kentoh - Fotolia
Hackers embrace cryptocurrency laundering to evade the law
Cybercriminals are turning to cryptocurrency laundering methods to hide illicit proceeds as law enforcement agencies find success in tracing bitcoin transactions.
As law enforcement agencies have increased their ability to track bitcoin transactions, cybercriminals are turning to "mixers" and other methods of cryptocurrency laundering to hide their illicit proceeds.
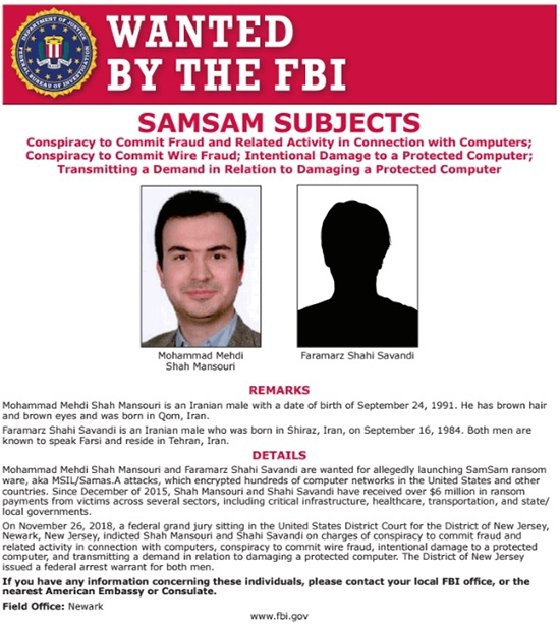
One illicit operation dependent on cryptocurrency is ransomware attacks, where threat actors often demand payments in bitcoin, the most popular form of cryptocurrency. And while at one time, bitcoin transactions were thought to be anonymous, law enforcement agencies over the years have become increasingly proficient at tracing ransomware payments and identifying perpetrators. That has led to the indictments of alleged operators of some of the most notorious cybercrime campaigns in recent memory, including SamSam ransomware and the GameOver Zeus botnet.
With bitcoin achieving mainstream acceptance over the last decade, threat actors used popular cryptocurrency exchanges to hide their profits. But cybercriminals have adapted in recent years by embracing new cryptocurrency laundering techniques to evade detection, including "tumblers" or mixers, which are services designed to obscure the trail of coins, according to John Fokker, McAfee's principal engineer and head of cyber investigations.
"For a long time, it was difficult to link certain payments in the blockchain to exchanges. However, with mainstream BTC acceptance, clustering and attribution techniques it has become easier to identify certain payments," Fokker said in an email. "Bitcoin tumblers are a reaction to this and nowadays play an important role in the cybercriminal ecoclimate as the No. 1 way for criminals to make sure that ransomware payments aren't tracked."
Law enforcement tackles cryptocurrency laundering
During the RSA Conference 2020, two sessions focused on the topic: "Feds Fighting Ransomware: How the FBI Investigates and How You Can Help," led by FBI special agent Joel DeCapua and "Hi-Tech Mass Extortion: Lessons from the SamSam Ransomware Prosecution," led by William Hall, senior counsel for the U.S. Department of Justice, Computer Crime and Intellectual Property.
According to Hall, ransomware is a synergy of three things: internet, encryption and cryptocurrency. "Without these three things, ransomware would not be as effective. Maybe it wouldn't exist at all," Hall said in the session.
Bitcoin transactions have also helped law enforcement agencies identify threats actors and recoup payments made by victims. For example, in the case of the SamSam ransomware attacks, payments made by victims were an important piece of the investigation, Hall said.
"Bitcoin was a big part of the SamSam attack. We could use tools to analyze blockchain ledger and gain visibility into movement of funds from origin to destination," Hall said during his session. "Evidence of these financial transactions helped us in our efforts to identify the perpetrators."
A report by blockchain analytics company Chainalysis, titled, "The 2020 State of Crypto Crime," showed a total of $11.5 billion worth of cryptocurrency transactions last year were associated with criminal activity.
"The very fact that we can quantify and investigate crypto crime so effectively demonstrates cryptocurrency's inherent transparency," said Kim Grauer, head of research at Chainalysis. "This kind of analysis would never be possible in fiat currency, but it is in cryptocurrency with the right tools since every transaction goes into a public ledger."
Those public ledgers have also been influential in solving ransomware investigations. "We are really interested in ransom wallets," DeCapua said during his session. "Incident response companies can track the money. We aren't really interested in who the clients are, we care about where the money went."
Over the last six years, the FBI has traced $144 million worth of ransoms paid in bitcoin alone, DeCapua said. By tracing those proceeds, the FBI also determined that from the actual wallets victims used to pay demands, the money went directly to an exchange.
"This is a real problem," DeCapua said in his session. "One of the FBI's major challenges is the fact that it's easy to launder money. A lot of virtual currency exchanges do no anti-money laundering [measures], so it's easy."
One example was BTC-e, a virtual currency exchange that didn't ask for personal information or adhere to regulatory compliance. During the Black Hat 2017 conference, an engineer from Google presented a study that concluded that 95% of ransomware was cashed out via BTC-e, one of the most popular virtual currency exchanges until it was taken down by the IRS in 2017, DeCapua said during his session.
And according to Chainalysis, the use of exchanges is only increasing.
"While exchanges have always been a popular off-ramp for illicit cryptocurrency, they've taken in a steadily growing share since the beginning of 2019. Over the course of the entire year, we've traced $2.8 billion in bitcoin from criminal entities to exchanges," Chainalysis wrote in the report.
Tumblers, mixers and gift cards
Most cryptocurrency exchanges are cooperative with law enforcement, but the FBI is aware that some do not comply with U.S. laws and regulation. Even with cooperation, there are no guarantees because threat actors will find additional methods to hide their illegal funds.
"As law enforcement agencies might compel exchanges into disclosing the identity of their clients, some operators deposit their bitcoins into mixers, services that obfuscate bitcoin trails by intermixing bitcoin from multiple sources," DeCapua said in his session.
The use of mixers is increasing, according to Grauer.
"A small but significant, in 2019, increasing portion of all funds stolen via hacks are passed through third-party mixers or CoinJoin wallets to obscure their illicit origins," Grauer said. "While there are legitimate uses for mixers, the data makes it clear that they're increasingly being utilized by hackers in particular to obfuscate the path of stolen funds prior to cashing out. Exchanges can likely stop some of these cash outs and help law enforcement claw back stolen funds by halting suspicious transactions from mixers."
The reason for only a slight increase is because there's no recourse if a mixing service rips off a client.
"Mixers weren't as predominant as I thought they would be," DeCapua said in his session. "What's stopping a bitcoin mixer from stealing your money? It happens all the time."
In 2019, law enforcement agencies were successful in the take down of one mixing service, Bestmixer. McAfee had alerted agencies when they found Bestmixer's page, which described evading anti-money laundering policies and making funds untraceable.
Bestmixer was the third largest tumbling service in the world, according to Fokker.
Mixers and exchanges aren't the only route for money laundering. Another common method among cybercriminals is to purchase gift cards or prepaid credit cards. For example, the U.S.-designated North Korean state-sponsored group Lazarus, transferred $1.4 million worth of bitcoin into prepaid Apple iTunes gift cards, according to a the U.S. Department of the Treasury's Office of Foreign Assets Control.
"Purchasing gift cards or prepaid credit cards with cryptocurrency and then anonymously selling those gift cards online for U.S. dollars is a method we've seen frequently. Cybercriminals are always looking for creative ways to integrate cryptocurrency derived from illegal criminal proceeds into the traditional banking industry," the FBI said in a statement to SearchSecurity.
Some cybercriminals have ditched bitcoin for cryptocurrencies that offer more anonymity. For example, Bleeping Computer reported the Sodinokibi ransomware group last month announced on a hacker forum that they are starting to accept the Monero cryptocurrency to make it harder for law enforcement to trace them and plans to stop accepting bitcoin payments.
"Criminals will exchange BTC into Monero or Dash in order to evade the blockchain tracking," Fokker said in an email. "Although the large majority of cryptocurrency used is still BTC because it's easier to obtain, less volatile and easier to exchange, ... we do see, for instance, ransomware families encouraging the use of other currency such as Monero. Time will tell if this will overtake the BTC, since ransomware payments are strongly driven by the victim's capability to obtain certain currency."