- Share this item with your network:
- Download
Information Security
- Editor's letterPlan now for the future of network security
- Cover storyAI-powered cyberattacks force change to network security
- InfographicThe state of cybersecurity risk: Detection and mitigation
- Q&AOne security framework may be key to cyber effectiveness
- ColumnWhy nation-state cyberattacks must be top of mind for CISOs
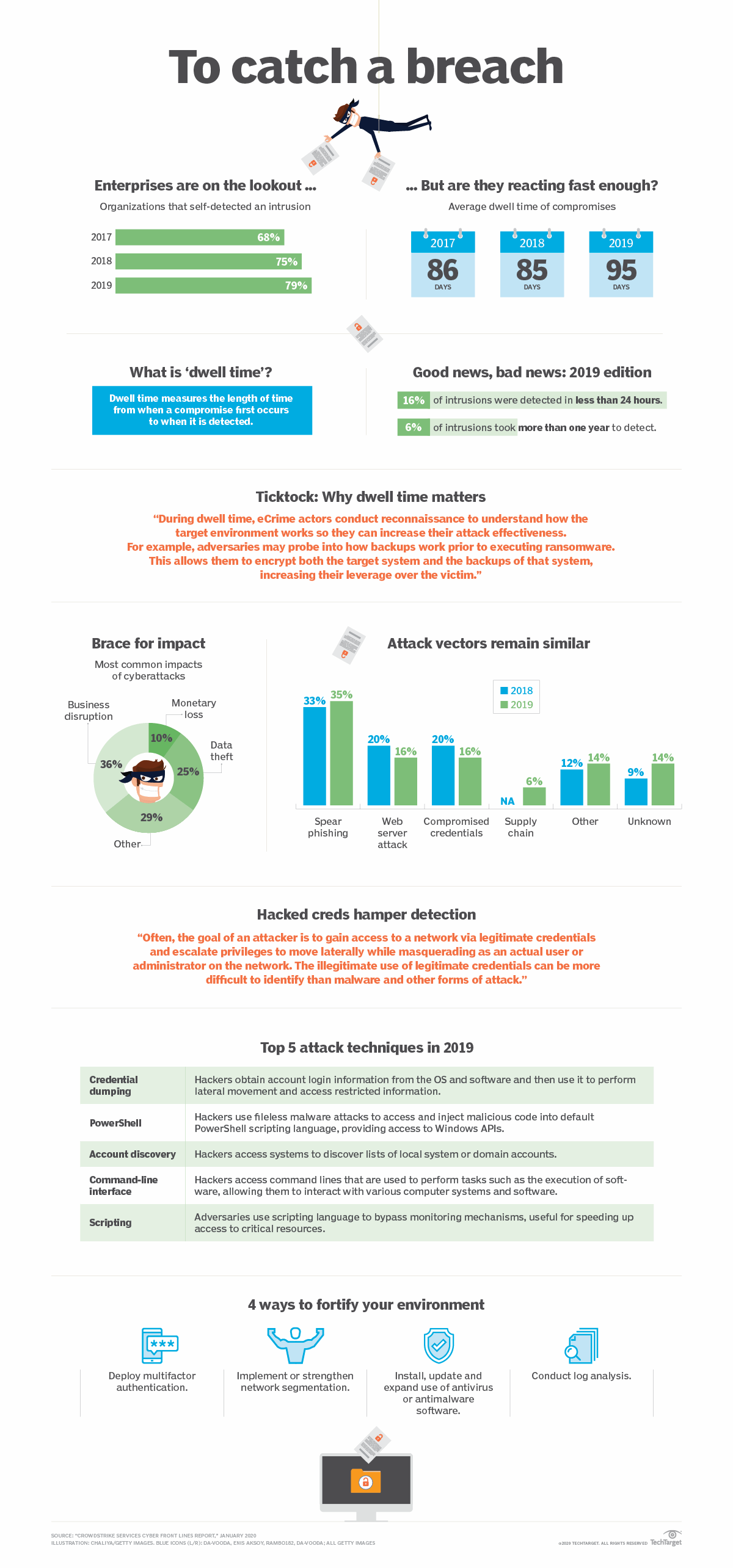
The state of cybersecurity risk: Detection and mitigation
Hackers will always try to creep in, and many will succeed. That's why effective detection and mitigation are essential. How are enterprises faring?Attackers lurk in the shadows. Their techniques are constantly evolving, and visibility into threats is limited. In short, information security is not known for clarity. But when it comes to guidance for enterprises seeking to manage cybersecurity risk, it doesn't get any clearer than this: "The ability to quickly detect an intrusion is the foundation of rapid response and remediation," wrote the authors of CrowdStrike's 2020 "CrowdStrike Services Cyber Front Lines Report."
Of course, detecting breaches is easier said than done. The average breach goes unseen for more than three months, and that's no accident, according to the CrowdStrike report.
"State-sponsored threat actors are applying countermeasures that allow them to remain undetected for a protracted length of time -- particularly in environments protected by legacy security technologies," the report stated.
Check out our graphic to learn more about the state of detection and mitigation, including why these steps need to be the cornerstone of any cybersecurity risk posture today.