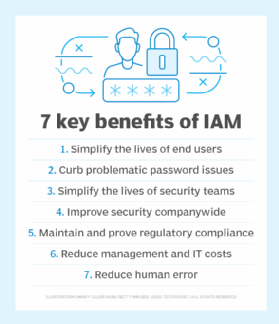
6 key identity and access management benefits
Identity and access management is beneficial not just for users, security and IT admins, but also enterprises as a whole. Read up on the six key advantages of an IAM framework.
Years ago, when users required access to a specific system, application or other corporate resource, they were provided a username and password tied to the access level they needed.
While this was a viable option when the number of IT services was small, it didn't take long before the number of accounts a user had to manage reached a dozen or more. To keep track of all these account usernames and passwords, many end users resorted to writing down their account information on sticky notes that they stuck to their monitors for all to see. Understandably, this type of password management is a big no-no by anyone's security standards. Thus, IT needed a way to better manage the growing number of user accounts. The answer was identity and access management (IAM).
In a nutshell, IAM is a framework of processes, policies and systems that manage digital identities in a secure, streamlined manner. Here's a rundown of the top six identity and access management benefits for users, security admins and enterprises.
1. Simplify the lives of end users
IAM systems enable users -- employees, third parties, contractors, guests, customers, vendors and partners -- to access corporate systems, regardless of where they are, what time it is and, often, what devices they are using.
Rather than requiring users to manage dozens of accounts for various corporate applications or resources, IT administrators can use IAM systems to create a unique digital identity for each user that includes a single set of credentials.
Did you know the average response time to a customer help desk ticket is 7 hours and 4 minutes? If employees are locked out of their account this long waiting for help desk to help them reset their passwords or provide access, it can equate to thousands of dollars in lost productivity.
With an authentication method called single sign-on (SSO), users can access cloud-based, SaaS, web-based and virtual applications with their unique identity. From productivity applications, such as Microsoft 365 or Salesforce, to collaboration applications, such as Zoom or file-sharing services, SSO helps ease the friction of authentication processes and improves UX.
2. Curb problematic password issues
Beyond enabling easier sign-in processes and boosting productivity, IAM systems prevent users from resorting to sticking passwords on their monitor.
Speaking of passwords on sticky notes, compromised user credentials are one of the most common causes of data breaches today. Many IAM systems offer password management features that help security admins enforce password best practices, such as minimum character lengths and frequent password updates, and strong authentication measures, such as multifactor authentication, biometrics or role-based access.
3. Simplify the lives of security teams
Outside of securing an enterprise, one of the biggest identity and access management benefits is that IAM systems improve the efficiency and effectiveness of security teams. IT administrators can use IAM grant access rights based on predefined user roles. This not only reduces the chances of granting authorized access rights to users who should not have them, but it also significantly cuts down user onboarding and offboarding times.
Privileged user access management is a major component here. To prevent resources from being accessed, security admins can apply the principle of least privilege to user roles. This ensures employees, contractors, guests and partners can be quickly and easily set up with only the access needed to complete their job role.
SSO capabilities are generally only used for one enterprise and its associated IT systems. Federated identity management, of which SSO is a subset, links user identities across multiple organizations. With federated identity management, companies and partners can reduce overhead costs by sharing a single application for all user identities.
4. Improve security companywide
With IAM systems, security admins can enforce security policies across all company systems, platforms, applications and devices. This is imperative to enforcing authentication and other security measures, as well as preventing privilege creep.
With companywide IAM policies, it is easier to identify violations, remove inappropriate access privileges and revoke access when needed. They also limit potential internal threats, since employees only have access to the systems they need to perform their specific job duties and cannot escalate privileges without approval or a role change.
Many modern IAM systems use automation, AI and machine learning, and identity analytics capabilities that identify and automatically block anomalous activity.
Using an IAM system also enables IT departments to demonstrate where and how user credentials are used and helps admins identify what data may have been accessed and compromised when a data breach occurs.
IAM systems work on both employee- and company-owned devices and across the cloud. They are also becoming integral to IoT systems as connected devices increasingly access corporate systems. IAM is key to assigning unique identities to connected devices, monitoring the data they access and enforcing security policies in IoT environments.
5. Maintain and prove regulatory compliance
Many regulations, including the Sarbanes-Oxley Act, HIPAA, PCI DSS and GDPR, have data security, privacy and protection mandates that directly relate to IAM. To prove compliance, organizations must understand and be able to verify protections for their data, including who has access to it, how that access is protected, processes for revoking access and how passwords are managed.
During a compliance audit, IAM systems also help IT admins prove where and how user credentials are used and to demonstrate that corporate information is protected with the proper controls.
6. Reduce management and IT costs
Did you know 30%-50% of help desk calls are for password resets? And that the average password reset costs an organization $70? Because IAM systems simplify management for help desk employees and administrators, the time that was once spent on mundane tasks such as helping users locked out of their accounts can now be spent on more high-priority tasks.
Beyond helping prevent data breaches, consolidating user accounts into single identities can eliminate other enterprise expenditures. For example, using federated identities can save costs associated with managing identities across multiple -- often legacy -- applications. Using cloud-based IAM services can also reduce or eliminate the need to buy and maintain on-premises IAM systems.






