SYN flood attack
What is a SYN flood attack?
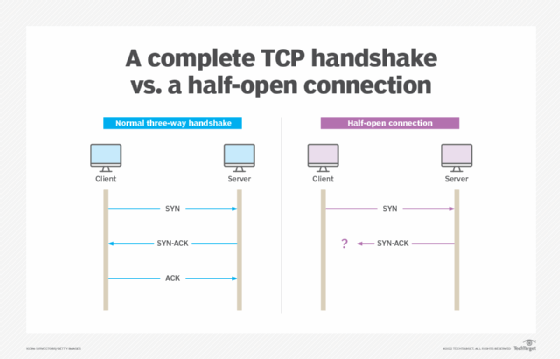
A SYN flood attack is a type of denial-of-service (DoS) attack on a computer server. This exploit is also known as a half-open attack.
SYN floods are one of several common vulnerabilities that take advantage of TCP/IP to overwhelm target systems. SYN flood attacks use a process known as the TCP three-way handshake. As part of the handshake, the client and server exchange messages to establish a communication channel.
The attack involves having a client repeatedly send SYN -- which stands for synchronization -- packets to every port on a server using fake IP addresses. When an attack begins, the targeted server sees the equivalent of multiple attempts to establish communications. It sends a SYN-ACK -- or synchronization acknowledged -- packet from all of the open ports in response to each communication attempt and a RST -- or reset -- packet from all of the closed ports.
SYN flood explained: How it exploits the three-way handshake
A three-way handshake involves the following three steps:
- The client sends a SYN packet to initiate communication with the server.
- The server responds, sending a SYN-ACK packet.
- The client returns a final ACK packet to confirm that the server's SYN-ACK packet was received.
Once those three steps happen, communication can begin between the client and the server. However, in a SYN flood, the hostile client does not return an ACK response packet. Instead, the client program sends repeated SYN requests to all the server's ports. A hostile client knows a port is open when the server responds with a SYN-ACK packet.
The hostile client's SYN requests appear valid to the server. However, because the attacker uses fake IP addresses, the server is unable to close the connection by sending RST packets to the client.
As a result, the connection stays open, and before a timeout can occur, another SYN packet arrives from the hostile client. This is called a half-open connection. The server becomes so busy with the hostile client requests that communication with legitimate traffic is difficult or impossible.
How can a SYN flood attack occur?
The three ways that a SYN flood attack can occur are the following:
- Spoofed. In a spoofed attack, the malicious client spoofs the IP address on each SYN packet sent to the server, making it look like the packets are coming from a trusted server. Spoofing makes it hard to trace the packets and mitigate the attack.
- Direct. This type of SYN attack does not use spoofed IP addresses. Instead, the attacker uses one source device with a real IP address to perform the attack. With this approach, it's easier to trace where the attack is coming from and shut it down.
- Distributed. A distributed DoS (DDoS) attack uses a botnet that spreads the source of malicious packets over many machines. The sources are real, but the distributed nature of the attack makes it difficult to mitigate. Each device in the botnet may also spoof its IP address, adding to the level of obfuscation. The larger the botnet, the less need to mask the IP address.
How is a SYN flood attack mitigated?
There are several ways to mitigate SYN flood attacks, including the following techniques:
- Rate limiting. The number of SYN requests that can be sent to a server at any one time is limited.
- Intrusion detection system (IDS). An IDS or firewall is able to detect and block malicious traffic from a SYN flood attack.
- SYN cookies. With this technique, each connection request gets a unique identifier. This approach can block illegitimate requests, though it also may degrade the TCP connection.
- Increasing the backlog queue. A larger backlog queue increases the allowable number of half-opened While the system performance may be affected, DoS attacks are avoided.
- Recycling the oldest half-open connections. When the backlog of connection requests is full, the oldest half-open TCP connections are recycled. This works as long as legitimate connections can be established faster than malicious half-connections are requested.
Each of these methods has advantages and disadvantages. The best way for an organization to mitigate a TCP SYN flood attack is to configure its systems in a way that aligns with its network security policy and infrastructure.
Why is SYN flood prevention important?
SYN flood prevention is important because these attacks can cause significant damage to networks and systems. SYN floods can cripple servers and networks, making them unavailable to legitimate users. They can also cause data loss and other damage.
High-profile cyber attacks, such as the Mirai botnet, use SYN flooding to crash servers and inflict damage. Internet of things devices are particularly prone to SYN flooding and DDoS attacks.
Is SYN flooding illegal?
Although threat actors often use this technique, SYN flooding is not always illegal. Security professionals and ethical hackers use SYN flooding as a legitimate way to test or debug a network. The practice of intentionally exploiting a computer system or network to discover and fix flaws is known as penetration testing.
However, when SYN flooding is used to harm another computer system, it is illegal. These attackers may be subject to civil penalties or fines. A DDoS attack that uses SYN flooding is an illegal cybercrime in the U.S. Depending on the context, it could be considered a federal offense under the Computer Fraud and Abuse Act.
Providing DDoS protection and deflecting botnets, SYN floods and other exploits require a solid enterprise cybersecurity plan. As part of such a plan, employees must be properly trained. Learn what type of relevant and effective cybersecurity training is needed to maintain excellent cyber hygiene.








