identity provider
What is an identity provider?
An identity provider (IdP) is a system component that provides an end user or internet-connected device with a single set of login credentials that ensures the entity is who or what it says it is across multiple platforms, applications and networks.
For example, when a third-party website prompts end users to log in with their Google Account, Google Sign-In is the identity provider.
A single, consistent identity usable across platforms, applications and networks is called a federated identity. An IdP's job is to maintain the federated identity by protecting registered credentials and making them available to disparate directory services through translation services. If an IdP provides endpoint authentication services or user authentication services, it might be referred to as an authentication as a service (AaaS) provider.
An identity provider serves the same basic function as a directory service, such as Microsoft's Active Directory (AD). It enables information security (infosec) administrators to organize and manage the identity of end users, digital devices and network resources and to interact safely and securely over a proprietary network. Network resources include anything from software applications and the databases that support them to physical devices in the internet of things (IoT), such as phones, printers, sensors and actuators.
How do identity providers work?
IdPs communicate with each other and other web service providers using languages, such as Security Assertion Markup Language (SAML), or data formats, such as Open Authorization (OAuth).
An IdP is responsible for sending three basic types of messages:
- An authentication assertion that shows the requesting device is who or what it claims to be.
- An attribution assertion that passes along all relevant data when a connection request is made.
- An authorization assertion that documents whether the user or requesting device was granted access to the online resource or not.
These assertions are Extensible Markup Language (XML) documents that contain all the necessary information to verify users to a service provider.
Security benefits of using an identity provider
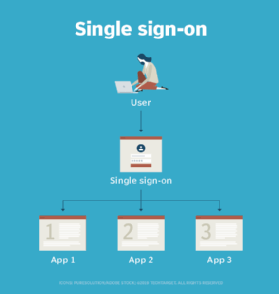
Using an identity provider is convenient for users because it means they no longer must remember multiple logins.
From the service provider's point of view, this approach can be more secure for the following reasons:
- The IdP provides a central audit trail of all access events, which makes it easier to prove who is accessing what resources and when.
- The IdP saves users the hassle of creating and maintaining multiple usernames and passwords with single sign-on (SSO). Maintaining and reentering multiple passwords can lead to identity and password sprawl. The more times users must log in or remember a new password, the more likely they are to jeopardize its security -- for example, by writing it down on a sticky note, reusing passwords or creating easy-to-hack passwords.
- The service provider doesn't have to be concerned about protecting personally identifiable information (PII) because that is the IdP's responsibility.
Types of identity providers
The two main types of identity management providers are enterprise-based and social-based. An enterprise identity provider is used in a corporate enterprise for identity and access management (IAM) or in personal computing to authenticate users for online activities that take place behind a registration wall, such as online shopping and access to subscription-based content. A social-based IdP allows users to login using social media accounts.
Identity providers can also be categorized by the languages they use for communication with service providers.
SAML is a language better suited to corporate interests because it provides more control, enabling corporations to make their SSO logins more secure. SSO is an important aspect of identity as a service (IDaaS) and AaaS.
Popular identity providers
Popular companies that offer IdP services include the following:
- Google.
- Facebook.
- Apple.
- Microsoft.
- Amazon Web Services (AWS).
Popular IdPs for enterprise/corporate use include the following:
- AD.
- Native Azure AD.
- G Suite.
- Lightweight Directory Access Protocol (LDAP).
- PingFederate.
- SharePoint.
Risk of using an identity provider
The downside of using an IdP is that sensitive information is still sent to a third party, albeit a reliable one. There is always the risk that the identity provider could be hacked or lose control of the information it possesses through poor data hygiene.
Blockchain is one solution that might mitigate this issue. Conventional IdPs federate and centralize identity; an IdP that uses blockchain takes advantage of the way blockchain stores information. This approach enables users to have a single identity, just like SSO and IDaaS, yet still be in full control of their credentials instead of handing them off to a third-party provider.
Identity providers vs. service providers
When talking about IdPs, the service provider is the entity that maintains the digital resource a user is trying to access. The identity provider delivers authentication credentials to the service provider at the user's request. This distinction can be confusing because, technically, an identity provider is also a service provider.