principle of least privilege (POLP)
What is the principle of least privilege (POLP)?
The principle of least privilege (POLP) is a concept in computer security that limits users' access rights to only what is strictly required to do their jobs. POLP can also restrict access rights for applications, systems and processes to only those who are authorized. This principle is also known as the access control principle or the principle of minimal privilege.
POLP is considered a cybersecurity best practice, as it restricts access to high-value data and assets. In addition, organizations that use POLP can improve their security posture by reducing their attack surface. It's also used in zero-trust network access (ZTNA).
Depending on the system, some privileges might be based on attributes contingent on the user's role within the organization. For example, some corporate access systems grant the appropriate level of access based on factors such as location, seniority or time of day. An organization can specify which users can access what in the system and the system can be configured so the access controls recognize only the administrators' roles and parameters.
How does POLP work?
The principle of least privilege grants users permission to read, write or execute only the files or resources necessary to do their jobs. Time-limited privileges can also be enabled to ensure users have access to critical data for just the amount of time needed to perform a specific task. Without this principle, an organization could create overprivileged users, which could increase their chance of data breaches and malicious actions.
Organizations should adopt POLP as a default security measure to ensure that no one employee has access to critical information they don't need. Likewise, the number of privileged accounts should be kept at a minimum. For example, system administrators are typically privileged accounts, as they help other employees with their software and hardware. Some system administrators might be given unlimited privileges, making them a bigger target for attackers. As such, minimal privileges should also be placed on system administrators, limiting the total number of users they have access to.
When configuring new systems or applications, all unnecessary services, applications and data should be disabled. This includes any applications that might be enabled by default.
Organizations should also log authentication and authorizations to critical systems. This way, they can keep track of failed login attempts and access control changes -- which can be a sign of threat actors. Likewise, organizations should review accounts and privileges at regular intervals to ensure there are no overprivileged users.
Why is POLP important?
As a security measure, the principle of least privilege reduces an organization's attack surface by limiting user and administrator access to nonessential information. By enforcing POLP on user devices, any device that becomes infected with malware can't access elevated privileges that might increase access to further information, saving an organization from further potential damage. Likewise, the principle stops employees from intentionally or unintentionally damaging critical systems.
As a cybersecurity best practice, POLP is also an integral part of ZTNA. ZTNA implements the concept of a zero-trust policy and access control to enterprise resources at a network level. It uses identity-based authentication to establish trust and provide access. In the ZTNA framework, POLP provides the ability to accurately identify applications and application functions across a port or protocol.
What is a superuser?
A superuser account provides IT staff members with unlimited privileges so they have full read, write and execute authority and can make changes across a network. This includes installing software, modifying settings and files, and deleting data and users. Superuser accounts are the highest level of privilege and are only given to the most trusted individuals -- usually system administrators or the equivalent. The superuser account is also known as an administrator account and is often dubbed root.
To prevent their sessions from being hijacked, superusers can type the sudo command into any account, enabling the account to temporarily perform a single command with superuser privileges. Ideally, superuser credentials aren't used for logging in. Since the superuser account has full control of the system, it must be protected from unauthorized access.
Controlling access
Least-privileged users (LPUs) are those with the most limited access and often the lowest level of authority within the company. In an organization, users often have elevated levels of access to the network and the data on it. When an LPU account is set up, that user has limited privileges and can perform only specific tasks, such as surfing the web or reading email. This makes it harder for a malicious attacker to use an LPU account to cause harm.
Another way to control user access is by implementing a concept called privilege bracketing. This approach permits users access to administrator accounts for the shortest time necessary to complete the specific task. This function can be administered through special automated software to ensure that access is granted only for the specified amount of time.
What is privilege creep?
Privilege creep refers to the tendency of software developers to gradually add more access rights beyond what individuals need to do their jobs. This commonly happens when a user is given access that isn't revoked later. For example, employees who are promoted might still need temporary access rights to certain systems for their old jobs. But, once they're settled in their new position, more access rights are added and existing privileges often aren't revoked. This unnecessary accumulation of rights could cause major cybersecurity risks and result in data loss or theft.
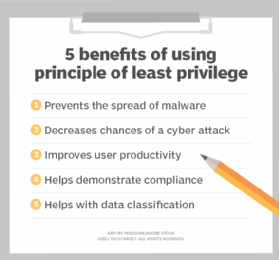
Benefits of using principle of least privilege
POLP can provide organizations with the following benefits:
- Prevents the spread of malware. By imposing POLP restrictions on computer systems, malware attacks can't use higher-privilege or administrator accounts to install malware or damage the system.
- Decreases chances of a cyber attack. Most cyber attacks occur when a hacker exploits privileged credentials. POLP protects systems by limiting the potential damage that an unauthorized user gaining access to a system can cause.
- Improves user productivity. Only giving users the required access to complete their necessary tasks means higher productivity and less troubleshooting.
- Helps demonstrate compliance. In the event of an audit, an organization can prove its compliance with regulatory requirements by presenting the POLP concepts it has implemented.
- Helps with data classification. POLP concepts enable companies to keep track of who has access to what data in the event of unauthorized access.
While POLP helps minimize the risk of an unauthorized user accessing sensitive data, the main disadvantage is that the minimum permissions must be consistent with users' roles and responsibilities, which might be challenging in larger organizations. For example, users might not be able to perform a certain required task if they don't have the appropriate privilege access.
How to implement POLP
Applying POLP concepts can be as simple as eliminating end-user access to devices -- such as removing USB drives to prevent the exfiltration of classified information -- or more involved operations, such as conducting regular privilege audits.
Organizations can successfully implement POLP by doing the following:
- Conducting privilege audits by reviewing all existing processes, programs and accounts to ensure there's no privilege creep.
- Starting all accounts with least privilege and adding privileges according to the access required.
- Implementing separation of privileges by distinguishing between higher-level privilege accounts and lower-level privilege accounts.
- Assigning just-in-time least privileges by providing lower-level privilege accounts with limited access to complete the necessary task.
- Tracking and tracing individual actions conducted by one-time-use credentials to avoid potential damage.
Learn how to implement least privilege access in the cloud to control and manage cloud policies.







