Top 10 cybersecurity interview questions and answers
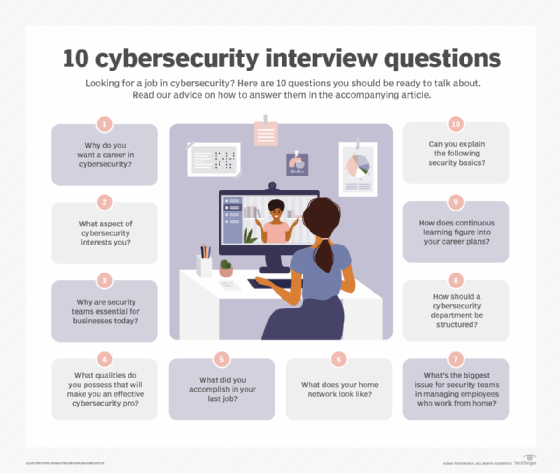
Interviewing for a job in cybersecurity? Memorizing security terms won't cut it. Here are the 10 interview questions you should be ready for -- and how to answer them.
Interviewing for a job in information security can be daunting. There are so many topics candidates are expected to know: DNS monitoring, distributed denial-of-service attacks and data leakage are some of the basics. Job applicants should also be familiar with terms such as encryption, decryption, firewalls and penetration testers -- the security pros who work on red teams.
But, according to experts we interviewed, memorizing hundreds of terms is not the ticket to a successful interview for a cybersecurity job. The best candidates have a sense of what they want to accomplish in the security field and can demonstrate a sincere interest in and concern for how cybersecurity has become a front-burner issue for businesses.
Simone Petrella, president of cybersecurity training and information provider N2K Networks, said she can tell in a matter of minutes if there's a serious candidate in front of her. "If they say they are interested in security because it's the hot field and they want to make money, I know they are not serious," Petrella said. "Candidates need to show they've done some research and have some sense of what aspect of security interests them."
David Wolpoff, former CTO at IBM's Randori cybersecurity unit, pointed to similar telltale attributes of a successful security job candidate.
"A mantra I've picked up from previous teams is passion, capacity and smarts," Wolpoff said. "You're not going to stay current and grow if your only learning time is 9 to 5 -- the security space is too big." That's especially true for aspiring red team applicants. "To become a really awesome hacker, you have to be willing to dig in and learn everything."
In short, come to the interview ready to talk about yourself and why security matters. Newbies are expected to have a general sense of the field. Know terms like cryptography and show you understand the difference between a vulnerability and an exploit. On the other hand, midcareer professionals and people going for more advanced positions, such as CISO or chief security strategist, must demonstrate knowledge gained through certifications such as CISSP, Certified Information Security Manager and Offensive Security Certified Professional (OSCP) -- or show that they are working on those certifications.
So-called soft skills, such as the ability to communicate and creativity, are also important to security interviewers. In addition, companies want people who understand business and, even more importantly, how security relates to their specific business.
Use these 10 interview questions to organize your thoughts and sharpen how you present yourself to security recruiters and interviewers.
10 cybersecurity interview questions and how to answer them
Q1) Why do you want a career in cybersecurity?
Don't start off by telling an interviewer that you heard the field pays well and you want to work in a growth field. While that's one of the reasons many of us pick security, there are better ways to phrase it. Show the interviewer that you've done some homework and that you know about the cybersecurity skills shortage and the workforce gap. If you are just starting out, say you're interested in an entry-level job, but show you have done some homework. Explain that you have been doing some research on which certifications to obtain but haven't decided yet. Tell the interviewer you are aware of the CompTIA Security+ exam and possibly other certifications, like Certified Ethical Hacker (CEH) or CISSP.
Q2) What aspect of cybersecurity interests you?
Your answer will tell the interviewer if you are serious. While it's fine for newbies to say they are still exploring their options, more experienced people need to specify if they're more interested in a hands-on penetration tester path, want to work on a red team or want to work on an incident response team. Job candidates that ultimately want to become CISOs must show the interviewer how they've developed business skills along the way. People with accounting backgrounds can gravitate to compliance or risk jobs on security teams, especially in the financial sector, but if you can, talk about the field in a more in-depth, knowledgeable way that will show the interviewer you are a cut above.
Q3) Why are security teams essential for businesses today?
Here's where you can show the interviewer that you understand the history of security in the enterprise. Explain that the perimeter-based "protecting the moat" style of security has become a thing of the past, replaced by mobile security and securing work-from-home employees. It would help to show that you are aware of some of the major hacks, like the ILOVEYOU and Melissa viruses from 20 years ago. You should also know about the waves of data breaches in the past decade that started with the major hacks at Target, Home Depot and JPMorgan -- and you need to show the interviewer that you understand the business implications of these security incidents.
Candidates going for a management position in security must demonstrate that they are technology people who understand business. Make the case that security professionals cannot get bogged down talking about log analysis data, KPIs and software testing if they hope to convince management about the importance of security infrastructure and policies. Instead, argue that security people need to explain to top management how major breaches will affect sales, profits and future growth by damaging the company's reputation.
Q4) What qualities do you possess that will make you an effective cybersecurity pro?
Don't tell them that you live to hack and have been hacking into computers since you were seven years old. While this may be an awesome skill to have in your next job, odds are the person interviewing you has been a hacker much longer and has worked on tougher challenges. Radnori's Wolpoff said his company looks for people who notice weird things and try to figure them out: "We once had an off-site meeting at a hotel, and the touchscreen that helped a user find out about the area had a strange glitch," Wolpoff said. "One of the interns was rabidly prodding at the broken screen trying to understand the weird behavior, and he was later recruited to my team."
Don't overstate your case and love for the field. Do demonstrate that you have a burning curiosity about how networks and devices work, and tell the interviewer how you've solved technical problems, both in your personal life and on the job. You can also talk about your hobbies and show that you are more than just a tech person. Companies like people who have played musical instruments, acted in plays, dabbled in painting, traveled extensively, and can genuinely show that they have other creative interests. Don't come off as the stereotype who spends all their off-hours playing video games -- though, in reality, video games are an important part of hacker culture, so that's a valuable skill, too.
Q5) What did you accomplish on your last job?
Let them know that you are a hard worker and take initiative. Maybe on your last job you were a network security analyst and worked on a team that redid the company's wireless infrastructure and set updated security policies. Show that you are not afraid of new technology -- that you advocate for new technologies, such as passwordless authentication and more effective identity management. Even better is if the CISO or top manager doesn't want to deploy something like passwordless and you can make the case that, by using Google Authenticator or Authy, the company's users would be more secure -- and they'd actually use it and appreciate that the company was making them more secure. Show you have some moxie and will stand up for a policy or technology you believe in -- that you don't just accept the status quo.
Q6) What does your home network look like?
Security people need to know that you follow cybersecurity best practices -- in other words, that you have changed the default password on your home router, that you have segmented the home network at least into a segment for gaming and home use and a segment for business use and that, for all your main applications, you enable two-factor authentication and also use a password manager. Newbies need to show that they understand these basic issues and have had them on their radar for at least a few years. If you are new to the field, don't take a security interview until you have read up on basic home network security and have a good story to tell about your home network.
Q7) What was the biggest security issue for security teams while managing work-from-home staff in 2020?
The pandemic changed the tech and security game for businesses. Almost overnight, companies that had 10% to 20% of their staff working remotely had almost the entire team working from home. Security pros needed to triage staff and determine who needs a VPN and secure access to corporate data or who could do the basic job via remote desktop protocol (RDP). Show the interviewer that you understand that many companies couldn't handle all the VPN requests and were besieged with attacks on RDP servers. Explain that you have learned from this experience and can help manage the company's transition back to a normal work routine by setting policies to curtail attacks on RDP servers and establishing better network visibility.
Q8) How should a cybersecurity department be structured?
You may not get this specific question, but do find out how the company's security and IT organizations are structured. Does the company plan to have the CISO and CIO sit on the board? If not, are there any plans to head in that direction?
This information will help you determine if the job is right for you. If you are looking for a company that's far along in terms of security maturity, a job at a company just getting security organized might not be a good fit for you. But, if you're looking to become part of a team that's working to improve its security, it could be a fine fit. If you do take a job at a company that's just forming a security group, be realistic and flexible. Companies have been through quite an ordeal in 2020, and if they are reforming or expanding their security teams, you have to be willing to become a part of that effort. If you are not a risk-taker, then you may have to explain that to the interviewer and tell them that the position does not suit your needs or personality.
Q9) How does continuous learning figure into your security career plans?
It's important to show that you have thought about what a career in cybersecurity looks like. If you started off in tech support but want to be a penetration tester, tell the interviewer that you have been working on this path for a while now and understand that you need to continuously develop new skills and earn certifications. Tell them you have done the research and plan to become a CEH and, one day, pass the OSCP exam. People who take a job as a junior security operations center analyst and don't plan to keep learning will get bored and leave the field. Show the interviewer you are someone who's planning a long career in security, and have a story to tell. Your story could be modest. Maybe you've worked retail at a Best Buy while putting yourself through college and learned how important security is to the success of the business. The idea is to show the interviewer that your interest in technology and security is genuine and you have given some thought to the types of skills you'll need to develop.
Q10) Can you explain the following security basics to show you have a good grounding in the field?
Our experts' advice about not memorizing terms notwithstanding, there are indeed some basic terms every candidate for a security position should know.
For starters, make sure you know the difference between a vulnerability and an exploit. Vulnerabilities are weaknesses or gaps in an organization's defenses that could be exploited. Vulnerabilities are known to exist in everything from websites and servers to OSes and software. Exploits are when the bad threat actors take advantage of vulnerabilities to gain unauthorized access to a corporate network. Let the interviewer know you know how the industry tracks and reports vulnerabilities. For example, cve.mitre.org tracks and posts information on all reported vulnerabilities.
New candidates especially should know that people refer to crypto as encryption. It's important to have a basic understanding of how encrypted data thwarts attackers and how email encryption works across a network. Candidates should also have a basic knowledge of SSL technology and HTTPS. SSL creates an encrypted link between a server and a client, typically a web server and web browser. HTTPS secures communications over a network. Anyone coming in for a security interview should know that the little lock to the left of the browser address bar stands for HTTPS.
Also, come prepared with a basic understanding that 2020 was the year of ransomware. Demonstrate that you are aware of the earlier WannaCry and NotPetya attacks and have followed the past year where Maze, Sodinokibi, NetWalker and Egregor did a great deal of damage. Candidates are expected to know how ransomware works, that the attackers encrypt files and, most recently, threaten to slowly leak them out to the public if the victims don't pay the ransom. Know that that the FBI still advises not to pay the ransom but that this has become a controversial issue. It would help if you could explain your position on ransomware. In what circumstances should organizations pay the ransom? Is there ever a time to pay the ransom?
Other common cyber attacks to know about include cross-site scripting (XSS) attacks, which are essentially client-side code injection attacks. In XSS, the attacker executes malicious scripts in a web browser of the victim by including malicious code in a legitimate webpage or web application. Come prepared to talk about these attacks and what you would do about them.
Finally, candidates need to show they understand the many COVID-based attacks that have gone on this year. This would include phishing attacks where the fraudsters lure people on to fake government sites. The victims think they are filling out additional information to obtain unemployment benefits, but in reality, these operations are looking to steal credentials. Be able to explain credential stuffing and information from the annual Verizon Data Breach Investigations Report on how 80 of the breaches use stolen and/or weak passwords.
Finally, the year ended with the SolarWinds hack that impacted major government and corporate systems. Show you are aware of the case and can explain the basics of supply chain attacks.








