
unified communications (UC)
What is unified communications?
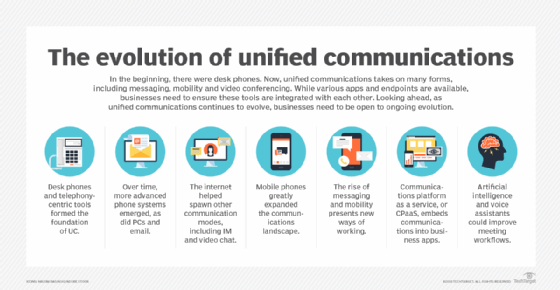
Unified communications (UC) is an umbrella term for the integration of multiple enterprise communication tools -- such as voice calling, video conferencing, instant messaging (IM), presence, content sharing, etc. -- into a single, streamlined interface, with the goal of improving user experience (UX) and productivity. Unified communications technology supports a user's ability to switch seamlessly from one mode of communication to another within a single session, whether on a desktop computer, laptop, tablet or smartphone. For example, someone might initiate a conversation via chat before escalating the interaction to a video conference with a single click, without having to open a separate, video-only application. Many UC systems also integrate with third-party business applications, such as project management software, to enable the centralization of information and resources, as well as more efficient workflows.
UC technology facilitates the integration of software that supports both real-time communications (RTC), such as voice over IP (VoIP), and asynchronous communication, such as persistent chat, so the end user has easy, immediate access to all relevant tools in a consistent environment, from any physical location and digital device. Many UC offerings also include -- or even hinge on -- team collaboration tools, which have messaging-centric workflows and cooperative features such as real-time file sharing and annotating. These next-level UC systems are also referred to as unified communications and collaboration (UCC).
The increasing popularity of unified communications is part of a larger digital transformation and cloud migration under way across today's enterprises. The COVID-19 pandemic greatly accelerated this shift, with many organizations relying heavily on UCC technologies to enable remote work.
How does unified communications work?
A unified communications environment is typically supported by one or more back-end management systems, sometimes referred to as UC platforms, that facilitate integration among services, as well as the front-end clients that provide access. For example, a web conferencing system would make use of an audio conferencing system -- which, in turn, would be built on an underlying Internet Protocol telephony platform -- and a Unified messaging client would allow click-to-talk, click-to-chat or click-to-video functionality.
This article is part of
Ultimate guide on enterprise unified communications strategy
UC systems and their components can be deployed on premises, in a public or private cloud, or as a combination of all three. Cloud-based UC services, also called UC as a service (UCaaS), are gaining traction. An Open Source project called WebRTC enables RTC to be embedded into web browsers. This provides users the option of accessing services via Google Chrome, for example, rather than a downloadable, standalone app.
Historically, single-vendor UC environments have demonstrated the tightest integration and compatibility. Interoperability among vendors remains an ongoing challenge in UC, but it has also been mitigated, in part, by partnerships, common protocols and open application programming interfaces (APIs).
What are the benefits of unified communications?
UC is often credited with increasing employee productivity, supporting more communication and collaboration than the legacy phone system.
Additionally, specific technologies, such as video conferencing, are linked to reduced travel costs, greater efficiency, more flexibility and better engagement. With UC technologies, employees can work from the office, their homes or the road using a variety of devices, from desktop and laptop computers to mobile devices.
The benefits of unified communications can also stretch to an organization's customer base. Organizations that integrate UCaaS solutions with social media, customer-facing apps or call center platforms can directly engage with their customers -- or students or patients in the education and healthcare sectors, respectively -- providing real-time feedback and improved service to boost customer satisfaction.
What are the components of unified communications?
The suite of tools that a UC platform might offer includes the following:
- email;
- text messaging;
- persistent chat;
- mobility;
- real-time presence;
- telephony (fixed line, mobile and VoIP);
- voicemail;
- screen sharing;
- audio transcription;
- audio conferencing;
- video conferencing, room-based video conferencing and TelePresence;
- web conferencing, virtual meeting spaces and interactive whiteboards;
- calendars, scheduling and other personal assistant functions; and
- Enterprise social networking and collaboration platforms.
On the back end, a strong communication system may include the following:
- a single- or multivendor UC platform or server;
- a traditional, IP or cloud-based private branch exchange;
- devices such as phones, headsets, cameras and microphones, which are also user-facing tools;
- business communication gateways, such as session border controllers; and
- a multipoint control unit, or video bridge, for video conferencing with three or more endpoints.
Differences between communications and collaboration
UC and team collaboration tools overlap significantly, and vendors, IT pros and end users increasingly use the terms interchangeably. Technically, differences between business communications and collaboration exist, however, depending on how workers interact, and for what purpose, while using a given tool or feature. Email, for example, enables communication between two or more parties. And, while those parties might send and receive messages in the spirit of cooperation, their communication isn't necessarily collaborative.
Collaboration, on the other hand, involves interactively working together toward a concrete shared outcome. Imagine that a group of sales professionals needs to plan a client presentation. If they convene on a video conferencing platform to discuss the upcoming meeting, they are communicating. But, if they also have a single shared document in the cloud -- perhaps, a presentation outline, PowerPoint file or virtual whiteboard -- where each user can make changes the whole group can see, then they are also collaborating. While communication can exist without collaboration, collaboration is impossible without communication.
Why might the difference between business communications and collaboration matter? Vendors increasingly package an array of connectivity and productivity applications in their UC offerings, sometimes inaccurately describing communication features as collaborative. Customers should understand the difference between communication and collaboration, if only to have confidence they will get the value they need from any given platform or tool.
What are technologies related to UC?
UC overlaps with contact center technologies in the form of automated call distribution, interactive voice response and automated attendant systems, video chat functionality, and messaging capabilities. Integrating internal and external UC capabilities -- with in-house and customer-facing communications happening on the same platform and over the same channels -- can eliminate departmental silos and improve customer outcomes.
Other types of UC offerings embed enterprise communication tools into business processes. This concept, known as communications-enabled business processes, has evolved into communications platform as a service (CPaaS) and the use of communications APIs. Services such as presence, chat and telephony can be integrated into business applications that span the entire organization. For example, users can launch a voice call directly within a customer relationship management application.
UC risks and security issues
The biggest security challenges a business faces when implementing and maintaining its UC infrastructure are managing users' identities and access and securing data. UC strategies focus on connecting disparate technologies operating on an array of different networks, so the challenge becomes ensuring each disparate access point is secure, no matter the device or the network on which it is operating.
Additionally, UCaaS and bring your own device (BYOD) environments are becoming increasingly prevalent in enterprises. Both approaches spread out an organization's data and increase the attack surface. UCaaS also places a portion of the security responsibilities in the hands of a third-party vendor and requires an organization to thoroughly vet the security practices of the service provider.
Another potential UC security vulnerability is the exploitation of open APIs. Traditionally, open communication APIs are used to streamline workflows by enabling an organization to add customizable communication features to existing applications, removing the need for employees to switch between applications for communication. However, the open nature of the API leaves room for access credentials to be stolen. If credentials fall into the wrong hands, potentially sensitive data could be leaked.
Other significant security issues enterprise UC faces as a result of compromised access procedures and poor encryption include the following:
- content theft, in which a malicious actor intercepts enterprise traffic;
- denial-of-service attacks, in which an attacker targets specific IP ports related to UC services and overloads them with traffic to damage service; and
- service hijacking, in which an attacker sells access to a company's UC applications, such as VoIP, and, consequently, causes UC costs to increase dramatically.
Organizations can take a few steps to ensure they are practicing good access management, including the following:
- Granular access. Define user roles and levels of authorization based on those roles to limit access to sensitive data.
- Audit trail. Keep track of which users are accessing an API and how they are doing it. Doing this will help organizations monitor suspicious activity.
- Encryption. Organizations using a CPaaS provider should inquire about their service provider's level of encryption.
- Security awareness. Employees should understand the importance of data security and practice good security habits, such as creating strong passwords and using trusted networks when accessing enterprise UC applications.
Unified communications platforms
When choosing a unified communications platform, an organization should ensure its preferred vendor offers a product that meets the organization's unique needs and has strong security practices in place. Some popular UC platform vendors are the following:
- 8x8 Inc. offers a contact center integrated with Google Cloud's Contact Center AI, which adds real-time customer experience analytics and a virtual agent capability that can answer routine customer calls. Virtual agents can improve customer service by reducing call times.
- Avaya offers the Avaya OneCloud UC platform. Avaya is one of the few UC vendors that still offers adequate on-premises solutions in a field that is moving swiftly to the cloud.
- Cisco has a variety of UC products and services for on-premises deployment and the cloud, including Webex Calling, Jabber, Unity Connection for voice messaging and Single Number Reach for extensive telephony features.
- CounterPath recently introduced its new team collaboration platform, Bria Teams. The cloud-based service is best suited to small and midsize businesses. One feature of the platform is a dedicated high-definition virtual meeting room, which eliminates the need for team members to schedule a physical meeting. Bria Teams and Bria Teams Pro also include chatrooms that track conversation history across multiple devices.
- Fuze offers voice, video, team chat and collaboration tools as part of its flagship UCaaS platform. Additional UCC features include file-sharing and contact center capabilities. The company guarantees 99.99% uptime.
- Microsoft offers Microsoft Teams for Microsoft 365, which integrates chats, meetings, calls, files and collaboration tools in one place. Users can customize their Teams platform with add-ins (applications) from either a third party or Microsoft. Users can also build their own application for Teams under the Microsoft 365 Developer Program.
- Mitel offers a range of telephony and UC options, including MiCloud, MiCollab and MiVoice, that cover businesses of all sizes. Mitel is another one of the few vendors still investing in on-premises UC solutions.
- RingCentral was an early major UCaaS player and, now, has one of the largest subscriber bases in the world, according to analysts. The cloud-based RingCentral Office platform has VoIP, messaging and meeting capabilities and is available in more than 40 countries.
- Unify provides VoIP calling, video conferencing, team messaging and file sharing on its Unify Circuit platform.
Criteria an organization should consider during the decision-making process include the following:
- Range of services. Different vendors offer different levels of service. Some vendors offer only a small range of foundational UC applications, like telephony, IM and basic conferencing, while others offer comprehensive, full-scale services, such as call recording, video, screen sharing and file sharing. Many vendors offer a large range of services and enable customers to start with the basics as needed.
- Specialization. Different vendors are specialized in different areas of unified communications. For example, one vendor might focus on telephony-based communications, whereas another might focus mainly on mobility and collaboration. An organization should consider its use cases for a unified communications solution and choose a vendor that best applies.
- Deployment model. Organizations can choose between implementing on-premises UC platforms, cloud-based platforms or a hybrid solution that mixes both models. Organizations with an apt IT department may consider operating on-premises solutions, whereas smaller businesses may opt for a hybrid or hosted option in which aspects of the platform are managed by a third-party provider. Many vendors are making the transition to cloud-based services.
- Interoperability. If an organization is utilizing multiple vendors at once or a hybrid infrastructure, it should ensure all provided platforms can function together efficiently.
- UX. As organizations continue to adopt BYOD and mobility initiatives and the rate of device turnover increases, it becomes increasingly important to have intuitive, adaptable and unified UX to streamline the use of UC platforms on those devices. Poor UX will render an organization's UC architecture useless, no matter how well integrated its back-end services are.
What is the future of unified communications?
The UC market is going through a period of significant transformation, particularly when it comes to UC's migration to the cloud and the growing dominance of UCaaS over purely on-premises deployments. The COVID-19 pandemic dramatically hastened this shift by forcing an unprecedented percentage of the workforce to work remotely. According to a Metrigy survey, the percentage of organizations using UCaaS increased by 79% between 2019 and 2020, with more than 60% of organizations speeding up their adoption plans.
Going forward, as employees return to the office, it's clear they must have the ability to communicate from anywhere on a moment's notice. Many experts also expect enterprises to permanently embrace a hybrid work model, with a mix of in-office and remote employees. These factors make cloud-based UC technology attractive and, in many cases, necessary.
Before the COVID-19 pandemic hit, vendors were already shifting their focus from on-premises products and support to investment in cloud-based products and will likely continue to do so in the months and years ahead. Organizations that plan to stick to on-premises solutions for the foreseeable future should be aware that only a select few vendors are still making a point of investing in on-premises UC and there may not be adequate support for this type of infrastructure in the near future. On the other hand, some experts argue that escalating cyberattacks on cloud services make a compelling case for on-premises UC systems, which offer organizations greater control over their own security.
In addition to ongoing cloud migration, users can expect vendors to continue to partner up and collaborate in creating stacks of UC tools, which can help companies capitalize on each other's strengths and improve compatibility between their respective products.
Lastly, emerging technologies, such as artificial intelligence (AI) and machine learning, are anticipated to have an impact on the field -- although, its less clear exactly how. In addition, only 5% of companies surveyed by Metrigy used AI in their UC and collaboration experiences; 43% of companies were considering it. Some uses for AI in UC could be to break down language barriers and to improve UX.







