Best practices for reporting ransomware attacks
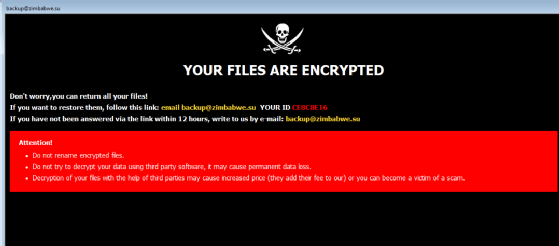
Organizations must decide whether to report ransomware incidents to the authorities and disclose them to the public. Experts weigh in on the options and best practices.
Ransomware isn't going anywhere given how lucrative it continues to be for attackers. The average ransomware payment in 2023 increased to more than $1.5 million according to the Sophos "State of Ransomware 2023" report -- nearly double what it was in 2022 ($812,380).
Because ransomware attacks are so common -- the Verizon "2023 Data Breach Investigations Report" found ransomware accounts for 24% of all breaches -- it's important for organizations to decide what they're going to do if they do become a victim of an attack. This includes whether to pay the ransom as well as whether to report the attack to the authorities.
Should companies report ransomware to law enforcement agencies?
The answer is unquestionably yes, Gartner analyst Paul Furtado advised.
"A lot of law enforcement groups have specialized resources that provide guidance around this," he said. It is especially important for small and medium-sized organizations that don't have dedicated security teams, he added.
Compromised organizations, regardless of size, should also consider the larger picture. "You may also be the target of a coordinated attack. So law enforcement really needs to know what is happening, because you can be just one piece of a bigger puzzle," he said.
This article is part of
What is ransomware? How it works and how to remove it
Some organizations will eventually be required to report ransomware attacks to the authorities. The Cyber Incident Reporting for Critical Infrastructure Act -- signed into law in 2022 and going into effect when Cybersecurity and Infrastructure Security Agency publishes a final rule, expected in 2024 -- requires critical infrastructure organizations to report a cyber attack to CISA within 72 hours and ransom payments within 24 hours.
The Federal Communications Commission in January 2023 proposed updating data breach reporting to require telecommunications carriers notify customers and federal law enforcement in the event of a breach. In July 2023, the Securities and Exchange Commission announced new rules requiring public organizations report cyber attacks within four business days.
In some instances, companies could legally have to notify a federal agency before it can receive payments from its cyber insurance provider, though not all policies require it.
While organizations can willingly report ransomware attacks to law enforcement agencies, the same can't be said about publicly revealing them. Due to the absence of any national ransomware attack notification law, some organizations can quietly pay with no one knowing. Their larger worry may be that the attack could hurt public perception or be used against them in competitors' marketing. If personally identifiable information is involved, however, organizations are required to notify individuals affected.
Reporting ransomware attacks to federal law enforcement helps more than just the organization itself. Forrester Research analyst Allie Mellen said, "Reporting helps us track the number of ransomware attacks happening and helps law enforcement release bulletins about particular threats. I think of it as a 'security as a community initiative.'"
How to report ransomware attacks
The FBI and CISA want victims to notify them of an attack. If your organization has experienced a ransomware event, it should provide law enforcement agencies with the most complete reporting possible. A complaint can be filed to the Internet Crime Complaint Center (IC3) here.
"It's really important to report to [IC3] because it helps them track ransomware incidents within the U.S. and globally, and it can be useful for them when it comes to potentially prosecuting attackers," Mellen said.
Organizations can also contact their local FBI field office, which will ask for the following information:
- The date of ransomware attack.
- How the infection occurred.
- Ransom amount demanded.
- Ransom amount paid, if any.
- The ransomware variant.
- Information about your company, such as industry, size, etc.
- Victim impact statement.
- Losses due to the ransomware attack.
Organizations can also report ransomware to CISA. Like reporting to the FBI, CISA has the following specific ransomware reporting requirements:
- Identify the current level of impact on agency functions or services.
- Identify the type of information lost, compromised or corrupted.
- Estimate the scope of time and resources needed to recover from the incident.
- Identify when the activity was first detected.
- Identify the number of systems, records and users impacted.
- Identify the network location of the observed activity.
- Identify point of contact information for additional follow-up.
CISA requires all submissions include the above information and also requests organizations provide the attack vector; indications of compromise; and subsequent mitigation efforts, if known and applicable. The National Cybersecurity and Communications Integration Center determines a severity score of the attack based on all provided information. The score provides CISA a way to objectively view risk in a national context of the ransomware attack, starting at a Baseline attack -- not likely to affect public health -- and going up to Emergency -- an imminent threat to infrastructure or citizens.
Reporting ransomware attacks is only the first step
Once an organization has reported a ransomware attack and recovered, its focus needs to turn toward ransomware prevention. Mellen said a company's first steps should include implementing regular security monitoring and putting business continuity plans and ransomware incident response plans in place as well as a team ready to execute on those plans.
Tips for enterprise ransomware prevention include using strong email protections and controls, implementing multifactor authentication and using role-based access control. Another important aspect is to have a ransomware-specific security awareness program in place to educate employees about how bad actors can put malicious software onto the corporate network, especially via social engineering.







