Mitre ATT&CK framework
What is the Mitre ATT&CK framework?
The Mitre ATT&CK (pronounced miter attack) framework is a free, globally accessible knowledge base that describes the latest behaviors and tactics of cyber adversaries to help organizations strengthen their cybersecurity strategies. The acronym ATT&CK stands for Adversarial Tactics, Techniques and Common Knowledge, which is the basis for the framework and accompanying ATT&CK knowledge base.
The framework is used across multiple fields and disciplines, including intrusion detection, threat hunting, red teaming, security engineering, threat intelligence and risk management.
Organizations can use the framework to evaluate and test their security methods and to vet cybersecurity vendor products and services. Security vendors can use Mitre ATT&CK to ensure their offerings make defending against and responding to security events faster and more effective.
The framework evaluation criteria are specific to each organization using it and focus on the details of a specific cybersecurity approach. The results of the evaluations are, therefore, noncompetitive; organizations can't use results to gain a business advantage over other organizations that have been evaluated.
The framework and knowledge base were created and are curated by Mitre, a not-for-profit security research organization. The knowledge base is an ongoing project. It contains analyses based on real-world events that organizations can reference when developing threat models and methodologies, and it grows as organizations contribute their knowledge of cyberthreats. The knowledge base, in turn, informs the framework. Mitre aims to foster a stronger overall cybersecurity community with these free offerings.
Mitre ATT&CK history
Mitre launched ATT&CK in 2013 to document common tactics, techniques and procedures that advanced persistent threats used against Windows enterprise networks. It began as an effort to gather this data for a research project on detecting threats in enterprise networks post-compromise, i.e., after adversaries had broken in.
The Fort Meade Experiment (FMX) involved close observation of more than 200 hosts on a monitored network segment. Mitre ran red team operations on this network, meaning it had designated teams to act as attackers using known techniques to penetrate the network. A blue team then attempted to detect and mitigate these simulated attacks.
By simulating the complete cybersecurity landscape from both the attacker's and defender's perspective, Mitre formulated the following key insights that it uses as the basis of its ATT&CK framework:
- Focusing on adversarial behavior enables Mitre to develop behavioral analytics and better techniques for defense.
- Many existing cybersecurity lifecycle models were too abstract and unable to efficiently detect new threats.
- To work, threat behaviors and tactics must be based on real past observations of adversarial behavior.
- Terminology for describing tactics must be consistent across different adversarial groups to enable businesses to compare and contrast them.
By applying these principles in a controlled research setting, Mitre verified that following them improves the threat detection capabilities of defending networks in a measurable way.
In 2015, in light of the project's success, Mitre released the framework to the public. It has since grown to include threats to macOS X, Linux and mobile device operating systems.
In 2020, Mitre released its framework for industrial control systems (ICS). It's designed to handle the issues and challenges that are exclusive to industrial environments. Industrial control systems manage and control critical infrastructure, including manufacturing plants, power plants and other industrial activities. Mitre continues to grow and evolve.
Use cases
The Mitre framework has several use cases that make it compelling for organizations. Common use cases of the framework include the following:
- Penetration testing. In pen testing, organizations designate a red team -- similar to what Mitre did in its FMX research project -- to simulate behavior and find vulnerabilities. Pen testers can use Mitre to learn how to simulate behaviors so they can develop accurate defenses.
- Cybersecurity service evaluation. Cybersecurity vendors can use Mitre's evaluations to determine the strength of their products and services. The evaluations provide objective insights into the use of specific commercial security products, offer a transparent analysis of a given product's capabilities and strengthen the cybersecurity community as a whole by making vendors that develop products responsible for customer security across many industries.
- Cybersecurity gap assessments. Mitre ATT&CK helps identify which sections of an enterprise are deficient in defenses and lack visibility. Organizations can prioritize investments and determine the degree of security coverage by using it to test prospective tools or evaluate existing ones before making a purchase.
- Behavior analytics. The framework can be used for user behavior analytics, as it provides a comprehensive knowledge base of tactics, techniques and procedures that adversaries use during the different phases of the cyber attack lifecycle. For example, the ATT&CK framework includes techniques related to lateral movement, credential access and privilege escalation, which adversaries commonly use. By keeping an eye out for these types of activities, organizations can detect potential security threats and take necessary precautions to mitigate them.
- Prioritization of detection efforts. Security teams can use the ATT&CK framework as a roadmap to determine where to focus their detection efforts. For instance, some teams might opt to prioritize threats that occur earlier in the attack chain whereas other teams might instead focus on specific detections based on the techniques employed by attacker groups in their specific sectors.
- Security operations center maturity assessment. Similar to gap assessment, organizations can use Mitre ATT&CK to determine how effective an SOC is at detecting, analyzing and responding to breaches.
Benefits of the Mitre ATT&CK framework
The broad benefits of the framework include the following:
- Offers a concrete account of adversarial behaviors.
- Provides an account of threat indicators as well as threat groups. Businesses can use Mitre to detect behaviors, make educated guesses about who is performing them and track behaviors across different attacker groups. Its attack page features group-based info.
- Includes sector-specific threat information that's widely used and trusted across many industries.
- Provides a communal approach to threat reporting that ensures info is up to date and checked by the public as well as Mitre.
- Improves an organization's security posture as it aligns its security strategies with the tactics and techniques outlined in the framework.
Using the framework, a business can do the following:
- Associate attack behavior to different groups.
- Pen test its network.
- Find vulnerabilities in its network and map ATT&CK methodologies to threats.
- Discover network misconfigurations.
- Share its cybersecurity knowledge with the broader community.
- Standardize disparate security tools and techniques to create a more cohesive security strategy.
How to use Mitre ATT&CK
There are several ways an organization can use Mitre ATT&CK to strengthen its cybersecurity strategies, including the following:
- Understand the framework and the matrices that cover different attack environments, such as enterprise systems, cloud environments and mobile devices.
- Stay informed on attacker tactics and techniques using the threat matrix.
- Learn how to prep a network pre-attack.
- Learn mitigation strategies post-attack.
- Share observations to improve overall community understanding.
- Evaluate cybersecurity products and services using Mitre's noncompetitive evaluation methodologies. This feature is mainly for cybersecurity vendors.
Tactics and techniques
Tactics and techniques are Mitre's two different ways of categorizing adversarial behavior. By Mitre's definition, a technique describes how adversaries achieve their objective and, sometimes, what they gain from achieving that objective. A tactic describes the objective, or reason, for performing the attack.
Techniques show the information that attackers are after and how they go about getting it. Tactics explain why they want it. Multiple techniques can be used to achieve a tactical objective.
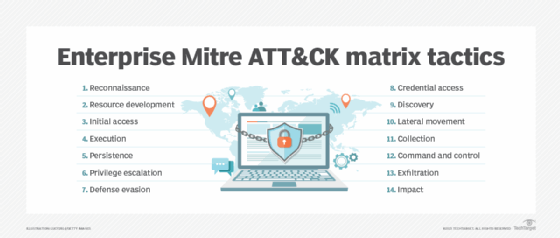
The following 14 tactics are cataloged in the enterprise Mitre ATT&CK matrix:
- Reconnaissance. Adversaries find possible weak points and targets by learning as much as possible about the target.
- Resource development. Adversaries acquire resources, such as infrastructure or tools, to support their operations.
- Initial access. Adversaries gain an initial foothold in the target environment by using techniques such as phishing or exploiting vulnerabilities.
- Execution. To accomplish their goals, adversaries use malicious code or commands on compromised systems.
- Persistence. Adversaries establish ways to continue to access compromised systems even after a reboot or remediation attempts.
- Privilege escalation. Adversaries gain higher levels of access or privileges within the target environment.
- Defense evasion. To avoid detection, adversaries employ techniques to bypass and get around security systems.
- Credential access. Adversaries steal or obtain legitimate credentials to gain unauthorized access to systems or accounts.
- Discovery. Adversaries explore the target environment to collect information regarding the network, systems and user accounts.
- Lateral movement. Adversaries move laterally within the network, in an attempt to expand their reach and access additional systems.
- Collection. Adversaries gather data or information from compromised systems, including sensitive files and credentials.
- Command and control. Adversaries create communication channels between compromised systems and their controlled external entities.
- Exfiltration. Adversaries steal or move data from the target environment to external locations or systems.
- Impact. Adversaries disrupt, modify or destroy systems or data within the target environment.
The main objective of the ATT&CK Matrix is to provide organizations with a deeper understanding of potential threats and to help them formulate more thorough defense strategies.
A visualization of the relationship between attacker tactics and attacker techniques -- essentially a large table or matrix -- is available on the Mitre ATT&CK website. Each tactic or technique is clickable and leads to more detailed explanations of the term. An organization can use this matrix to pinpoint the exact adversarial behavior it wants to learn more about for defense purposes.
Because multiple techniques can be used to achieve a given outcome, the ATT&CK Enterprise Matrix includes multiple techniques in each tactic category. The tactics are listed on the x-axis and the techniques are listed on the y-axis.
For example, if a user clicks on the "Initial Access" tactic, they're presented with 10 techniques and their descriptions. The first three items on the list are "Content Injection," "Drive-by Compromise" and "Exploit Public-Facing Application." If the user clicks on "Content injection," they're taken to a page that describes the attack in more detail, provides procedure examples and lists subtechniques.
Mitre ATT&CK vs. Cyber Kill Chain
Although both the Cyber Kill Chain and Mitre ATT&CK are frameworks used in cybersecurity, their approaches, structures and points of emphasis are different.
Lockheed Martin developed the Cyber Kill Chain model in 2011. It outlines the stages of a cyber attack from initial reconnaissance to data exfiltration.
The seven steps of the Cyber Kill Chain include the following:
- Reconnaissance. Attackers research and identify potential targets.
- Weaponization. Cyber attackers create a backdoor to exploit a delivered payload.
- Delivery. Cybercriminals send the victim a weaponized bundle by USB, email or web.
- Exploitation. Attackers take advantage of a vulnerability to run code on a victim's computer.
- Installation. Intruders install malware and other cyberweapons on the asset's network.
- Command and control. Cybercriminals communicate with their cyber weapons for remote manipulation.
- Actions on objectives. Intruders begin the final stage by carrying out their cyber attack objectives.
Learn how to create a cybersecurity awareness training program that will equip employees with the knowledge and skills they need to help protect their organizations from cyber attacks.







