CHAP (Challenge-Handshake Authentication Protocol)
What is CHAP (Challenge-Handshake Authentication Protocol)?
CHAP (Challenge-Handshake Authentication Protocol) is a challenge and response authentication method that Point-to-Point Protocol (PPP) servers use to verify the identity of a remote user. CHAP authentication begins after the remote user initiates a PPP link.
CHAP enables remote users to identify themselves to an authenticating system, without exposing their password. With CHAP, authenticating systems use a shared secret -- the password -- to create a cryptographic hash using the MD5 message digest algorithm.
CHAP uses a three-way handshake to verify and authenticate the identity of the user, whereas the Password Authentication Protocol (PAP) uses a two-way handshake for authentication between the remote user and PPP server.
Designed to be used with PPP for authenticating remote users, CHAP is applied periodically during a remote session to reauthenticate the user. PAP and CHAP are primarily intended for remote connections over dial-up lines or switched circuits, as well as for dedicated links.
PAP and CHAP are commonly used for negotiating a network connection to an internet service provider. CHAP is specified in Request for Comments 1994.
How does CHAP work?
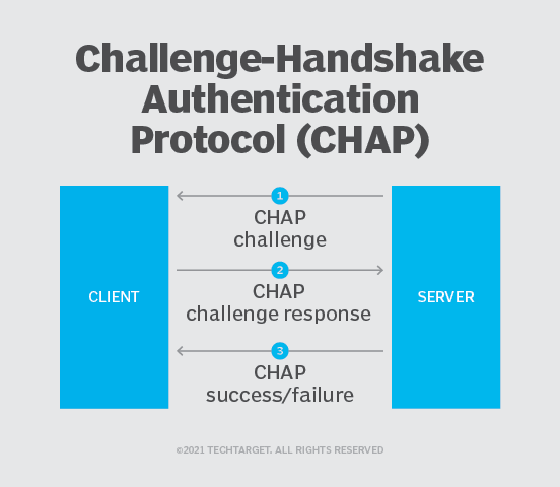
Here's how CHAP works:
- After the link is made, the server sends a challenge message to the connection requestor.
- The requestor responds with a value obtained by using a one-way hash function known as MD5.
- The server checks the response by comparing it with its own calculation of the expected hash value. If the values match, the authentication is acknowledged; otherwise, the connection is usually terminated.
The server can send a new challenge to the requestor randomly during the session to reauthenticate the requestor. Steps 1 through 3 are then repeated.
At any time, the server can request the connected party to send a new challenge message. Because CHAP identifiers are changed frequently and authentication can be requested by the server at any time, CHAP provides more security than PAP.
Types of CHAP packets
PPP carries CHAP packets between the authenticator and the requestor. CHAP packets consist of a header, which includes the following:
- Code field, which contains an eight-bit code identifying the type of CHAP packet being sent -- valid values are 1 to 4;
- Identifier field, which is an arbitrary eight-bit ID identifying the packet as belonging to an authentication sequence;
- Length field, which contains the number of bytes in the CHAP packet; and
- Data field, which includes any data being requested or submitted and values depending on the type of CHAP packet it is being carried in.
Further reading
CHAP and PAP were among the first attempts to implement secure remote access, and understanding the differences between CHAP and PAP is just the first step.
CHAP integrates with the Remote Authentication Dial-In User Service, or RADIUS, protocol. Kerberos offers a more sophisticated and secure tool for remote user authentication.
Learning the differences between CHAP and Extensible Authentication Protocol, Lightweight Extensible Authentication Protocol and Wi-Fi Protected Access version 2 protocol will help IT pros make the best decision.
CHAP works with four different types of packet. Each packet is identified by the value of its Code field, as follows:
- The authenticating system -- usually a network access server or switch -- sends a CHAP Challenge packet to start the authentication process. After a PPP session is initiated, the system or network being accessed can demand that the remote user authenticate. The Challenge includes the authenticator's host name.
- The remote user's system must send a CHAP Response packet in response to a Challenge. The remote system sends a secure hash based on the remote user's password in the Response packet. The authenticator compares the hash of the user's password with the expected value. The remote user is authenticated if they match; otherwise, the authentication fails.
- The authenticating system -- the network access server-- sends a CHAP Success packet if the remote user's hash matches the hash expected by the server.
- The authenticating system sends a CHAP Failure packet if the remote user's password hash does not match the value sent by the user.
If the remote system fails to respond to a Challenge packet, the authenticator can repeat the process. The authenticator terminates the remote user's access if they can't authenticate.
CHAP vs. PAP
CHAP is a more secure procedure for connecting to a system than PAP.
The PAP and CHAP authentication schemes were both originally specified for authenticating remote users connecting to networks or systems using PPP. CHAP's three-way handshake protocol provides stronger protection against password guessing and eavesdropping attacks than PAP's two-way handshake.
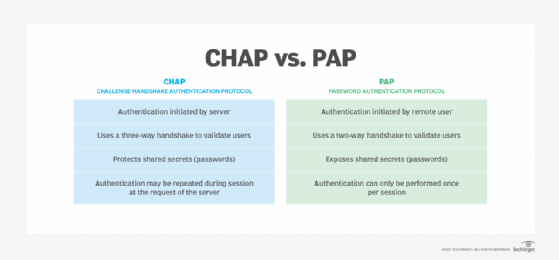
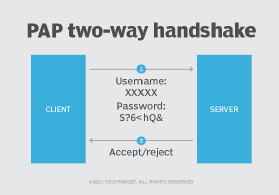
Authenticating with PAP requires the remote user to submit their username and password, and the authenticating system then either permits or denies the user access based on those credentials.
CHAP secures the authentication process by using a more sophisticated protocol. CHAP implements a three-way handshake protocol to be used after the host establishes a PPP connection with the remote resource.
PAP defines a two-way handshake for a remote user to initiate remote access:
- The remote system sends a username and password, repeating the transmission until the network access server responds.
- The network access server transmits an authentication acknowledgement if the credentials are authenticated. If the credentials are not authenticated, the network access server sends a negative acknowledgment.
While PAP may be used as a bare minimum protocol to enable a remote user to initiate a network connection, CHAP provides a more secure authentication protocol.







