
Maksim Kabakou - Fotolia
Emotet botnet hacked, malware replaced with humorous GIFs
Malware distribution network Emotet has been hacked by a potential threat actor of unknown origin, with malware payloads now being replaced with GIFs of James Franco and others.
Users who have been subjected to strange GIF files in recent days may have dodged a major bullet.
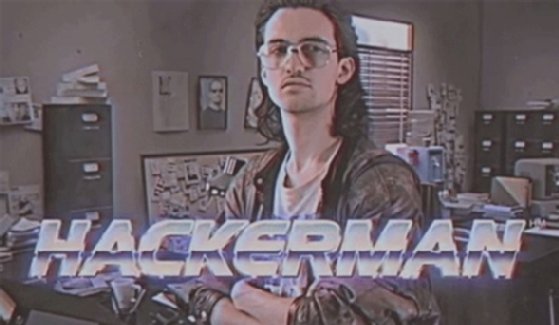
The infamous malware distribution network Emotet was hacked by unknown individuals, with a number of distribution files being replaced by humorous GIFs. As a result, instead of being hit with malware, users who click on malicious links from Emotet spam have been seeing images of James Franco and others such as "Hackerman" from the 2015 film "Kung Fury."
Members of "Cryptolaemus," an informal group of security researchers who track Emotet, noted on Twitter last Friday that Emotet activity had suddenly declined and that the "Hackerman" GIF was loading instead of malware in around 25% of the cases. Microsoft senior threat intelligence analyst Kevin Beaumont noted in a Medium post that he "flagged a few times over the years, the last time in 2019, that Emotet uses an insecure malware distribution system."
In a tweet late last year, he said, "The Emotet payload distribution method is super insecure, they deploy an open source webshell off GitHub into the WordPress sites they hack, all with the same password, so anybody can change the payloads infected PCs are receiving."
Originally started as a malware strain and banking Trojan first detected in 2014, Emotet is now known for its series of botnets of computers infected by its malware. It's known for its service model, where it offers access to said infected computers to threat actor groups like the Ryuk ransomware gang.
In a tweet dated July 17, Microsoft reported that Emotet had resurfaced "in a massive campaign" after several months of quiet.
In a blog post last week, Malwarebytes Labs listed several indicators of compromise for Emotet, including a serious of malicious IP addresses, binaries and domains that organizations should add to their block lists to defend against the botnet's phishing emails or spam.
In the Medium post, Beaumont wrote that given malware is being replaced by GIFs a few minutes after updating their botnet, and given a quarter of all malware is being replaced, the likely culprit is either Emotet themselves, other threat actors or security researchers. But despite the reprieve from Emotet malware, he raised a concerning possibility.
"It does raise a really worrying question -- Emotet distributes a lot of emails (they have scale)," Beaumont wrote, "and anybody being able to replace the payloads for something less detectable (other malware) could be problematic."






