, predictive analytics and other emerging technologies that require the superior computing power and internet connectivity of the cloud.
ERP vendors
There are dozens of ERP vendors, most of which offer both on-premises and cloud options.
Four vendors -- Infor, Microsoft, Oracle and SAP -- are the market leaders in sales, according to most research firms, and have the broadest product lines covering all of the ERP categories described above. They also have the largest installed base of old on-premises systems, which the industry refers to as legacy ERP.
Several vendors are popular with SMBs, notably Acumatica, Sage Intacct and Oracle NetSuite, the SaaS ERP pioneer. Workday is another influential, fast-growing SaaS ERP provider.
Other prominent vendors include Epicor, IFS, DELMIAWorks (formerly IQMS), Plex Systems, QAD, Syspro and Unit4.





