session key
What is a session key?
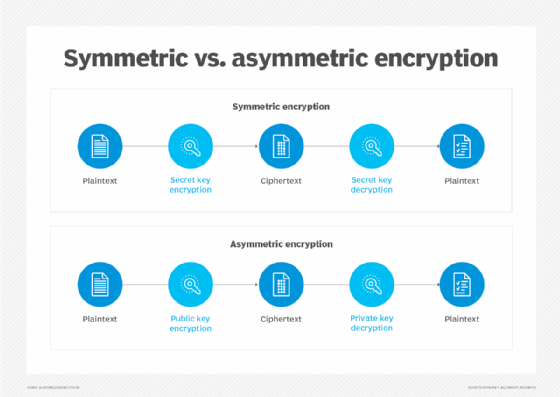
A session key is an encryption and decryption key that is randomly generated to ensure the security of a communications session between a user and another computer or between two computers. Session keys are sometimes called symmetric keys because the same key is used for both encryption and decryption.
The session key is used for only one session. It is then discarded, and a new key is randomly generated for the next session. Public keys or asymmetric encryption, by contrast, use two keys -- a public key and a private key -- instead of a single key to secure data communication between two parties over an open network.
What is a session?
A session is an interaction between a user and a web server characterized by an exchange of information. This exchange may be in the form of a request-response between a browser and web server.
 In this example, Alice encrypts a message she is sending with its current
In this example, Alice encrypts a message she is sending with its current
timestamp using a randomly generated session key. When the server receives
the message, it decrypts it using that same symmetric key to check her name
and timestamp. If those are OK, the server authenticates the message.
Alternatively, the interaction may not involve a request or response between the two parties. For instance, when a user signs in to a web service, the session is essentially an exchange of information that results in the user signing in and the server storing this information for later use.
Another kind of session is a browser session, which is when someone makes a request to a web server. Here, a session begins when a user first requests a page from a web server and is completed when that browser has sent over all the packets of information the server requested, such as when a user logs in to a website. This is considered a session because it is a series of interactions with the website requiring a data connection.
Other kinds of sessions include the following:
- Hypertext Transfer Protocol (HTTP) sessions. An HTTP session is a series of interactions between a user's browser and a web server that persists beyond a single page view and enables the server to track a user's activity.
- Transmission Control Protocol (TCP) session. A TCP session is a logical connection between two network hosts established by the exchange of transport layer segments.
- Telnet remote login session. A Telnet remote login session is a method used to connect to and interact with a remote server.
Cryptography key terms to know
The most important terms to know when discussing cryptography, including session keys, are the following:
- Encryption. The process of converting data into a format that is unreadable without special knowledge.
- Decryption. The process of converting encrypted data back to its original, readable format.
- Symmetric key. A single, shared key used by two parties to encrypt and decrypt data.
- Asymmetric key. Two separate keys used to encrypt and decrypt data.
Advantages of cryptographic session keys
cryptography is an essential tool in the fight against identity theft that is used to protect information in a wide range of applications, such as electronic commerce, information security and data storage. Cryptography uses keys to encrypt and decrypt data. The most common type of cryptography key is a symmetric key, which uses the same key to encrypt and decrypt data -- as opposed to asymmetric keys, which use a separate key for encryption and decryption.
Generated using a symmetric algorithm, sessions keys have number of advantages:
- The major advantage of session keys is they are convenient to use. Session keys can be a single fixed key, or they can be generated dynamically from a set of existing keys.
- Session keys offer added protection because the key is discarded after it has been used to establish a secure communication channel, such as during a Transport Layer Security (TLS) connection.
- Asymmetric algorithms usually take longer to compute than symmetric algorithms. Since session keys are single-use symmetric keys, they are much faster to use for particular applications, including for storing caches of temporary data.
Disadvantages of session keys
Sessions keys are not without their disadvantages, including the following:
- The biggest disadvantage of using session keys is they are not as secure as public keys due to their simplicity. Using a session key for more than one session may compromise it.
- Another disadvantage of using a session key to encrypt data is that it is vulnerable to eavesdropping and compromise. As a symmetric key, a session key is used to both encrypt and decrypt data. This makes information vulnerable should bad actors intercept the key in transit through the network or steal it when stored in the memory of a server.
HTTPS encryption and session keys
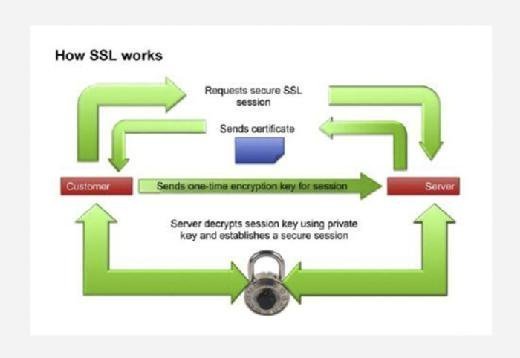
HTTP over Secure Sockets Layer, or SSL, also known as HTTP Secure (HTTPS), is a web protocol that encrypts data sent between a browser and website. The encryption gets the data to its destination securely so it can't be intercepted and read in transit.
By adding an encryption layer to the connection, HTTPS ensures a connection is private. With HTTPS, when a browser sends a request to access a website, it generates a session key. The session key encrypts sent data and decrypts that data when it is received.
For instance, if users enter their checking account information to buy items online, their browser will encrypt that information using a session key. The website's server will then decrypt it using the session key it received from the browser.
How does a TLS handshake work?
In order to create a secure connection between two computers, a series of steps must be taken. Called the TLS handshake, these steps are the first thing that occurs when connecting to a website with HTTPS.
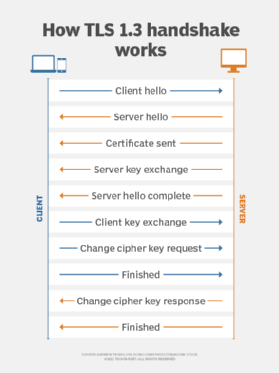
Thinks of a TLS handshake as a protocol that enables two computers to agree on how they will communicate. If the handshake fails, then the connection is not secure. While a TLS handshake can fail in many different ways, the most common reason is due to misinformation passed back and forth between two communicating computers.
A TLS handshake involves the following three steps:
- The server sends its SSL certificate to the client.
- The client checks the certificate.
- The client encrypts a random number with a public key.
The session key encrypts the bulk of the data transmitted in the TLS handshake and is generated and negotiated independently of the protocol version and cipher suite selected by the clients and servers. As a result, the session key is the same for all connections established between two peers that support the same protocol version.
Closely related concepts
Master encryption key (MEK). A MEK is an encryption key that protects other encryption keys. A cryptographic key used to generate a large number of other keys, a master key is usually not directly used for encryption or decryption. Rather, it is used to generate session keys that are then used for communications. Since session keys are only needed for a short period of time, a master key is more practical than a per-use key.
Key encryption key (KEK). A KEK is used to encrypt other keys, such as the data encryption key or the traffic encryption key, that are used to encrypt sensitive data.
Content encryption key (CEK). A CEK is a key that may be further encrypted using a KEK. The CEK is used to encrypt content for storage or transmission, including content in the form of messages, images, audio, etc.






