
momius - stock.adobe.com
Coronavirus phishing scams increase amid pandemic's spread
Organizations must account for a sharp uptick of coronavirus phishing scams in their pandemic and business continuity plans. Learn about the trend here, with steps for mitigation.
The spread of COVID-19 has been matched by the spread of news and misinformation about the pandemic, including a number of coronavirus phishing scams and spam that prey on users' fear in a time of uncertainty.
The attacks feature a variety of malware, often appealing to targets by purporting to be communications from trusted sources, such as officials or doctors from the Centers for Disease Control and Prevention and the World Health Organization (WHO). Such emails often contain the organization's logo or an email signature to appear like official communication.
Here, find coverage of one of the biggest cybersecurity side effects of coronavirus -- pandemic-related phishing campaigns -- and read up on how to best keep employees and organizations as a whole secure in the face of a global health emergency.
Tracking the increasing trend of coronavirus-themed attacks
Though cyberattacks exploiting coronavirus fears first appeared in January when the virus was mostly relegated to China, February marked the first sharp uptick in occurrences. Thousands of coronavirus phishing scams were detected in the first week of February alone, and the highest single-day detection reached 6,000.
In this Risk & Repeat podcast episode, SearchSecurity editors discussed phishing campaign trends and the potential fallout from cyberattacks on healthcare organizations.
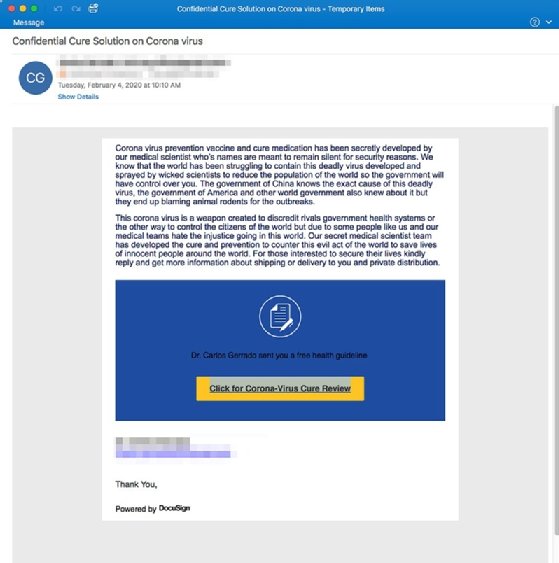
Examples of coronavirus phishing scams in the wild
Phishing and threat detection technologies have identified multiple incidents of coronavirus-related malware, including malicious files disguised in PDF, DOCX and MP4 formats. Other scams detected include malicious hidden images or links, with some installing Trojans or keyloggers to track and harvest credentials. Many included misinformation about COVID-19 vaccines, emergency announcements and modes of transmission, and each scam involved a domain spoof of a trusted source, such as WHO.
Click here to learn more about COVID-19 phishing threats being seen in the wild.
Investigating cybercriminals' phishing tactics and techniques
As COVID-19 spreads, so too does news coverage of the pandemic. As such, global stories involving the coronavirus are frequently exploited by cybercriminals. A combination of high anxieties and a high demand for information increases the likelihood employees will let their cybersecurity guard drop in efforts to stay informed.
Phishers are experts at exploiting their targets' emotions and signaling urgency to increase the chances of engagement with malicious communication. In this conversation with security researcher Steven Murdoch, learn more about cybercriminals' motivations and tactics to prepare for the increasing number of coronavirus phishing scam campaigns.
Defining security's role in a global pandemic
Enterprise security programs do not exist in a vacuum. Infosec is fundamentally about risks, which range from human error to supply chain weaknesses to public health crises. As such, a global pandemic is inherently a cybersecurity issue and should be treated as one -- regardless of an organization's size or industry. As organizations transition to have employees work from home and the onslaught of misinformation puts stress on individuals' security awareness, the responsibilities of infosec pros are shifting.
In this article, get help preparing a comprehensive COVID-19 security agenda, which should include remote work training and learning how to anticipate coronavirus phishing scams.
Enterprise phishing prevention best practices
In response to the uptick in pandemic-related cyberthreats, it is critical for organizations to bolster cybersecurity programs. To mitigate phishing attacks and keep their organizations secure, infosec experts should:
- deploy multifactor authentication to prevent social engineering attackers from gaining entry into the network;
- arm employees with security awareness training campaigns to account for the sophisticated phishing campaigns related to COVID-19;
- fight malware with a combination of security fundamentals, including antimalware software, firewalls, email filtering and continuous monitoring;
- establish vigilant patch management, thus helping prevent users from clicking malicious links, since phishing attacks usually target known vulnerabilities in out-of-date software;
- deploy AI and machine learning technology to continuously monitor and detect malware and phishing interactions in the network;
- beef up antiphishing measures with nine essential email security features, including mailbox intelligence and login hardening, to protect credentials; and
- review advice from the U.S. Cybersecurity and Infrastructure Security Agency on risk management for COVID-19.






