rimom - Fotolia
3 ransomware distribution methods popular with attackers
To prevent cyber attacks, understanding how they work is half the battle. Explore the most common ransomware distribution methods in this excerpt of 'Preventing Ransomware.'
Be careful where you click.
Ransomware, like other varieties of malware, is commonly distributed via phishing emails. One wrong click on a malicious link or attachment can result in a costly breach. Ransomware attack victims in 2020 paid an average of $4.4 million in damages, according to the "CrowdStrike Services Cyber Front Lines Report."
There is more than one way to deliver ransomware, however. In addition to phishing emails, infected websites and lateral movement are common ransomware distribution methods, as outlined in Preventing Ransomware by Abhijit Mohanta, Mounir Hahad and Kumaraguru Velmurugan.
The book, published by Packt Publishing, covers the fundamentals of identifying, preventing and responding to ransomware and discusses real-world examples, including WannaCry, Bad Rabbit and Petya. In the following excerpt from Chapter 3 of Preventing Ransomware, the authors detail three main ransomware distribution methods to help security teams anticipate and prevent attacks on all fronts.
Be sure to check out a Q&A with Mohanta to learn more about his malware research and how ransomware will evolve. Also, download a PDF of Chapter 3 to read the full-length chapter for a closer look at email and lateral movement ransomware distribution methods.
3. Web attacks
 Click to learn more about
Click to learn more about
Preventing Ransomware
by Abhijit Mohanta, Mounir
Hahad and Kumaraguru
Velmurugan.
Malware is also delivered through web attacks. Attacks can leverage vulnerabilities in websites and browsers to execute the attack.
A web application is hosted on a web server and, as a result, we get a website. A web application is composed of web pages, databases, and several subcomponents. Web pages are created using PHP, HTML, Java, JavaScript, and so on. A database for a website can be created using MySQL, Postgres SQL, and MongoDB. Joomla, WordPress, and Drupal are some popular readily available web applications. People can use these as templates and modify them to create their websites as per their requirements. Apache Tomcat, JBoss, and Microsoft IIS are some of the famous web servers. A vulnerability in a web application, web page, database, or web server can expose the website to attack. We term these kinds of vulnerabilities as server-side vulnerabilities. Attackers can use these vulnerabilities to compromise the website. They can get the credentials of the users who have logged into the website. Also, an attacker can embed code in the web pages of the site. He can embed URLs in the website that can redirect the victim to malicious sites which can contain ransomware or other malware. SQL injection attacks and cross-site scripting attacks are the most popular attacks carried out on websites. SQL injection attacks are aimed at manipulating the database whereas cross-site scripting attacks can embed malicious code in a website. There are a lot more attacks. You can find a list of some of the top web vulnerabilities at the Open Web Application Security Project (OWASP) site.
OWASP is an organization that lists the top vulnerabilities: https://www.owasp.org/index.php/Category:OWASP_Top_Ten_Project.
A desktop user uses a web browser to browse a site. Firefox, Internet Explorer, and Chrome are commonly used web browsers. The web server hosts websites while a browser acts as a client that consumes the web pages. Browsers have the ability to parse the code in web pages hosted on a website and display it to the user. One can install plugins in browsers to extend their capabilities. The Adobe Flash plugin extends the capability to view videos in the web browser. A vulnerability can be present in the browser or its plugin. An attacker uses an exploit (explained in section 4.11 Exploit in Chapter 1, Malware from Fun to Profit), intended for the particular vulnerability, to compromise the browser and execute malicious code, thus taking control of the system.
These kinds of vulnerabilities are often termed as client-side vulnerabilities. If an attacker uses the vulnerability in a browser, only the user with a certain browser is affected.
If the attack involves an exploit (refer to Chapter 1, Malware from Fun to Profit) related to Internet Explorer, the user using Firefox is not affected by that particular exploit.
Again, exploits are specific to a version of software too. An exploit that is intended to compromise Internet Explorer 6 may not harm an Internet Explorer 7 browser unless they have the same vulnerability. A successful execution of an exploit is dependent upon the protection mechanisms employed by the operating system. Windows has developed several techniques, such as DEP and ASLR, to protect browsers and other software installed on it. We will be explaining these mechanisms in the Defense mechanism section in Chapter 8, Ransomware Detection and Prevention. Exploits are designed to bypass these defensive mechanisms too.
3.1 Exploit kits
An exploit kit is a web application that serves a lot of exploits. The idea behind this is to try and apply all kinds of permutations and combinations of exploits on the victim. A victim could be using any version of Internet Explorer with a version of Flash player installed in it. The exploit kit can have exploits for various versions of Flash and Internet Explorer for various versions of Windows. A code in an exploit kit usually checks for the operating system, browser versions, and browser plugins installed on the victim's machine and accordingly serves the exploit for that particular version. The code that does this is called the landing page. The landing page code works in a hidden way and the victim does not get any notifications regarding it. After the landing page gets the details of the victim, it delivers the suitable exploit that can compromise the victim. Usually, the landing page is highly obfuscated and security analysts find it hard to de-obfuscate:

The landing page is almost human unreadable. You can see that the variable name looks scrambled. Analysts use tools, such as malzilla, are used to de-obfuscate these landing pages. We will talk about analyzing and de-obfuscating JavaScript in a later part of the chapter.
Sometimes an exploit kit has another intermediate layer called a gate. An exploit kit gate does some extra checks before forwarding the control to the landing page. It checks for some basic functionalities, such as the operating system and region. If the exploit kit has only a Windows exploit, it is pointless in trying to use it on Linux or Mac operating systems. After confirming that the operating system of the victim is Windows, the gate redirects to the landing page, which checks for minute details, such as the operating system version, browser versions, and browser plugins. After profiling the victim, the landing page delivers a suitable attack that can compromise the victim. The gate can also check the geographical location of the victim.
The exploit kit is hosted on a web server and the URL is distributed. The most common technique used in the recent past was to inject these URLs into legitimate sites. A victim can be infected by just visiting a legitimate site. We call this technique of spreading malware a drive-by-download attack. These legitimate sites could have web application vulnerabilities, such as cross-site scripting and so on, which could allow the attacker to inject the malicious URL into the website. The injected URL does not change any look and feel of the legitimate site and therefore the victim is not aware of the backend malicious activities. Hidden iframes containing the exploit kit URL are injected into legitimate sites. For those who have not come across it before, an iframe is an HTML tag that can be used to embed content from another HTML page. Here an iframe is used to redirect a clean site to a malicious site:
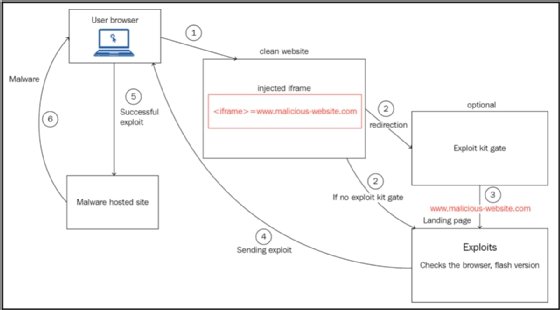
If the exploitation is complete, the shellcode (explained in Chapter 1, Exploits) downloads a malware. The malware can be a ransomware or a downloader (a downloader is described in section 4. Types of Malware in Chapter 1, Malware from Fun to Profit). A downloader is a malware that can be configured to download any other kind of malware. In the recent past, most exploit kits used to download versions of CryptoLocker. Bedep was a downloader which was downloaded by some exploit kits and which in turn was used to download ransomware.
It's been a decade since exploit kits were first discovered. The first exploit kit found in 2006 was the webattacker kit. Mpack was the second exploit kit and traces of Mpack were found at the end of 2006. Some popular exploit kits that followed include:
- Blackhole
- Angler
- Rig
- Neosploit
- Nuclear
- Sweet orange
- Magnitude
- Fiesta
These kits were distributed by spam emails and compromised websites. We will describe a few exploit kits involved in ransomware attacks later in this chapter, as well as in other chapters. Writing an exploit is extremely complex. The exploit kit can have 0-day exploits which were not seen earlier; therefore, a patch was not available to protect against it. So a lot of the time, it was hard to stop them. Many of these exploit kits were sold as tools in the underground market.
Hackers carry out exploit kit campaigns to spread the exploit kit to increase their coverage. Afraidgate, pseudo-Darkleech, and EITest are popular exploit kit campaigns. Campaigns can be identified by the way the compromised sites are infected.
The following is a snapshot of an injected iframe used in the pseudo-Darkleech campaign. This iframe was injected into a very popular legitimate site:
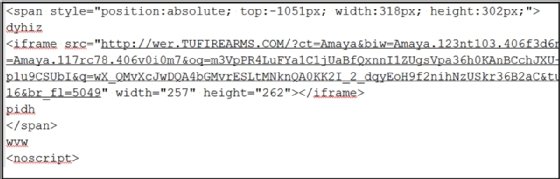
The iframe injected lies between the <span> tag followed by a <noscript> tag. The preceding campaigns were used by the nutrino exploit kit and downloaded CrypMIC ransomware. Darkleech is a malicious Apache web server module that injects malicious iframes into the hosted websites.
Other types of campaigns can be similarly recognized by their patterns.
We sometimes define the whole process of infection as a drive-by-download attack. The attacker visits the sites and without the victim's knowledge, his browser is redirected to exploit kit sites and ends up getting infected. We will go through a small case study of the rig exploit kit, which was used in the distribution of Cerber ransomware. I am using a pcap from http://www.malware-traffic-analysis.net/2016/12/26/index.html. The exploit kit uses a pseudo-Darkleech campaign:
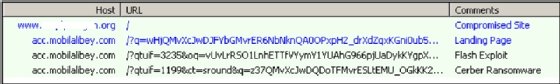
The compromised site is infected and the iframe is injected into it:
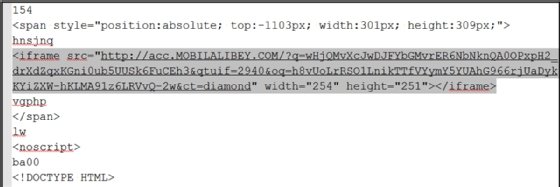
The injected iframe redirects the victim to the landing page hosted on http://acc.MOBILALIBEY.COM/. The landing pages are highly obfuscated:
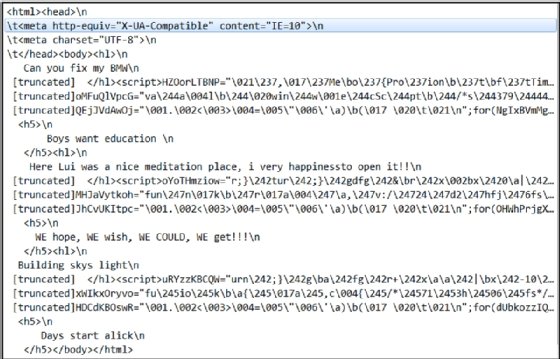
It is a highly obfuscated page. Needless to say, it would take a lot of time trying to read it. The landing page then delivers a flash exploit to the victim. After successful exploitation, the flash exploit downloads the Cerber ransomware.
Malvertising is another popular method used by hackers to victimize with exploit kits. Malvertising means advertising a great online business. A lot of sites offer to show advertisements related to your company. Many bloggers also integrate with advertising sites. The blogger gets revenue in return. Very popular sites can generate a lot of revenue for themselves by allowing advertisements on their sites. We see a lot of advertising in news sites. It's common for a normal user to see ads in lots of sites and forums. Attackers often compromise these advertisements and inject malicious code into them. When a user clicks on an advertisement generated from an ad from that site, he ends up getting compromised. The Angler exploit kit was spread in 2016 using malvertising.
We will talk about a few exploit kits that contributed to ransomware distribution in the following sections.
3.1.1 BlackHole exploit kit
The Blackhole exploit kit was first seen in 2010. It was largely distributed through spams containing links to a compromised website.
Here are some exploits that were used in the Blackhole exploit kit:
- Activex vulnerabilities-CVE-2006-0003
- Adobe reader vulnerabilities-CVE-2007-5659, CVE-2008-2992, CVE-2009-4324,
- Adobe Flash player vulnerabilities-CVE-2011-2110, CVE-2011-0611
- Java vulnerabilities-CVE-2010-4452, CVE-2011-3544, CVE-2012-0507
There were more exploits integrated in the Blackhole exploit kit.
We have discussed the CVE in section 4.11 Exploits in Chapter 1, Malware from Fun to Profit. For further details about the vulnerabilities, refer to cve.mitre.org/.
Blackhole exploits distributed many kinds of malware. A lot of them distributed rogue or fake antivirus. Reveton was one popular ransomware distributed by Blackhole.
Law authorities caught the Blackhole authors, named HodLuM and Paunch, at the end of 2013. They confessed that they earned $50,000 a month by selling the exploit kit to other underground groups.
3.1.2 Nuclear exploit kit
The Nuclear exploit kit was first seen in 2010.
The Nuclear exploit kit had exploits for the following vulnerabilities:
- Adobe Acrobat Reader: CVE-2010-0188
- Adobe Flash Player: CVE-2014-0515, CVE-2014-0569, CVE-2014-8439, CVE-2015-0311, CVE-2015-0336
- Internet Explorer: CVE-2013-2551
- Microsoft Silverlight: CVE-2013-0074
- Java: CVE-2012-0507
Nuclear was known to spread through pseudo-Darkleech and Afraidgate campaigns.
Nuclear was also known to download CryptMIC, Locky, CryptoLocker, Teslacrypt, and CTB-Locker ransomware. Other than ransomware, it also distributed banking trojans. Nuclear was finally shut down in mid-2016.
3.1.3 Neutrino Exploit kit
Neutrino was seen in 2013 and continued until 2016. Neutrino started with Java vulnerabilities:
- Java-CVE: 2013-0431, CVE-2013-2460, CVE-2013-2463, CVE-2013-2465, CVE-2013-2551
- Silverlight: CVE-2013-0074
- Adobe flash player: CVE-2015-0336
Neutrino was spread using pseudo-Darkleech, EiTest, and Afraidgate campaigns. Neutrino was rented in the underground market for $450 per month. Neutrino was known to distribute CryptXXX, Crypmic, and zepto ransomware in 2016.
Other popular exploit kits that contributed to ransomware distribution during the period of 2016-2017 were Angler, Rig, Sundown, and Magnitude. These exploit kits have Internet Explorer, Microsoft Silverlight, and Adobe Flash Player vulnerabilities. All of these were involved in the distribution of the top ransomware of the time - Locky, Cryptolocker, and CryptXX. Angler embedded the leaked hacking team Adobe Flash exploits to its kit in 2016.
Angler was shut down in mid-2016 after the arrests of some cyber criminals. The Rig and Sundown exploit kits continued until the third quarter of 2017.
 Abhijit Mohanta
Abhijit Mohanta
About the authors
Abhijit Mohanta is the author of Malware Analysis and Detection Engineering, published by Apress, and Preventing Ransomware, published by Packt Publishing. He has worked in the security industry for more than 13 years. He is passionate about mentoring professionals in specialized areas of cybersecurity, including malware analysis, reverse-engineering, intrusion analysis, digital forensics and memory forensics. He has more than 13 years of experience in the antimalware field. Mohanta has worked in antimalware research labs at Uptycs, Symantec, McAfee and Juniper Networks. He has experience in reverse-engineering, malware analysis, and detection engine development and is a book reviewer for Packt Publishing. He holds multiple patents in the field of malware analysis and detection and gives talks at various security conferences and webinars.
Mounir Hahad is a cybersecurity expert focused on malware research, detection techniques and threat intelligence. He is head of Juniper Threat Labs at Juniper Networks. Prior to joining Juniper, he was the head of threat research at Cyphort, a company focused on advanced threat detection and security analytics. He has also held various leadership positions at Cisco and IronPort working on VPN, unified threat management, email and web security. He holds a Ph.D. in computer science from the University of Rennes in France.
Kumaraguru Velmurugan has more than 10 years of experience in malware analysis and remedial measures. Before working at Microsoft as a security researcher, he was a senior malware researcher at FireEye. He has been associated with different antivirus and sandbox products in his career. He is a passionate reverse-engineer and is interested in assembly programming and automation in the cybersecurity domain. He has authored and assisted technically in blogging about interesting key features employed by malware and owns a patent on malware remedial measures.







