eavesdropping
What is eavesdropping?
Eavesdropping is the act of listening to, recording or intercepting private communications. It can apply to verbal conversations, such as phone calls or people talking face-to-face, or it can refer to data communications, including email, text messages, video conferences, fax transmissions, internet of things data streams or any other type of data that's transmitted over a network.
Eavesdropping can be carried out by individuals and organizations, and their reasons for doing it can vary widely:
- Governments engaged in espionage.
- Cybercriminals trying to steal sensitive information.
- People spying on their neighbors or co-workers.
- Businesses trying to gain a competitive advantage.
- Blackmailers attempting to learn their victims' secrets.
- Law enforcement agencies investigating criminal activity.
Eavesdropping victims can suffer financial loss, identify theft, ruined careers, compromised data, humiliation or jail sentences. In some cases, eavesdropping is part of a larger campaign to gain unauthorized access to a network to steal information, hold the organization hostage, disrupt operations or any combination of these. Whatever the reasons for eavesdropping, the consequences for the victims can be severe.
Eavesdropping on private conversations
The oldest form of eavesdropping is the type that targets live conversations. It comes from the term eavesdrop, which derives from the practice of standing under a building's eaves and listening to the conversation inside.
Eavesdroppers target people in a variety of situations and environments. They might go after people talking on the phone, conversing in a private room, meeting with their co-workers, participating in virtual doctor appointments, sitting on park benches or carrying out private conversations in other ways.
Eavesdroppers use various techniques to listen in on conversations. The original method of eavesdropping was to stand close enough to people conversing to hear what they were saying. The eavesdropper might crouch beneath a window, hold a glass against the wall of an adjoining room, stoop outside a door to "listen at the keyhole" or take other steps to get into close proximity with the conversers.
As technology grew more sophisticated, so did the methods used to listen to and record private conversations:
- Hiding a physical bug or listening device in a bedroom, office, vehicle or other environment to eavesdrop on live conversations. The bug is stashed in a place where it's not likely to be discovered, yet close enough to clearly pick up people talking. In some cases, one of the conversers is wired with a bug. A bug includes a transmitter that broadcasts the conversation to a receiver controlled by the eavesdropper. Through the receiver, the eavesdropper can listen to or record the conversation.
- Wiretapping a conventional phone line to eavesdrop on live telephone conversations. The eavesdropper installs a monitoring device at a specific point in the communication path. The exact location depends on the line's accessibility and how covertly the operation can be carried out. For example, an eavesdropper might wiretap a phone line by cutting into the phone wires outside an individual's home, assuming the wire can be accessed without incident.
- Using a long-distance listening device to capture conversations at a distance. Such a device typically includes a parabolic dish with a microphone inside to pick up conversations. The eavesdropper aims the device toward the place where the private conversation is being held. For example, an eavesdropper might point a listening device at an apartment window 100 yards away to hear what's being said inside.
Eavesdroppers might use a combination of methods to listen in on private conversations, depending on the nature of their surveillance. They might also use the same methods multiple times, such as bugging each room in a house or bugging someone's home and office. Whatever the approach, all eavesdroppers have the same goal: to hear private conversations.
Eavesdropping on data communications
The world of computing and rise of the internet have changed how eavesdropping is conducted and the type of information that is being intercepted. Eavesdroppers are no longer satisfied with just listening to nearby conversations. They're now going after data, which can take many forms, including email, text messages, IP-based phone calls, video chats and conferences, application data or any other type of data that is transmitted across a network.
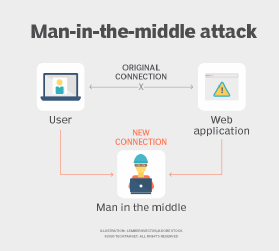
Eavesdroppers hack into computers or other devices to eavesdrop on user communications and actions. The most common type of this kind of eavesdropping is the man-in-the-middle (MitM) attack. With MitM, hackers secretly intercept and relay messages between parties who believe they're communicating directly with one another.
For instance, cybercriminals might trick users into installing malicious software on their devices, which then enables the hackers to control the devices' microphones and cameras, making it possible to spy on users without them knowing. The hackers might also intercept text messages, IP phone calls, chat sessions, online meetings or other communications directly from the computer. Some malicious software makes it possible to log keystrokes, which can be used to access confidential information.
Eavesdroppers also target Wi-Fi networks and local area networks to intercept private conversations and sensitive data. Often, they'll use data-sniffing tools to capture data and retrieve the information they want. Public Wi-Fi networks are particularly susceptible to eavesdropping, as are unencrypted networks of any kind. Network eavesdropping can be difficult to detect because there is minimal impact on the communication itself.
VoIP eavesdropping
With the proliferation of voice over IP (VoIP) systems, eavesdroppers have come up with new ways to listen in on private conversations. Because VoIP communications are digital, they rely on software and data networks to facilitate voice exchanges, making them susceptible to many of the same types of threats found in other digital systems.
Someone who hacks into a VoIP network can use a protocol analyzer to intercept and record phone conversations without callers knowing. Hackers might also be able to control phone devices remotely, allowing them to turn on a phone's microphone without alerting anyone. VoIP systems are especially susceptible to eavesdropping if encryption is not used, although they can be vulnerable even with encryption.
Learn how organizations can address VoIP security threats and see how to prevent network eavesdropping attacks.







