black hat hacker
What is a black hat hacker?
A black hat hacker historically has been used to describe one who has malicious intent -- such as theft of information, fraud or disrupting systems -- but increasingly, more specific terms are being used to describe those people.
A hacker may exploit security vulnerabilities for monetary gain; steal or destroy private data; or alter, disrupt or shut down websites and networks.
The hacker may also sell these exploits to other criminal organizations. The term black hat has been used to differentiate criminal hackers from white hat and gray hat hackers. These categories were inspired by early Western movies, where the heroes could be identified by the white hats they wore and the villains by their black hats.

Different types of hackers
In this section, we review the differences among the three most common types of hackers.
What is a white hat hacker?
A white hat hacker, also called an ethical hacker, is the antithesis of a black hat hacker. White hat hackers are not cybercriminals, rather they are security specialists hired by organizations to conduct tasks such as penetration tests and vulnerability assessments on their systems to improve their security defenses.
When working as pen testers, white hat hackers conduct tests and attacks on networks, websites and software in order to identify possible vulnerabilities. They also follow established rules, such as bug bounty policies.
They will notify the affected organizations directly of any issues so that a patch can be released or other steps taken to fix the flaw.
What is a gray hat hacker?
Gray hat hackers operate with more ethical ambiguity. While they do not hack into systems with the malicious goal of stealing data, they don't participate in true ethical hacking either.
For example, they may be willing to use illegal methods to find flaws. They might then expose vulnerabilities to the public or sell zero-day exploits to government and intelligence agencies.
What is a black hat hacker?
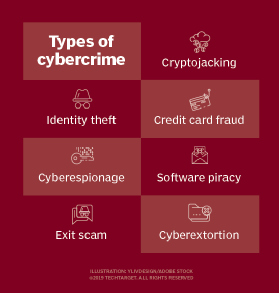
A black hat hacker is typically one that engages in cybercrime operations and uses hacking for financial gain, cyber espionage purposes or other malicious motives, like implanting malware into computer systems.
Laws and penalties against black hat hacking
U.S. and state authorities can punish black hat hackers under a number of computer crime statutes and other state and federal laws. Penalties for conviction on different classes of misdemeanors and felonies include fines, jail time or both.
Some notable laws include the Computer Fraud and Abuse Act, Electronic Communications Privacy Act and Digital Millennium Copyright Act.
These laws generally prohibit a person from conducting the following acts without authorization:
- accessing a protected computer, system or network;
- modifying or disclosing data held on a computer;
- transmitting malicious code in order to damage a system or data held on it;
- accessing a computer with the intention to defraud; and
- trafficking computer passwords.
The term protected computer is broad in scope, referring to a computer used by, for instance, a financial institution or the U.S. government for commerce or interstate and foreign communication.
Certain laws have been passed to help law enforcement agencies investigate and locate black hat hackers.
The Cybersecurity Enhancement Act and Communications Assistance for Law Enforcement Act grant law enforcement agencies the permission to access data stored by an internet service provider. They can do so without a warrant in certain circumstances. Authorities also can access modified telecommunications devices and facilities that can help in authorized electronic surveillance.
Notable black hat hackers
In recent decades, there have been several notable black hat hackers, whose exploits helped to define many of the laws we have in place today.
Kevin Mitnick
Mitnick served time in prison for hacking into Digital Equipment Corporation's computer network to copy its software. His second high-profile arrest in 1995 was as a result of his hack into Pacific Bell's voicemail computers and other major corporations' systems.
He was charged with crimes such as wire fraud, unauthorized access to a federal computer and causing damage to a computer. He served five years in prison.
Since his release in 2000, Mitnick has worked in the cybersecurity industry in several capacities. He runs his own information security consulting business called Mitnick Security, and he also serves as chief hacking officer at anti-phishing vendor KnowBe4.
Albert Gonzalez
Gonzalez, also known as Segvec, was the leader of a major cybercrime scheme that resulted in some of the biggest data breaches in U.S. history.
Over the course of several years, Gonzalez and other members of the ShadowCrew hacking group participated in the theft and sale of payment card account information from a variety of retailers, including The TJX Companies, BJ's Wholesale Club, OfficeMax, Barnes & Noble and Sports Authority.
Gonzalez was charged with conspiracy, computer fraud, wire fraud, access device fraud and aggravated identity theft related to the hacking and data breaches. He was sentenced to 20 years in prison.
Hector Xavier Monsegur
Monsegur, also known as Sabu, was a prominent member of Anonymous, an online hacktivist community, as well as a splinter group, LulzSec.
He and his affiliated groups were responsible for participating in online attacks against companies like Visa, Mastercard and Sony, in addition to government-owned computers in several countries.
Monsegur was arrested in 2011, charged with several computer hacking charges and faced up to 122 years in prison. He became an informant for the Federal Bureau of Investigation (FBI), assisting in the arrest of other hackers. He served seven months in prison.
Yahoo hackers
The U.S. Department of Justice indicted two members of Russian intelligence agency Federal Security Service and two hired hackers for hacking Yahoo in 2014 and stealing information from over 500 million user accounts. The intention behind the hack, according to authorities, was to gather intelligence and for financial gain.
The first hacker, Karim Baratov of Canada, was arrested. The second hacker, Russian citizen Alexsey Belan, was well known to U.S. authorities.
Belan, also known as Magg, was previously indicted by federal authorities in 2012 and 2013 over the data breaches of several unnamed e-commerce companies. He was charged with several counts of computer fraud and abuse, access device fraud and aggravated identity theft.
Belan is still at large, and he is currently among the 105 persons on the FBI's Cyber Most Wanted list.
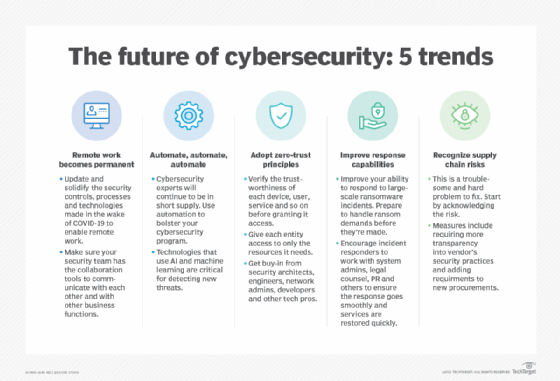
Outlook for black hat hacking
Hacking and cybercrime, in general, are a global epidemic only increasing in frequency and significance each year. Data breaches alone have tended to double annually in recent years. Cyber attacks take many forms, such as phishing, social engineering, ransomware, firewall breaches and distributed denial-of-service attacks.
Malicious hackers' intent can also vary. Some aim to install software that can open an opportunity to ransom or steal trade secrets. Some intend to steal data that can be sold on the dark web or used for identity theft. Others simply intend to cause chaos or service disruption.
Regardless of the hackers' intent, it is clear that organizations and citizens must make themselves aware of best practices in information security and computer security. Utilizing antivirus software and virtual private networks and avoiding questionable emails, links and messages are just a few of the ways system owners can help to protect themselves.
Learn more about the different kinds of hackers, and see why studying the black hat community can help enterprises.
TechTarget is responding to readers' concerns as well as profound cultural changes. In some cases, we are defaulting to industry standards that may be seen as linguistically biased in instances where we have not found a replacement term. However, we are actively seeking out and giving preference to terms that properly convey meaning and intent without the potential to perpetuate negative stereotypes.