employee productivity
What is employee productivity?
Employee productivity, sometimes referred to as workforce productivity, is an assessment of the efficiency of a worker or group of workers.
How is employee productivity measured?
Productivity may be evaluated in terms of the output of an employee over a specific time. Typically, the productivity of a given worker is assessed relative to an average for employees doing similar work. Because much of the success of any organization relies upon the productivity of its workforce, employee productivity is an important consideration for businesses.
Why is employee productivity important to business?
An organization's success depends significantly on its employees and their productivity. The work environment matters greatly, and human resources play a key role. The environment includes a company culture that should encourage work-life balance, employee engagement and well-being, development of achievable performance metrics, and incentives to reward performance. Systems and technology are also important, as they can greatly increase employee productivity if they are properly designed and working as intended.
Companies generally set expectations for employee productivity. For example, in a factory manufacturing auto parts, employees may be expected to complete the assembly of a targeted number of finished pieces per work day. The use of robots and other automation technology greatly improves product quality and volumes but may or may not directly impact individual employee productivity. Of course, the employee's minimum daily production output can be adjusted to factor in technology.
Loss of employee productivity can have different consequences, such as the inability to ship the required numbers of components to customers or failure to deliver government-mandated reports on time. As such, maximizing employee productivity is everyone's responsibility, from line workers to C-level executives.
The impact of COVID-19 on employee productivity
The COVID-19 pandemic introduced changes in how work is performed. Many such changes involved employees working remotely, such as in another office or from home. This raised concerns about how employee productivity could be monitored and measured. As might be expected, use of productivity-measuring applications increased.
With the shift to remote work came heightened concerns about connectivity. These included the ability of an employee working from home to connect safely and efficiently to the organization's systems, databases and other resources. Productivity would certainly be reduced if remote employees were unable to connect securely to their office applications.
Many employers have been encouraging remote employees to return to the office, with varying degrees of success. Many remote employees felt their productivity increased because they could avoid traditional workplace activities, such as chatting around a water cooler or eating in the company cafeteria. Hybrid arrangements -- e.g., three days in the office and two at home -- have shown promise. In the end, it is traditionally easier for managers to monitor employee productivity -- and deal with productivity issues -- when employees are present at corporate facilities.
How is productivity improved?
The capacity for collaboration has always been important for productivity. In the early days of the corporate network, email and video conferencing provided productivity gains and lowered costs. Newer mobile collaboration tools make it much easier for geographically dispersed employees to work together. Tablets, smartphones and laptops let users connect with colleagues anywhere, at any time.
According to proponents, the bring your own device (BYOD) trend makes employees more productive. Because employees are working on devices that they own and are used to, they're likely to use them more often. The devices are mobile by definition, so whether employees are taking notes in a meeting, reviewing documents during a commute or preparing the next day's agenda while watching television, they can accomplish more in a way that doesn't impact personal time as significantly as it would if the same work is done using a company-issued desktop computer. The biggest concern about BYOD is the threat of cyber attacks to personal devices that may have not been updated by the company with suitable antimalware software. Security and other concerns also abound when employees connect their own devices to company networks.
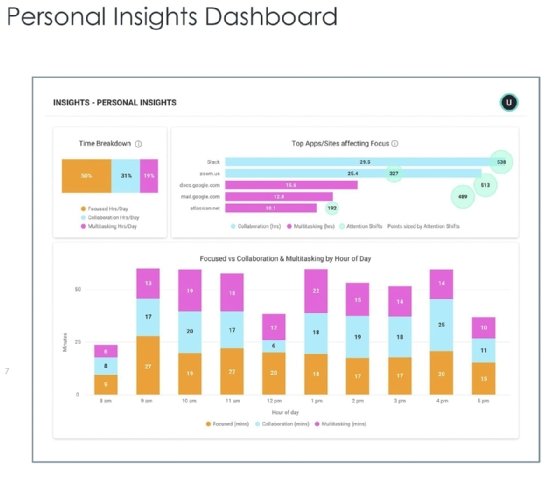
Constant connectivity and the popularity of social networking and social media have made it easier and more tempting for employees to waste time on the job. To prevent online time-wasting, sometimes called cyberslacking, some organizations monitor employees or limit the sites they can access from the corporate network.
Email processing consumes a significant portion of many employees' time, estimated to be about 30% of many knowledge workers' jobs or even more if email is not efficiently handled. Effective email management practices can lessen email's negative impact on productivity. Such practices include limiting the number of email processing sessions each day and limiting the amount of time spent per session. Some organizations may even limit the hours during which email is accessible on the corporate network. Software that tracks employee email activity can be helpful in identifying issues and facilitating best practices.
The number of interruptions an employee encounters each day has been extensively studied. At the University of California, Irvine, for example, Professor Gloria Mark in the Department of Informatics found that, on average, workers are interrupted every three minutes and that it takes 23 minutes after even a brief interruption to return to the original task. Interruption science explores the impact of disruptions on productivity.
Employee productivity is one element of IT productivity, the relationship between an organization's technology investments and its corresponding efficiency gains, or return on investment. This is especially important as workforces are more physically distributed and many employees continue to work from home. Use of employee productivity monitoring and analysis software has become a major management tool for ensuring that employee productivity is achieving the required goals.
Learn seven employee experience stats to reshape your employee experience strategy, explore balancing remote work privacy vs. productivity monitoring and see five keys to successfully motivating remote employees.
