cyber insurance
What is cyber insurance?
Cyber insurance, also called cyber liability insurance or cybersecurity insurance, is a contract an entity can purchase to help reduce the financial risks associated with doing business online. In exchange for a monthly or quarterly fee, the insurance policy transfers some of the risks to the insurer.
Cybersecurity policies can change from one month to the next, given the dynamic and fluctuating nature of the associated cyber-risks. Unlike well-established insurance plans, underwriters of cyber insurance policies have limited data to formulate risk models to determine insurance policy coverages, rates and premiums.
Origins of cyber insurance
Cyber insurance emerged in the late 1990s as a result of the growing reliance on technology and the increase of cyberthreats. Initially, it focused on data breaches and computer attacks, but over time, expanded to cover a broad range of cybercrimes, including ransomware, cyber extortion, social engineering attacks, system failures and business interruptions from cybersecurity incidents.
Cyber insurance has its origins in errors and omissions (E&O) insurance, a separate form of insurance that protects against faults and defects in the services a company provides. E&O insurance is analogous to product liability policies for companies that sell physical or digital products. While some cyber insurance policies contain specific provisions for E&O, most providers sell these as separate and distinct policies. E&O insurance doesn't cover third-party data loss, such as customer credit card numbers; customers needing such protection can purchase a cyber insurance policy that covers it.
This article is part of
What is risk management and why is it important?
Today, cyber insurance is essential for mitigating financial and reputational damage and ensuring a resilient digital environment.
Why is cyber insurance important?
The loss, compromise or theft of electronic data can have a negative effect on a business, including the loss of customers and revenue. Business owners could be liable for damages stemming from the theft of third-party data.
In 2011, hackers breached Sony's PlayStation Network, exposing the personally identifiable information (PII) of 77 million PlayStation user accounts. The breach prevented users of PlayStation consoles from accessing the service, an outage that lasted for 23 days. Sony incurred more than $171 million in costs related to the breach. Portions of this cost could have been covered by a cyber insurance policy, but Sony didn't have one in place. A court case ruled that Sony's insurance policy covered damage to physical property only, leaving Sony to incur the full amount of costs related to cyber damages.
Cyber insurance provides the following benefits:
- Protection against cyber risks. Cyber liability coverage is important to protect businesses against the risk of cyber events, including those associated with terrorism. Cyber insurance can provide network security coverage and assist in the timely remediation of cyber attacks and incidents.
- Financial protection. Cyber insurance offers financial security against damage caused by cyber incidents. This includes expenses for investigations, credit monitoring services and potential legal responsibilities, among other costs associated with data breaches. In addition, it can provide compensation for business interruption, loss of revenue and computer system restoration.
- Legal support. Legal assistance is frequently included with cyber insurance, which helps businesses navigate the complicated legal system around cyber events. It can pay for the costs of legal counsel, legal compliance with regulations and prospective lawsuits brought about by data breaches or privacy violations.
- Peace of mind. Cyber insurance provides businesses and individuals with a sense of security by guaranteeing their financial stability in the case of a cyber crisis. This lets businesses concentrate on their core business operations without having to constantly worry about the possible financial and reputational consequences of a cyber attack.
- Highlights commitment to security. Cyber insurance coverage can make businesses and organizations stand out by highlighting their dedication to safeguarding client data and being proactively ready for cyber attacks. It also exhibits a commitment to cybersecurity, which can boost reputation and confidence among customers, stakeholders and partners.
How does cyber insurance work?
Cyber insurance policies are sold by many of the same providers that offer related business insurance, such as E&O, business liability and commercial property insurance. Most policies include first-party coverage, which applies to losses that directly affect a company, and third-party coverage, which applies to losses suffered by others from a cyber event or incident, based on their business relationship with that company.
Cyber insurance policies can help cover the financial losses that result from cyber events and incidents. In addition, cyber-risk coverage often helps with the costs associated with remediation, including payment for legal assistance, investigators, crisis communicators and customer credits or refunds.
Who needs cyber insurance?
While every organization's risk profile is unique, most companies could benefit from purchasing cyber insurance. A wide range of industries that are good candidates for cyber insurance include the following:
- Businesses of all sizes. Organizations that create, store and manage electronic data online -- such as customer contacts, customer sales, PII and credit card numbers -- could benefit from cyber insurance. In addition, e-commerce businesses can benefit from cyber insurance, since downtime related to cyber incidents can cause a loss in sales and customers. Similarly, any business that stores customer information on a website can benefit from the liability coverage provided by cyber insurance policies.
- Healthcare providers. Due to the sensitive information and patient data they maintain, healthcare companies are frequently targeted with data breaches and cyberthreats. According to a data breach report by IBM, the average cost of a healthcare breach is $10 million annually. To reduce the financial and legal risks connected to data breaches and Health Insurance Portability and Accountability Act violations, cyber insurance is essential for healthcare organizations.
- Financial institutions. Banks and credit unions are also prime targets for cybercriminals due to their sensitive nature of dealing with customer's personal information such as social security numbers. Therefore, cyber insurance can help these institutions recover from financial damages caused by cyber attacks.
- Government agencies. A huge amount of private information is handled by government agencies on many different levels. Cyber insurance can help government institutions guard against cyber attacks and assure the continuity of public services.
- Educational institutions. Educational institutions such as schools, colleges and universities typically store large amounts of personal and academic records for both employees and students and are therefore good candidates for cyber insurance.
- Companies with high revenue. Due to the potential financial rewards, companies with significant revenue streams can be great targets for hackers. To guard against the financial damages brought on by cyber attacks and data breaches, organizations with high revenue should consider purchasing cyber insurance.
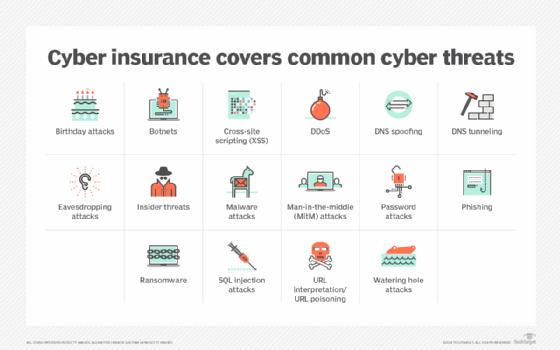
What is covered and not covered by cyber insurance?
In the U.S., many major insurance companies offer customers cyber insurance policy options. Depending on the price and type of policy, the customer can expect to be covered for extra expenditures resulting from the physical destruction or theft of IT assets. Such expenditures typically include costs associated with the following:
- Meeting extortion demands from a ransomware attack.
- Notifying customers when a security breach has occurred.
- Paying legal fees levied as a result of privacy violations.
- Hiring computer forensics experts to recover compromised data.
- Restoring identities of customers whose PII was compromised.
- Recovering data that has been altered or stolen.
- Repairing or replacing damaged or compromised computer systems.
Traditional insurance policies typically exclude cyber risks, and this has led to the growth of cybersecurity insurance as a separate type of coverage. Potential customers include any company that accepts digital payments or stores PII about customers, including medical and financial information.
Some cyber insurance policies cover the cost of providing credit monitoring services for customers affected by a data breach. In September 2017, Equifax, a consumer credit reporting agency, suffered a data breach that exposed the personal information of 147 million people. In 2019, Equifax reached a settlement with the U.S. Federal Trade Commission. As part of the settlement, Equifax agreed to spend $425 million to provide free credit reporting, cash payments for those already enrolled with a credit monitoring service, reimbursement for time or money spent on recovering from identity theft and free identity restoration services. A cyber insurance policy could have paid for part of the cost of Equifax's settlement, assuming the circumstances of its data breach were covered by such a policy.
Many entry-level cybersecurity insurance policies only cover first-party losses, but some insurers are beginning to offer policies that cover third-party liability losses.
Many cybersecurity policies exclude preventable security issues caused by humans, such as poor configuration management or the careless mishandling of digital assets. Other issues excluded by cybersecurity policies include the following:
- Preexisting or prior breaches or cyber events, such as incidents that occurred before the policy was purchased.
- Cyber events initiated and caused by employees or insiders.
- Infrastructure failures not caused by a purposeful cyber attack.
- Failure to correct a known vulnerability, such as a company that knows a vulnerability exists, fails to address it and is then compromised from that vulnerability.
- The cost to improve technology systems, including security hardening in systems or applications.
- The loss of intellectual property value such as proprietary information, trade secrets or other priceless intangible assets.
How to choose a cybersecurity insurance policy and how much does cyber insurance cost?
Typically, cyber insurance pricing is based on the insured entity's annual revenue, industry, extent and type of coverage and the size of the organization. However, the past few years have witnessed a notable surge in cyber insurance premiums and payouts, a trend attributed to the expanding attack surfaces and evolving adversary techniques. Taking these factors into consideration, a typical policy can cost anywhere from $500 to $5,000 or more a year according to Progressive Casualty Insurance Company.
To qualify for cyber insurance coverage, the individual or entity typically must submit to a security audit by the insurance company or provide documentation with the assistance of an approved assessment tool, such as that offered by the Federal Financial Institutions Examination Council. The results from a security audit or the documentation from approved assessment tools can factor into the types of coverage provided by the cyber insurance carrier, as well as the cost of the premiums.
Since the cyber insurance market is relatively young, many companies are choosing to forego this type of insurance because of its uncertain return on investment. In the U.S., the Cybersecurity and Infrastructure Security Agency, which operates under the Department of Homeland Security, is encouraging businesses to improve their cybersecurity in return for more coverage at more affordable rates.
Cybersecurity policies can vary widely from one provider to the next. To choose a policy, companies should closely review policy details to ensure it contains the necessary protections and provisions. In addition, companies should evaluate whether policies protect against known and emerging cyber incidents and threat profiles.
The cyber insurance industry is expanding but it comes with some pitfalls. Delve into four recommendations for securing the most suitable cyber insurance coverage for your requirements.







