
James Thew - Fotolia
Biometric authentication terms to know
Consumers are on board with biometric authentication, but enterprises aren't so sure. Here's a breakdown of the must-know terms for companies considering biometric authentication.
Biometric authentication is sometimes predicted to be a replacement for passwords that have long been considered too weak to provide true security. So far, though, biometrics have mostly been used as one part of two- or multifactor authentication as enterprises have been slow to widely adopt biometrics capabilities.
Biometric authentication systems capture data, usually encrypt it, and store it so the system can compare it to the stored data when a user tries to authenticate with that particular characteristic. If the user input and the stored data match, the user will be granted access to whatever they are trying to use.
This form of authentication is, however, spreading -- think of Apple's TouchID and FaceID. It's important to know what biometric authentication actually is and what it includes, as well as some of the problems and controversies that come with it.
Biometric authentication: Biometric authentication is the use of unique biological characteristics to verify the identity of a user trying to access an account, building or device. Characteristics such as retina scans, iris recognition, fingerprint scanning, facial recognition and voice identification can all be used in biometric authentication.
As with all authentication factors, there are risks associated with biometrics, including false positives and compromised data. With passwords, for instance, the user can change them if they are compromised by a threat actor. With biometrics, compromised data cannot be changed and it would be unwise to use that particular biometric factor for any other accounts or devices.
Behavioral biometrics: This type of biometrics deals less with innate physical characteristics and more with human patterns such as keystroke dynamics, gait analysis, voice ID, mouse use, signature analysis and cognitive biometrics. Behavioral biometrics is often used in financial organizations and government facilities, with the United States Department of Defense signing a contract in 2019 to use behavioral biometrics for employee identity and security.
Facial recognition: Facial recognition software maps a person's facial features mathematically and stores the data as a face print. The stored face print is compared to a live capture or digital image of the individual's face. Facial recognition's use for authentication has gained popularity on mobile devices, such as Apple's FaceID.
This type of biometric data has also been the source of some controversy, with Facebook using it to automatically identify individuals in photos and Amazon looking to sell its facial recognition software -- Amazon Rekognition -- to government agencies. Privacy advocates often lobby against facial recognition software as an infringement on privacy rights and civil liberties.
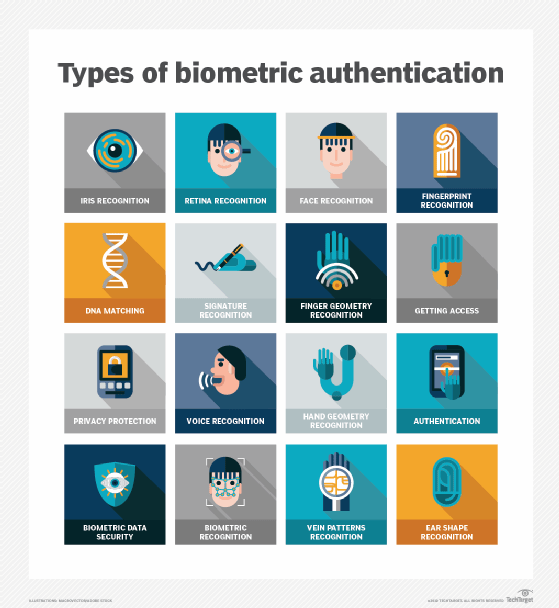
Retina scan: Not to be confused with an iris scan, a retina scan uses an image of a person's retinal blood vessel pattern as an identifying authentication factor. Retina scans are used for access to military bases, nuclear reactors and other high-security facilities since they are difficult to fake and can only be taken from a living human. Some smartphones claim retina scanning abilities, but they are usually referring to iris scanning.
Iris recognition: iris recognition is based on a unique pattern within the ring-shaped region surrounding the pupil of the eye. An iris is usually brown, blue, gray or green and has complex patterns that can be seen up close. For iris recognition to work as an authentication factor, one or more detailed images of the eye is taken with a high-resolution digital camera at visible or infrared wavelengths. A matching engine then compares the person's iris pattern with the stored pictures. Iris recognition is used in airports, points of entry or exit in government buildings, and on smartphones.
Fingerprint scanning: Also called fingerscanning, this is the process of electronically obtaining and storing human fingerprints. The details of a human fingerprint -- raised areas called ridges and branches call bifurcations -- make fingerprints a unique identifier and thus a good factor for biometric authentication. Fingerprints are commonly used on devices such as laptops and smartphones, like Apple's iPhones with TouchID enabled.
Voice ID: Sometimes called voice authentication, voice ID uses a voiceprint that focuses on the unique patterns in a person's vocal characteristics that are created by the shape of the person's mouth and throat.






