Security automation tools and analytics reshape SecOps efforts
To transition from being reactive to proactive in terms of cybersecurity threats, check out how SecOps teams can use security analytics and automation tools to make the change.
As security tools get smarter -- meaning more automated and better able to provide genuine insight into the security environment -- cybersecurity professionals must evolve, too. Long gone are the days when a $500-$1,000 per hour cybersecurity professional spent hours reviewing log files.
At the same time, the staffing shortage for cybersecurity leaders is acute, which makes it difficult for CISOs to find cybersecurity professionals in the first place.
But, now that machines can do some of the thinking, cybersecurity professionals need to rethink how they can best utilize insights provided by security automation tools and analytics to shut down existing and prospective attacks quickly and effectively.
To take advantage of the strengths of the tools, cybersecurity professionals first need to reconsider security operations (SecOps). In particular, they need to move from being reactive in responding to threats and alerts to being proactive in planning ahead to avoid security incidents.
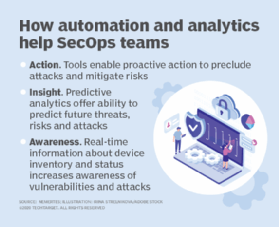
To understand how to go from reactive to proactive mode, security pros need to review the primary benefits automation and analytics provide. Check out the following steps to make the transition to proactive SecOps mode.
Step 1. Awareness of the current state
One of the first areas automation can help with is awareness. Awareness means simply having an accurate understanding of the current state. From a cybersecurity perspective, awareness encompasses several aspects:
- Asset management. Most companies lack up-to-date knowledge of their environments, including which assets are highest priority. Automated asset management tools can keep track of assets in real time, whether that means devices, workloads, containers or data repositories.
- Threat detection. Most cybersecurity professionals are familiar with old-school options, such as intrusion detection and prevention systems and SIEM. But newer technologies, such as extended detection and response (XDR), can provide insight into potential threats and attacks underway from endpoints. As discussed below, they can also help with rapid responses to such attacks.
- Risk analysis. It's not enough to be aware of the environment and potential or actual attacks. Awareness also requires cybersecurity professionals to understand which attacks are most threatening and which resources present the greatest risk of compromise. They need to be able to translate that risk into business terms. Automated risk dashboards can provide that information.
Some of these tools align with frameworks such as the MITRE ATT&CK framework or the NIST Cybersecurity Framework; others provide their own frameworks.
Step 2. Insight into what could happen
Once cybersecurity professionals have an accurate understanding of what's going on from the device level to the risk and impact analysis, the next step is to gain a credible understanding of what is likely to happen. Predictive analytics come in here. Many of the threat intelligence networks and some of the tools that provide awareness also incorporate predictive analytics to advise cybersecurity professionals about which threats might be most likely and most damaging. This enables them to proactively prevent those attacks.
Step 3. Action for automated response
Finally, automation can bridge the gap between knowledge and impact. With automation, security tools can automatically take preemptive steps to lock down systems, dispel intruders and neutralize attacks. Tools such as security orchestration, automation and response can equip security operations centers with the ability to take automated action in response to a breach. And technologies like XDR also include an element of automated response.
The impact of automation on SecOps
The availability of these tools means SecOps teams need to adjust their processes to fully utilize the new capabilities. Some likely changes SecOps teams will want to consider include the following:
- Factor in a regular review of new devices, systems and applications on the organization's resource list. Instead of investing time and energy locating assets, teams can assume they have accurate knowledge of assets and instead review changes they need to make in response.
- Conduct regular war games and simulated attacks that go beyond penetration testing for predicted threats and attacks. If automation is indicating certain attacks are likely, it makes sense to practice a response to uncover any operational or technical weaknesses. Both war gaming and simulated attacks are good ways to proactively identify and remediate vulnerabilities.
- Redesign response processes to factor in automation. As systems begin to include specific responses, it becomes more important to ensure the team is fully aware of the circumstances in which an automated response will or won't kick in and how they should respond. This ensures that handoffs between humans and automated systems are clean and minimize risk.
- Analyze audits. One of the benefits of increased automation and analytics is that auditing can be vastly simplified because every action has a clear digital trail. SecOps teams shouldn't let these digital trails lie unexamined. As part of a monthly or quarterly review, they should analyze the audit trails to see what occurred and whether it aligned to what they expected would occur.
A common theme among all these changes is that they represent a transition from being reactive to being proactive. Instead of being driven to a specific response based on an alert or an issue, SecOps teams have the freedom to conduct post-mortems and plan ahead. The upshot? Automation and analytics can vastly improve the SecOps team's effectiveness but only as long as the team is willing to step up to proactivity.







