user authentication
What is user authentication?
User authentication verifies the identity of a user attempting to gain access to a network or computing resource by authorizing a human-to-machine transfer of credentials during interactions on a network to confirm a user's authenticity. The term contrasts with machine authentication, which is an automated authentication method that does not require user input.
Authentication helps ensure only authorized users can gain access to a system by preventing unauthorized users from gaining access and potentially damaging systems, stealing information or causing other problems. Almost all human-to-computer interactions -- other than guest and automatically logged-in accounts -- perform a user authentication. It authorizes access on both wired and wireless networks to enable access to networked and internet-connected systems and resources.
A straightforward process, user authentication consists of three tasks:
- Identification. Users have to prove who they are.
- Authentication. Users have to prove they are who they say they are.
- Authorization. Users have to prove they're allowed to do what they are trying to do.
User authentication can be as simple as requiring a user to type a unique identifier, such as a user ID, along with a password to access a system. It can also be more complex, however -- for example, requiring a user to provide information about physical objects or the environment or even take actions, such as placing a finger on a fingerprint reader.
User authentication methods
The main factors used in user authentication include the following:
- Knowledge factors include all things users must know in order to log in to gain access to a system. Usernames, IDs, passwords and personal identification numbers (PINs) all fall under this category.
- Possession factors consist of anything users must have in their possession in order to log in. This category includes one-time password tokens, key fobs, smartphone apps, and employee ID cards.
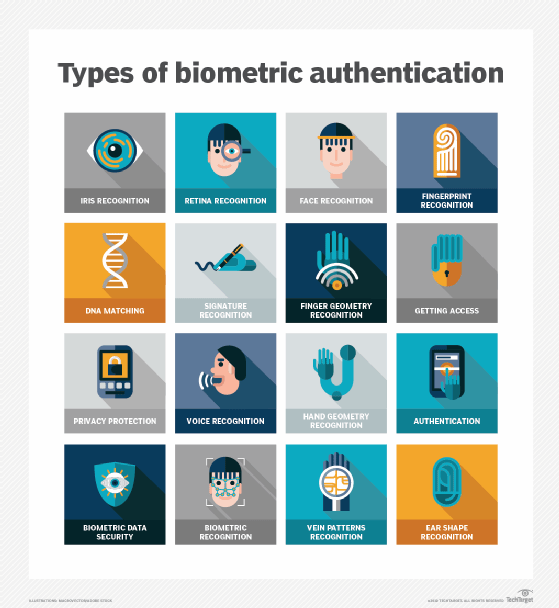
- Inherence factors include characteristics inherent to individuals that confirm their identity. This category includes the scope of biometrics, such as retina scans, fingerprint scans, facial recognition and Voice authentication.
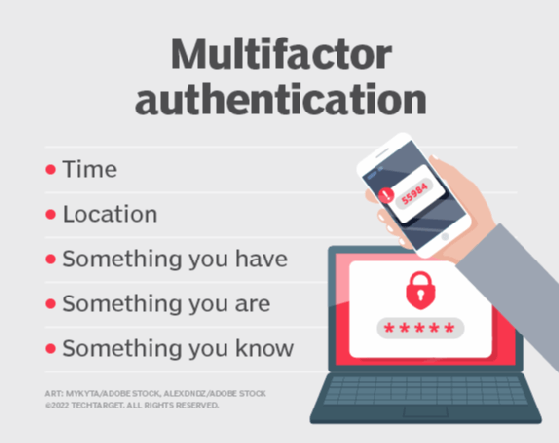
Other factors include location and time factors, which are typically used together or in conjunction with another authentication factor:
- Location factors are a method of confirming users' identity through their location. User authentication systems accomplish this by using the built-in Global Positioning System (GPS) functionality of most smartphones to identify a person's location or combine Wi-Fi and cell tower triangulation to estimate a location. Authentication systems typically do not use location on its own to confirm identity. For example, if an attacker logs in with a user's password, the location factor can prevent the attacker in a different geographical area from posing as the user, who typically logs in only from a specific location. Here, location and password are used together to confirm identity.
- Time factors add time-based access characteristics to confirm identity. Similar to the location factor, the time factor is not adequate on its own but can be helpful when used with another factor. For example, if a system last authenticated a user at noon in the U.S., an attempt to log in an hour later from Asia would be rejected based on the combination of time and location. A time factor can also only permit access within a scheduled time interval.
Single-factor authentication vs. multifactor authentication
Single-factor authentication (SFA) requires verification of one piece of information from a user, such as a password. Because SFA commonly employs knowledge factors, which require only a single piece of information, it can't stop an attacker who has stolen a user's password from accessing a user's system.
Multifactor authentication (MFA) uses more than one method of authentication to verify the identity of a user. For example, a user may be required to provide a password in combination with a security question. Two-factor authentication (2FA) uses factors from two of the authentication categories, while four-factor authentication (4FA) uses at least one factor from four categories of factors. The latter is considered far more secure due to the additional layers of security that come with more factors.
User authentication limitations and improvements
A number of issues affect the security of an authentication system. In addition to the number of factors involved, the specific technologies used and the manner in which they are implemented affect reliability. Well-designed and appropriately enforced implementation rules can help ensure the security of user authentication.
For example, passwords -- among the most vulnerable methods of authentication -- are relatively insecure because hackers can typically easily guess and crack them. To alleviate the problem, several industries and organizations have implemented strong password standards, which insist users create passwords that meet minimum length and other requirements, such as including at least one number and letter plus a symbol.
The ubiquity of mobile devices and cloud computing today has greatly affected how enterprises implement authentication. In the past, a simple password authentication system was sufficient to keep networks secure. However, increased risk of data breaches has made companies reevaluate their authentication strategies. Modern authentication processes should involve more than a single factor in order to ensure the highest level of security.
While MFA provides added layers of security for confirming a user's identity, it is also important not to overburden users with difficult authentication routines, which can lead to noncompliance that undermines the purpose of the authentication system in the first place. For instance, MFA with automatic processes can enhance security, while minimizing the effort required by the user.
MFA is especially important for organizations that offer cloud-based services, as the cloud itself provides secondary authentication if a user has a password breach.






