end-to-end encryption (E2EE)
What is end-to-end encryption?
End-to-end encryption (E2EE) is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system or device to another.
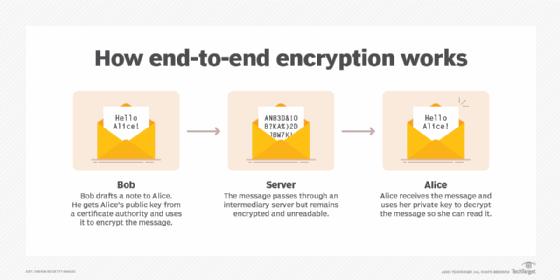
In E2EE, the data is encrypted on the sender's system or device, and only the intended recipient can decrypt it. As it travels to its destination, the message cannot be read or tampered with by an internet service provider (ISP), application service provider, hacker or any other entity or service.
Many popular messaging service providers use end-to-end encryption, including Facebook, WhatsApp and Zoom. These providers have faced controversy around the decision to adopt E2EE. The technology makes it harder for providers to share user information from their services with authorities and potentially provides private messaging to people involved in illicit activities.
How does end-to-end encryption work?
The cryptographic keys used to encrypt and decrypt the messages are stored on the endpoints. This approach uses public key encryption.
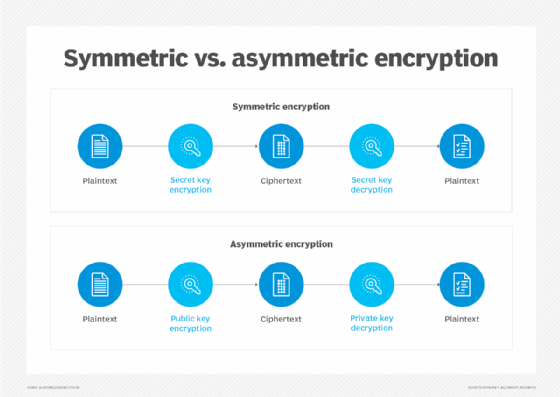
Public key, or asymmetric, encryption uses a public key that can be shared with others and a private key. Once shared, others can use the public key to encrypt a message and send it to the owner of the public key. The message can only be decrypted using the corresponding private key, also called the decryption key.
In online communications, there is almost always an intermediary handing off messages between two parties involved in an exchange. That intermediary is usually a server belonging to an ISP, a telecommunications company or a variety of other organizations. The public key infrastructure E2EE uses ensures the intermediaries cannot eavesdrop on the messages that are being sent.
The method for ensuring a public key is the legitimate key created by the intended recipient is to embed the public key in a certificate that has been digitally signed by a recognized certificate authority (CA). Because the CA's public key is widely distributed and known, its veracity can be counted on; a certificate signed by that public key can be presumed authentic. Since the certificate associates the recipient's name and public key, the CA would presumably not sign a certificate that associated a different public key with the same name.
How does E2EE differ from other types of encryption?
What makes end-to-end encryption unique compared to other encryption systems is that only the endpoints -- the sender and the receiver -- are capable of decrypting and reading the message. Symmetric key encryption, which is also known as single-key or secret key encryption, also provides an unbroken layer of encryption from sender to recipient, but it uses only one key to encrypt messages.
The key used in single-key encryption can be a password, code or string of randomly generated numbers and is sent to the message recipient, enabling them to unencrypt the message. It may be complex and make the message look like gibberish to intermediaries passing it from sender to receiver. However, the message can be intercepted, decrypted and read, no matter how drastically the one key changes it if an intermediary gets ahold of the key. E2EE, with its two keys, keeps intermediaries from accessing the key and decrypting the message.
Another standard encryption strategy is encryption in transit. In this strategy, messages are encrypted by the sender, decrypted intentionally at an intermediary point -- a third-party server owned by the messaging service provider -- and then reencrypted and sent to the recipient. The message is unreadable in transit and may use two-key encryption, but it is not using end-to-end encryption because the message has been decrypted before reaching its final recipient.
Encryption in transit, like E2EE, keeps messages from being intercepted on their journey, but it does create potential vulnerabilities at that midpoint where they are decrypted. The Transport Layer Security encryption protocol is an example of encryption in transit.
How is end-to-end encryption used?
End-to-end encryption is used when data security is necessary, including in the finance, healthcare and communications industries. It is often used to help companies comply with data privacy and security regulations and laws.
For example, an electronic point-of-sale (POS) system provider would include E2EE in its offering to protect sensitive information, such as customer credit card data. Including E2EE would also help a retailer comply with the Payment Card Industry Data Security Standard (PCI DSS), which mandates that card numbers, magnetic stripe data and security codes are not stored on client devices.
What does end-to-end encryption protect against?
E2EE protects against the following two threats:
- Prying eyes. E2EE keeps anyone other than the sender and intended recipient from reading message information in transit because only the sender and recipient have the keys to decrypt the message. Although the message may be visible to an intermediary server that is helping move the message along, it won't be legible.
- Tampering. E2EE also protects against tampering with encrypted messages. There is no way to predictably alter a message encrypted this way, so any attempts at altering would be obvious.
What doesn't end-to-end encryption protect against?
Although the E2EE key exchange is considered unbreakable using known algorithms and current computing power, there are several identified potential weaknesses of the encryption scheme, including the following three:
- Metadata. While E2EE protects the information inside a message, it does not conceal information about the message, such as the date and time it was sent or the participants in the exchange. This metadata could give malicious actors with an interest in the encrypted information clues as to where they may be able to intercept the information once it has been unencrypted.
- Compromised endpoints. If either endpoint has been compromised, an attacker may be able to see a message before it is encrypted or after it is decrypted. Attackers could also retrieve keys from compromised endpoints and execute a man-in-the-middle attack with a stolen public key.
- Vulnerable intermediaries. Sometimes, providers claim to offer end-to-end encryption when what they really offer is closer to encryption in transit. The data may be stored on an intermediary server where it can be accessed.
Advantages of end-to-end encryption
The main advantage of end-to-end encryption is a high level of data privacy, provided by the following features:
- Security in transit. End-to-end encryption uses public key cryptography, which stores private keys on the endpoint devices. Messages can only be decrypted using these keys, so only people with access to the endpoint devices are able to read the message.
- Tamper-proof. With E2EE, the decryption key does not have to be transmitted; the recipient will already have it. If a message encrypted with a public key gets altered or tampered with in transit, the recipient will not be able to decrypt it, so the tampered contents will not be viewable.
- Compliance. Many industries are bound by regulatory compliance laws that require encryption-level data security. End-to-end encryption can help organizations protect that data by making it unreadable.
Disadvantages of end-to-end encryption
Although E2EE generally does a good job of securing digital communications, it does not guarantee data security. Shortcomings of E2EE include the following:
- Complexity in defining the endpoints. Some E2EE implementations allow the encrypted data to be decrypted and reencrypted at certain points during transmission. This makes it important to clearly define and distinguish the endpoints of the communication circuit.
- Too much privacy. Government and law enforcement agencies express concern that end-to-end encryption can protect people sharing illicit content because service providers are unable to provide law enforcement with access to the content.
- Visible metadata. Although messages in transit are encrypted and impossible to read, information about the message -- date sent and recipient, for instance -- is still visible, which may provide useful information to an interloper.
- Endpoint security. If endpoints are compromised, encrypted data may be revealed.
- Not future-proof. Although end-to-end encryption is a strong technology now, there is speculation that eventually quantum computing will render cryptography obsolete.
Applications that use E2EE
The first widely used E2EE messaging software was Pretty Good Privacy, which secured email and stored files and digital signatures. Text messaging applications frequently use end-to-end encryption, including Apple's iMessage, Jabber and Signal Protocol (formerly TextSecure Protocol). POS providers, like Square, also use E2EE protocols to help maintain PCI compliance.
In 2019, Facebook announced that all three of its messaging services would begin using E2EE. However, law enforcement and intelligence agencies argue that encryption limits Facebook's ability to police illegal activity on its platforms. The debate often focuses on how E2EE can make it more difficult to identify and disrupt child abuse on private messaging platforms.
Encryption is just one piece of data security in the enterprise. Learn more about all aspects of data security and compliance in our comprehensive guide.





