iQoncept - Fotolia
Why DevOps security must be on infosecs' priority list
In the rush to implement DevOps, security is too often overlooked. But DevSecOps is essential in these hack-filled days. Learn how to add security to software development.
In the rush to implement DevOps, security is often the forgotten component.
Organizations that deploy DevOps tools and methodologies can deliver code faster and more effectively align it with business objectives. A recent Nemertes Research study found that 75% of companies that were successful in implementing their digital transformation initiatives were deploying DevOps. (The study included several objective measures of "success," including budgeting, staffing and the measured business effectiveness of digital transformation.) In a nutshell, DevOps is a critical tool for organizations seeking to digitally transform.
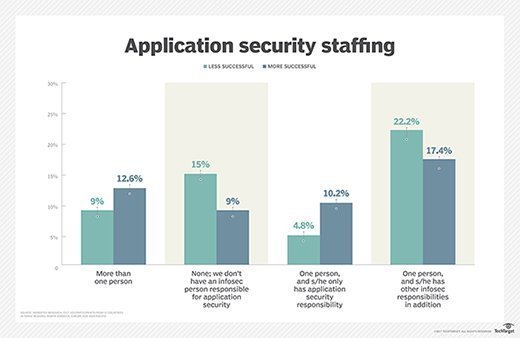
But quite often, organizations that have an effective application development team and a robust information security organization don't invest in the area in which the two overlap: application security.
Having an application security team that's on board with both security and DevOps strategies is the first step toward enabling DevOps security -- that is, code development that's as secure as it is agile. Building an application security team means hiring and training developers who understand security and security experts who can code.
This application security team needs to be funded out of the infosec budget; funding out of the infosec -- versus applications -- budget correlated with greater security success, as measured by quantitative metrics and security operational performance.
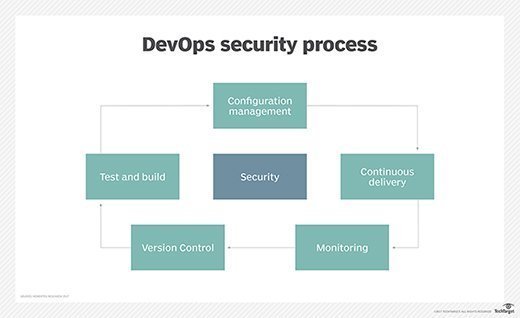
And the application security team should be familiar with DevOps tool suites. Automated tools designed to accelerate code development and streamline support can also make code more secure if it's deployed properly. The application security folks also need to be fluent in DevOps processes -- including the concepts of sprints, scrums and epics.
DevOps security needs coding know-how
Finally, all DevSecOps developers need a working understanding of some of the top coding errors that can introduce DevOps security vulnerabilities. Those errors include the following:
- Consuming unauthenticated resources -- that is, writing code that accesses services and microservices that haven't been authenticated and may contain malware. The best fix for this is to deploy an authentication mechanism -- such as JavaScript Object Notation Web Signature, or RFC7797 -- to require all services and microservices to use the mechanism, and to automate compliance.
- Letting malware into memory -- i.e., writing code that deposits data in predictable locations in memory that can be accessed by malware, such as buffer overflow malware exploits. The best prevention here is to develop in languages and frameworks that prohibit random memory assignments and to deploy automated security testing.
- Using pseudo-random number generators -- e.g., Monte Carlo simulations -- instead of true random number generators (TRNGs). This results in inadvertently injecting predictability into encryption mechanisms and other apps that require true randomness to be effective. The solution here, of course, is to deploy TRNGs for all security applications that require random number generation.
- Making undocumented code changes, which can inject vulnerabilities. Fortunately, DevOps tool suites include code management tools that feature auditing and logging, automatically ensuring that every change is documented. Requiring separation of duties in making changes -- no developers can approve their own changes -- can also ensure all changes are properly reviewed.
- Ignoring infrastructure security. Just because code is secure doesn't mean the infrastructure on which it runs is. Containerization -- i.e., using tools like Docker, Rocket, Amazon and the like -- can increase both code reliability and security; application security teams should be sure the infosec group is deploying Defense in depth to protect both infrastructure and apps.
The bottom line? Moving from DevOps to DevSecOps isn't as hard as it may sound. The first step toward DevOps security is putting in place an application security team that understands both coding and security and bringing that team up to speed on DevOps methodologies. That process should help protect the DevOps initiative from making some of the most common coding errors that can reduce security -- empowering it to move full speed ahead and enabling digital transformation.








