threat detection and response (TDR)
What is threat detection and response (TDR)?
Threat detection and response (TDR) is the process of identifying potential threats and reacting to them before they impact the business. TDR enables organizations to maintain a strong security posture to avoid security incidents, such as data breaches and data loss.
Effective threat detection and response is an increasingly difficult and ever-evolving challenge for security operations center (SOC) teams. Previously, prevention technologies, including antimalware and antivirus software paired with a firewall, were sufficient to defend against cyber attacks. Today, organizations require a defense-in-depth security strategy that incorporates these technologies and more advanced TDR tools and processes to defend against the growing number and sophistication of cyberthreats. Increasingly dispersed workloads and cloud adoption have led to a growing attack surface, which has extended the challenge. Further, many security teams use either manual processes that don't scale in modern environments or disparate TDR tools that don't integrate properly, causing alert overload and fatigue for team members.
In response, a slew of detection and response categories have emerged, including network detection and response (NDR), endpoint detection and response (EDR), managed detection and response (MDR), and extended detection and response (XDR). Many vendors also offer specialized TDR platforms that combine multiple detection and response capabilities.
How does threat detection and response work?
TDR involves two key steps: detection and response. Threat detection encompasses monitoring networks, endpoints, applications, user activity and data to uncover indicators of compromise (IOCs) that could indicate malicious cyber-activity. Threat detection tactics analyze system activity, including traffic patterns, system logs, suspicious files, access attempts, OS calls and applications, for anomalous patterns and behaviors.
Threat response involves processes to identify, mitigate, contain and eradicate detected threats. Response actions include blocking IP addresses, disabling affected accounts, isolating or quarantining infected endpoints, and shutting down affected services until the threat is mitigated.
TDR is a combination of tools and processes, which could include vulnerability scanning, behavioral analytics, threat intelligence, threat hunting, penetration testing, security information and event management (SIEM), incident response, sandboxing, analytics tools, network traffic analysis, automation and orchestration, and more.
What threats does TDR identify and prevent?
TDR tools are designed to identify and prevent a variety of cyberthreats, including advanced threats that evade traditional prevention technologies. TDR tools offer visibility into stealthy attacks to enable faster response and reduce business disruption and risk.
TDR tools detect and mitigate the following threats:
- Malware. Malware is any form of malicious software, including spyware and Trojans, designed to infect systems and networks and steal data.
- Ransomware. Threat actors use this type of malware to encrypt and exfiltrate business-critical data and then demand the victim pay to decrypt the data and/or prevent the attackers from selling it.
- Phishing. The most popular form of social engineering, phishing attacks trick users into giving up sensitive information and account credentials, which attackers then use to install malware or infiltrate systems.
- Distributed denial-of-service (DDoS) attacks. DDoS attacks flood systems with traffic to overwhelm services and disable servers.
- Botnets. A botnet is a network of malware-infected devices that attackers use to conduct additional actions, such as send spam emails, conduct DDoS attacks, steal data or money, or perform cryptojacking.
- Advanced persistent threats (APTs). APTs are cyber attacks in which malicious actors gain access to an organization's network to steal data over a prolonged period of time.
- Zero-day threats. A zero-day is a security flaw in software, hardware or firmware that developers are unaware of and, therefore, have not patched.
- Living-off-the-land attacks. Living-off-the-land attacks involve malicious actors abusing legitimate tools present in a network to compromise an organization.
Threat detection and response features and capabilities
An effective TDR program integrates a host of strategies and tools that work together to help organizations minimize risk. Key TDR components and features include the following:
- Real-time monitoring. Among the most critical components of TDR is real-time monitoring capabilities. Monitoring should extend to networks, endpoints, applications and user behaviors to identify anomalies and IOCs. It enables early detection of stealthy threats based on unusual activity. Real-time monitoring usually includes integration with SIEM systems for event correlation.
- Threat intelligence. Threat intelligence informs threat detection systems about the latest tactics, techniques and procedures used by threat actors. Properly integrating threat intelligence feeds helps to rapidly detect and identify nascent attack techniques.
- Threat hunting. Detecting threats as they come isn't enough to minimize risk. TDR tools also actively look for IOCs and anomalous activity on a network via threat hunting, the process in which defenders proactively search for breaches or signs of breaches in the network.
- Root cause analysis. Beyond hunting for and identifying threats, TDR forensic capabilities help with root cause analysis, the process in which security analysts determine the cause of an incident.
- Sandboxing. TDR programs can include sandbox capabilities that enable security teams to apply analytics and machine learning techniques on potentially malicious code and operations in an isolated environment. Sandboxing limits risk, while enabling teams to evaluate the impact of and conduct analysis on specific security threats.
- Automated response. TDR platforms can automatically isolate and block threats, thus enabling faster mean time to detect. TDR tools also integrate with security orchestration, automation and response (SOAR) platforms to enable faster mean time to respond.
- Vulnerability management. TDR requires some form of vulnerability management to enable SOC teams to identify and remediate weaknesses attackers could exploit.
Types of threat detection and response tools
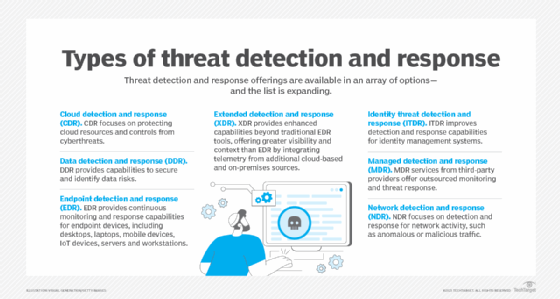
A variety of TDR technologies are available. These vary based on the scope of their detection and response capabilities, as well as the types of systems they protect. TDR options include the following:
- Cloud detection and response (CDR). CDR focuses on protecting cloud resources and controls from cyberthreats.
- Data detection and response (DDR). DDR provides capabilities to secure and identify data risks.
- Endpoint detection and response (EDR). EDR provides continuous monitoring and response capabilities for endpoint devices, including desktops, laptops, mobile devices, internet of things devices, servers and workstations.
- Extended detection and response (XDR). XDR provides enhanced capabilities beyond traditional EDR tools, offering greater visibility and context than EDR by integrating telemetry from additional cloud-based and on-premises sources.
- Identity threat detection and response (ITDR). ITDR provides capabilities to improve detection and response capabilities for identity systems.
- Managed detection and response (MDR). MDR services from third-party providers offer outsourced monitoring and threat response.
- Network detection and response (NDR). NDR focuses on detection and response for network activity, such as anomalous or malicious traffic.
- User and entity behavior analytics (UEBA). UEBA technologies monitor for abnormal user or entity behaviors that could indicate a threat. Entities include processes, applications and devices. UEBA systems generally do not automatically respond to threats unless integrated with another tool, such as SOAR, or if they are a component of a different detection and response product.
Threat detection and response best practices
Effective TDR enables security teams to stay ahead of advanced threats designed to evade traditional security defenses. Follow these best practices to reduce cybersecurity risks and get the most out of a TDR program:
- Establish baseline behavior. Document a baseline behavior profile of regular activity across an IT system. Examine and record data points, such as traffic flow, data access and application use, to flag common and expected patterns. Using this profile, security teams can quickly detect unusual or anomalous activity.
- Ensure continuous real-time monitoring. Monitoring is a critical capability for TDR to work effectively. Monitor networks 24/7 to spot potential issues.
- Integrate threat intelligence into the workflow. Integrate threat intelligence into workflows in actionable ways. Knowing about a threat is useful; being ready to act on that intelligence is better.
- Conduct vulnerability assessments. Regularly scan systems, networks and applications for known vulnerabilities to identify weaknesses before attackers.
- Threat hunt regularly. Regularly perform threat hunting activities. Always be hunting for IOCs and potential risks.
- Train employees and plan for successful outcomes. Train security staff how to properly use deployed TDR tools. Consider using simulated scenarios, such as tabletop exercises, so staff can practice response efforts. Ongoing education and security awareness programs also keep security teams informed of the latest threats.






