organizational network analysis (ONA)
Organizational network analysis (ONA) is a quantitative method for modeling and analyzing how communications, information, decisions and resources flow through an organization. It is used in a variety of fields, including business management and the social and behavioral sciences. Practitioners use ONA to gain a better understanding of the relationships that affect the effectiveness of individuals and groups.
To analyze information, ONA uses software to pull the data from sources such as surveys.
Basics of organizational network analysis
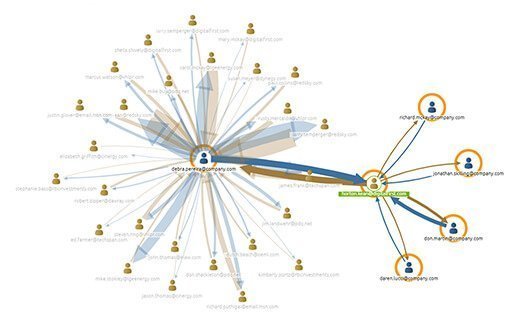
ONA relies heavily on diagrams that depict the people or groups (nodes) that play a critical role in providing information, ideas or decisions, and the connections (ties) between them.
There are three main kinds of nodes, according to the Deloitte consulting firm, one of the main proponents of ONA. Central nodes are influential people who seem to know everyone, are up to date on important news and have lots of information to share. They can be located anywhere in a hierarchy. Knowledge brokers, in contrast, facilitate information sharing by serving as bridges between nodes. Peripheral nodes are low-profile people with poor or nonexistent connections to the organization.
The analysis results in metrics that help to gauge the nature and health of a network. "Between-ness" measures the extent to which a node interacts with other nodes. A higher number can be an indicator of a thriving network but also provide an alert to a potential bottleneck. Another metric, network density, calculates the percentage of links to the total number possible among all the nodes. The centrality metric uses between-ness scores to determine whether the network is too centralized, among other things.
Further conclusions can be drawn from the analysis. For example, knowledge brokers often have important connections to outside information and expertise that can go underused if the broker lacks strong internal ties. Peripheral nodes are at risk of leaving the organization, which can be a detriment if their skills are highly valued. The insights from ONA may also reveal that people with formal authority and titles are not the real leaders of the organization. Identifying the leaders can, for example, speed buy-in and adoption of a new initiative.
Applications of ONA
Organizational network analysis has numerous uses in talent management, and is considered by some experts to be a sub-discipline of people analytics. For example, companies can use it to spot exclusionary tendencies that might indicate discrimination and bias. They can also analyze the influence and networking skills of external job candidates, which some studies say are predictors of career success, and can benefit the hiring organization. ONA can also help identify internal candidates for job openings and promotions.
Workforce planning is another talent management function that can benefit from ONA. Managers can use the analysis to decide where to reassign people so they collaborate more effectively for the least amount of resources. ONAs can help identify where work is being done and who is doing it, which can affect decisions about hiring, promoting and developing employees.
ONA can also help boost employee engagement by analyzing communication patterns and by providing feedback mechanisms that measure employee sentiment. The technology can even purportedly identify areas of unusually high stress in an organization, which in turn can indicate fraud or other undesirable behaviors.
Companies that are considering reorganizing departments and business units can use organizational network analysis before making decisions and building a formal org chart.
During mergers and acquisitions, ONA can find people with different titles who perform similar roles that could become redundant, and then move them into roles that add more value.
Some proponents of ONA claim it is indispensable in ensuring that increasingly decentralized and less hierarchical organizations can still function effectively. ONA can confirm, for example, that knowledge is being shared among teams and that sufficient coordination and reporting are maintained.
ONA can also help companies with globally dispersed teams and offices to disseminate information, such as engineering schematics and data, by understanding the informal networks that cut across formal departments and product lines. Some companies have reduced project times and boosted profits, according to ONA advocates.
ONA is also used by nonprofits and nongovernmental agencies in fields like economic development to understand systemic issues of the communities they serve. Such agencies also use ONA to design projects and scale up techniques that have succeeded locally.
In the social sciences, ONA is often called social network analysis (SNA), a discipline that originated in the early 20th century. Some consultants and academics specialize in ONA or SNA.
ONA technology
ONA is typically performed in software sold by niche vendors or offered for free from academic and research institutions.
The software captures data from emails, collaboration tools such as Enterprise social networking and feedback technologies, including employee surveys, and applies data analytics to draw conclusions.
ONA software typically also has a component for automating surveys, which are essential in data gathering. The surveys ask respondents questions designed to reveal the nodes and ties in their networks, such as who is on their work team, where they go to get information and who they collaborate with most often.
The software also includes data visualization tools that provide a graphical depiction of networks and ONA metrics. A network map (see figure) is typically created to show the main nodes, ties and information flows at a glance.
KeenCorp, Syndio and TrustSphere are among the major vendors of ONA software, according to analyst firm Bersin by Deloitte. In addition, Microsoft acquired software vendor VoloMetrix and rolled its technology into the Office 365 suite to create a search and presentation tool called Delve that employs ONA.
American Express, BP, Cigna, Cisco, GM, IBM, Microsoft and TD Bank are among the large companies using or exploring ONA tools, according to analysts and ONA software vendors.








