session layer
What is session layer?
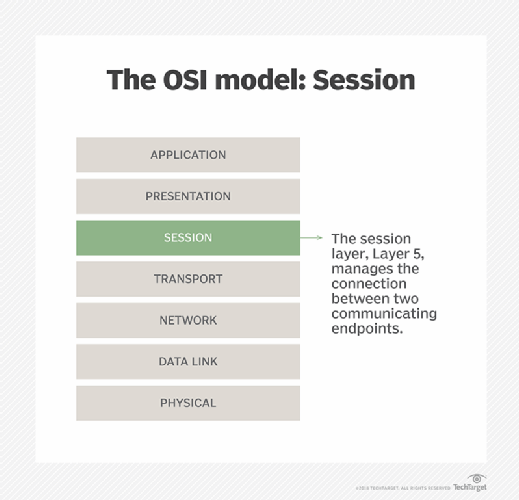
The session layer is Layer 5 of the OSI communications model. It is the long-lived logical connection that persists between endpoints over time. A single session is all the back-and-forth communication between two endpoints. It helps a protocol to be more consistent and reliable. The TCP/IP protocol does not have a separate session layer, but it's functionality can be present in the TCP/IP application layer.
The session layer sits between the transport and the presentation layer in the OSI model. The transport layer consists of short-lived bursts of data, typically in packets. The transport layer isn't concerned if the computers are already in communication or not, it simply sends packets back and forth. The session layer organizes this start and stop traffic into an overall session between the two endpoints with a specific start and end point. The session layer then gives the coherent data it collected to the presentation layer.
The session layer is important for the internet to function because it can save bandwidth and processing power. Encrypted communication between two endpoints typically takes a lot of processing power at startup to create and send the shared secrets. By maintaining the single session between endpoints the same secrets can be used for some time. If there was no long-lived session, they would need to do the same expensive start up process each time they wanted to send a packet of data, which would be slow and take a lot of processing power to do.
Authentication can happen at the start of a session. Then all communication within that session could be considered as coming from the same source, without needing to re-authenticate for every sent data packet.
The session layer can contain checkpoints in the data to be transmitted. If the sent data were to be lost or corrupted during transmission, only the newest data since the last checkpoint would need to be retransmitted. This saves on the total amount of data transmitted. It also insulates the higher-level systems from being aware of low-level data transmission problems.
To help understand the session layer, imagine two people at a party. They would typically say hello to each other at the start of the party, initiating a long session between the two of them. The length of the conversation between when they say hello and goodbye would be one session. The sentences they say back and forth would be the transport layer; they could even talk about different topics, similar to the application layer. A single session could even be momentarily interrupted; perhaps one person stops to talk to someone else, but then goes back to talking to the original person again and continues the conversation without another greeting. When they say goodbye, it would end the session. Maybe much later they bump into each other and then say hello again, starting a new session.
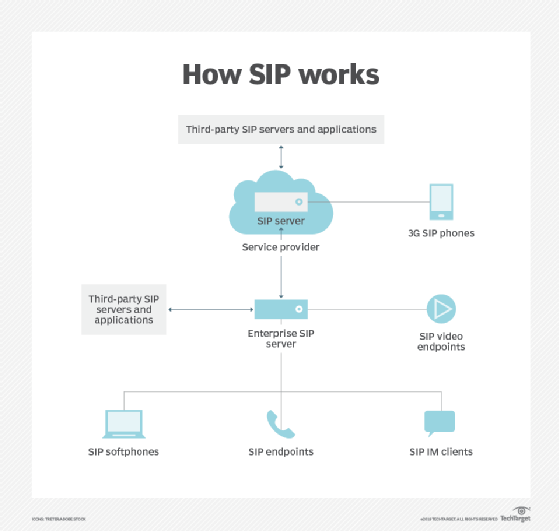
The session layer is important in media streams. IT can help to combine separate data streams, such as one for audio and one for video, into a single session. This can be controlled with high-level protocols, such as the Session Initiation Protocol (SIP).
TCP/IP and the session layer
The OSI model is a theoretical construct of how communication between systems can be understood. It does not directly relate to any specific implementation. TCP/IP, on the other hand, is a practically implemented protocol that is used in modern computer networks and on the internet.
TCP/IP does not contain a specific session layer. Instead the functionality of the OSI session, presentation and application layers are all combined into the single TCP/IP application layer. So, any session functionality present on a TCP/IP network must be implemented on a higher-level protocol that lives on top of TCP/IP.
Session layer protocols
There are several different session layer protocols, including the following:
- AppleTalk Data Stream Protocol (ADSP) and AppleTalk Session Protocol (ASP) (Deprecated).
- H.245.
- ITU X.225.
- Layer 2 Forwarding (L2F) and Layer 2 Tunneling Protocol (L2TP).
- Network Basic Input/Output System (NetBIOS).
- Point-to-Point Tunneling Protocol (PPTP).
- Real-time Transport Control Protocol (RTCP).
- Remote Procedure Call (RPC).
- Session Control Protocol (SCP).
- SIP
- SOCKS Proxy.
Learn how to identify and prevent OSI model Layers 4 to 7 security risks.






