Red team vs. blue team vs. purple team: What's the difference?
Red team-blue team exercises simulate attacks on enterprise networks. What does each team do? Where do purple teams fit in? Find out here.
Conducting red team vs. blue team exercises can be an eye-opening experience. Whether they're testing an organization's cybersecurity defenses against threats or assessing the talent of security team members, such simulated attacks can be beneficial for companies of all shapes and sizes.
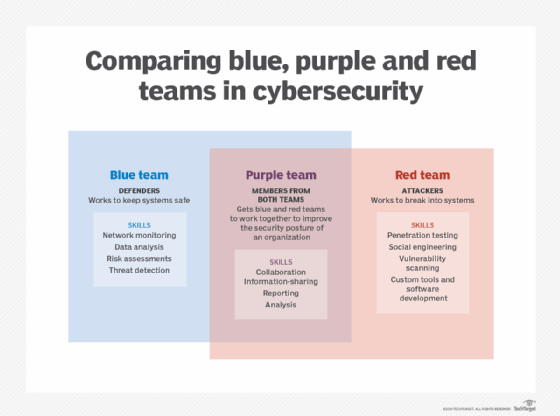
These exercises involve two teams. Tipping their hats to their military ancestors, red teams are the adversaries, with the blue team the defendants. Recently, the term "purple team" has entered the mix.
Read on to learn more about each team and how each works to benefit your security operations center.
What is a red team?
The red team attacks and attempts to break the blue team's defenses. Ideally, these ethical hackers are unaware of an enterprise's defense mechanisms, so their services are often outsourced to a third party.
Red teams use real-world cyber attack techniques to exploit weaknesses in a company's people, processes and technologies. They circumvent defense mechanisms, aiming to infiltrate corporate networks and simulate data exfiltration -- all without being noticed by the blue team.
Common red team techniques include:
- penetration testing;
- phishing, social engineering and other forms of credential theft mechanisms;
- port scanning; and
- vulnerability scanning.
In addition to these common hacker techniques, red team members use custom-made tools to get into networks, and then often escalate privileges to successfully breach the company.
Because exercises are performed to improve security, red team members write up reports post-attack, including details about techniques used, vectors targeted, and successful and unsuccessful attempts. The reports should also include recommendations about how to strengthen the organization's security posture, ensure defenses are up to par and bolster systems from future threats. The reports help blue teams understand where gaps in coverage exist, how defenses failed and where security needs to be tightened.
What is a blue team?
The blue team is responsible for regularly analyzing enterprise systems to properly protect them, identify vulnerabilities, and evaluate the effectiveness of security tools and policies.
Blue team tasks include:
- monitoring corporate networks, systems and devices;
- detecting, mitigating, containing and eradicating threats and attacks;
- collecting network traffic and forensic data;
- performing data analysis; and
- conducting internal and/or external vulnerability scans, DNS audits and risk assessments.
Blue teams analyze information from these tasks and then update security software, hardware and policies to better protect against potential future attacks.
Blue team members also:
- create, configure and enforce firewall rules;
- set and implement device and user access controls, often using the principle of least privilege;
- keep enterprise software -- production and security -- patched and up to date;
- deploy IDS/IPS and/or endpoint detection and response systems;
- segment networks;
- perform reverse engineering on cyber attacks;
- conduct DDoS testing; and
- develop response and remediation policies to ensure systems securely and quickly return to their normal operating state after a security incident.
The blue team is also instrumental in assessing and addressing human vulnerabilities. Staying up to date with the latest phishing and social engineering scams is a must for blue teams to effectively hold security awareness trainings and put end-user policies, such as password policies, in place.
Blue teams will notify senior management when risks are found to assess if a risk should be accepted or if a new policy/control needs to be adopted to mitigate it.
Like red teams, after an exercise is completed, blue teams gather evidence, logs and data to write reports about their experiences and findings, as well as develop a list of actions to be taken.
What is a purple team?
Calling the purple team a "team" is a bit misleading. The purple team is, in fact, not a standalone team but a mix of blue and red team members.
While red and blue teams have the same goal of improving the security of an organization, too often both are unwilling to share their "secrets." Red teams sometimes will not disclose methods used to infiltrate systems, while blue teams won't say how red team attacks were detected and defended against.
However, sharing these secrets is critical to strengthening the company's security posture. The value of red and blue teams is nil if they don't share their research and reporting data. This is where the purple team steps in. Purple team members get their red and blue teammates to work together and share insights about their resources, reporting and knowledge. To do so, purple teams should focus on fostering communication and collaboration between the red and blue teams.
Benefits of red team-blue team exercises
Red teams and blue teams each have their own individual benefits, but combined the two offer even greater value. In addition to identifying vulnerabilities and helping ensure system security, red team-blue team exercises can:
- foster collaboration;
- raise healthy competition;
- identify where training exercises are needed;
- encourage employees to think outside the box;
- help employees learn new real-world security skills in real time;
- improve threat detection and response times; and
- continuously improve an organization's security posture.








