indicators of compromise (IOC)
What are indicators of compromise (IOC)?
An indicator of compromise (IOC) is a piece of digital forensic evidence that points to the likely breach of a network or endpoint system. The breach might be the result of malware, compromised credentials, insider threats or other malicious behavior. By the time a security team discovers an IOC, it's likely that a breach has already occurred, which means that data could have been compromised. Even so, an IOC can still help the security team eliminate the threat and limit the damage.
Security teams typically monitor for IOCs as part of a larger cybersecurity strategy. The quicker they can discover and act upon discovered IOCs, the more effectively they can respond to that breach. If security teams catch an IOC breach in progress, they might be able to contain the damage. IOCs can also provide teams with insight into the nature of a breach so they can more effectively protect the systems going forward and improve the overall incident response processes.
Types of indicators of compromise
Security teams rely on a wide range of IOCs to protect network and endpoint systems. Various sources categorize IOCs in different ways. One approach is to separate them into three broad categories:
- Network-based. Network-based IOCs can include events such as unusual traffic patterns or the unexpected use of protocols or ports. For example, there might be a sudden increase in traffic to a specific website or unexpected connections to URLs, IP addresses or domains that are known to be malicious.
- Host-based. Host-based IOCs reveal suspicious behavior on individual endpoints. They can include a wide range of potential threats, including unknown processes, suspicious hash files or other types of files, changes to system settings or file permissions, or changes to file names, extensions or locations. File-based IOCs are sometimes treated as a separate category from host-based IOCs.
- Behavioral. Behavioral IOCs reflect behaviors across the network or computer systems, such as repeated failed login attempts or logins at unusual times. This category is sometimes incorporated into the other categories.
By using the various types of IOCs, security teams can more competently detect and respond to security breaches, as well as be more proactive in preventing them. The teams can also share this information with other organizations to help improve incident response and computer forensics. Such cooperation has led to standard threat intelligence feeds such as OpenIOC and STIX/TAXII, among others.
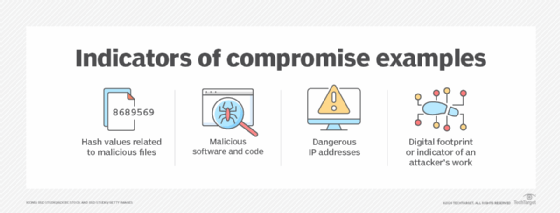
Security professionals look for IOCs in system and security logs, network traffic monitoring systems, enterprise security platforms and other sources. Examples of IOCs include the following:
- Unusual inbound or outbound network traffic patterns, such as unexpected spikes in outbound data transfers.
- Unexpected increases in the number of database reads, which can occur when attackers try to extract data.
- Unusual activity for privileged or administrator accounts, such as requests for expanded permissions.
- Login anomalies or unusual attempts to access resources, such as a sudden increase in access requests.
- Unknown files, services, processes or applications suddenly appearing on a system, such as unexpected software installations.
- Suspicious changes to registries, system files or system configurations, which can occur if an attacker is trying to take control of a system.
- Geographic anomalies, such as unexplained traffic from a particular country or region.
- Unusual domain name system requests, which can occur as a result of command-and-control attacks.
- File-related anomalies, such as a spike in requests for the same file.
By tracking these and other unusual activities, security teams can respond to malicious behavior quickly and effectively. However, IOC tracking alone is not enough to fully protect network and endpoint systems. For this reason, most organizations track IOCs in conjunction with solutions such as security information and event management, extended detection and response, endpoint detection and response, and intrusion detection system, among others.
Explore top incident response service providers, vendors and software and cloud incident response frameworks and best practices. Read about five digital forensics tools experts use. Learn all about threat detection and response and threat hunting techniques, tactics and strategies. Check out 12 common types of malware attacks and how to prevent them.






