
two-factor authentication (2FA)
What is two-factor authentication and why is it used?
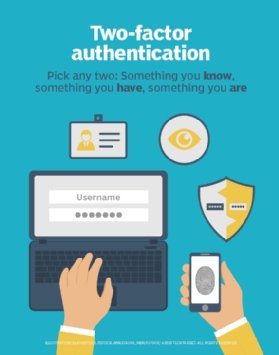
Two-factor authentication (2FA), sometimes referred to as two-step verification or dual-factor authentication, is a security process in which users provide two different authentication factors to verify themselves.
2FA is implemented to better protect both a user's credentials and the resources the user can access. Two-factor authentication provides a higher level of security than authentication methods that depend on single-factor authentication (SFA), in which the user provides only one factor -- typically, a password or passcode. Two-factor authentication methods rely on a user providing a password as the first factor and a second, different factor -- usually either a security token or a biometric factor, such as a fingerprint or facial scan.
Two-factor authentication adds an additional layer of security to the authentication process by making it harder for attackers to gain access to a person's devices or online accounts because, even if the victim's password is hacked, a password alone is not enough to pass the authentication check.
Two-factor authentication has long been used to control access to sensitive systems and data. Online service providers are increasingly using 2FA to protect their users' credentials from being used by hackers who stole a password database or used phishing campaigns to obtain user passwords.
What are authentication factors?
There are several ways in which someone can be authenticated using more than one authentication method. Currently, most authentication methods rely on knowledge factors, such as a traditional password, while two-factor authentication methods add either a possession factor or an inherence factor.
Authentication factors, listed in approximate order of adoption for computing, include the following:
- A knowledge factor is something the user knows, such as a password, a personal identification number (PIN) or some other type of shared secret.
- A possession factor is something the user has, such as an ID card, a security token, a cellphone, a mobile device or a smartphone app, to approve authentication requests.
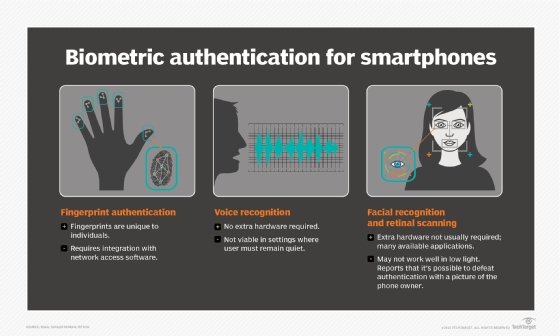
- A biometric factor, also known as an inherence factor, is something inherent in the user's physical self. These may be personal attributes mapped from physical characteristics, such as fingerprints authenticated through a fingerprint reader. Other commonly used inherence factors include facial and voice recognition or behavioral biometrics, such as keystroke dynamics, gait or speech patterns.
- A location factor is usually denoted by the location from which an authentication attempt is being made. This can be enforced by limiting authentication attempts to specific devices in a particular location or by tracking the geographic source of an authentication attempt based on the source Internet Protocol address or some other geolocation information, such as Global Positioning System (GPS) data, derived from the user's mobile phone or other device.
- A time factor restricts user authentication to a specific time window in which logging on is permitted and restricts access to the system outside of that window.
The vast majority of two-factor authentication methods rely on the first three authentication factors, though systems requiring greater security may use them to implement multifactor authentication (MFA), which can rely on two or more independent credentials for more secure authentication.
How does two-factor authentication work?
Enabling two-factor authentication varies depending on the specific application or vendor. However, two-factor authentication processes involve the same general, multistep process:
- The user is prompted to log in by the application or the website.
- The user enters what they know -- usually, username and password. Then, the site's server finds a match and recognizes the user.
- For processes that don't require passwords, the website generates a unique security key for the user. The authentication tool processes the key, and the site's server validates it.
- The site then prompts the user to initiate the second login step. Although this step can take a number of forms, the user has to prove that they have something only they would have, such as biometrics, a security token, an ID card, a smartphone or other mobile device. This is the inherence or possession factor.
- Then, the user may have to enter a one-time code that was generated during step four.
- After providing both factors, the user is authenticated and granted access to the application or website.
Elements of two-factor authentication
Two-factor authentication is a form of MFA. Technically, it is in use any time two authentication factors are required to gain access to a system or service. However, using two factors from the same category doesn't constitute 2FA. For example, requiring a password and a shared secret is still considered SFA as they both belong to the knowledge authentication factor type.
As far as SFA services go, usernames and passwords are not the most secure. One problem with password-based authentication is it requires knowledge and diligence to create and remember strong passwords. Passwords require protection from many insider threats, such as carelessly stored sticky notes with login credentials, old hard drives and social engineering exploits. Passwords are also prey to external threats, such as hackers using brute-force, dictionary or rainbow table attacks.
Given enough time and resources, an attacker can usually breach password-based security systems and steal corporate data. Passwords have remained the most common form of SFA because of their low cost, ease of implementation and familiarity.
Multiple challenge-response questions can provide more security, depending on how they are implemented, and standalone biometric verification methods can also provide a more secure method of SFA.
Types of two-factor authentication products
There are many different devices and services for implementing 2FA -- from tokens to radio frequency identification (RFID) cards to smartphone apps.
Two-factor authentication products can be divided into two categories:
- tokens that are given to users to use when logging in; and
- infrastructure or software that recognizes and authenticates access for users who are using their tokens correctly.
Authentication tokens may be physical devices, such as key fobs or smart cards, or they may exist in software as mobile or desktop apps that generate PIN codes for authentication. These authentication codes, also known as one-time passwords (OTPs), are usually generated by a server and can be recognized as authentic by an authentication device or app. The authentication code is a short sequence linked to a particular device, user or account and can be used only once as part of an authentication process.
Organizations need to deploy a system to accept, process and allow or deny access to users authenticating with their tokens. This may be deployed in the form of server software or a dedicated hardware server, as well as provided as a service by a third-party vendor.
An important aspect of 2FA is ensuring the authenticated user is given access to all resources the user is approved for and only those resources. As a result, one key function of 2FA is linking the authentication system with an organization's authentication data. Microsoft provides some of the infrastructure necessary for organizations to support 2FA in Windows 10 through Windows Hello, which can operate with Microsoft accounts, as well as authenticate users through Microsoft Active Directory, Azure AD or Fast IDentity Online (FIDO).
How 2FA hardware tokens work
Hardware tokens for 2FA are available supporting different approaches to authentication. One popular hardware token is the YubiKey, a small Universal Serial Bus (USB) device that supports OTPs, public key encryption and authentication, and the Universal 2nd Factor protocol developed by the FIDO Alliance. YubiKey tokens are sold by Yubico Inc., based in Palo Alto, Calif.
When users with a YubiKey log in to an online service that supports OTPs -- such as Gmail, GitHub or WordPress -- they insert their YubiKey into the USB port of their device, enter their password, click in the YubiKey field and touch the YubiKey button. The YubiKey generates an OTP and enters it in the field.
The OTP is a 44-character, single-use password; the first 12 characters are a unique ID that represents the security key registered with the account. The remaining 32 characters contain information that is encrypted using a key known only to the device and Yubico's servers, established during the initial account registration.
The OTP is sent from the online service to Yubico for authentication checking. Once the OTP is validated, the Yubico authentication server sends back a message confirming this is the right token for this user. 2FA is complete. The user has provided two factors of authentication: The password is the knowledge factor, and the YubiKey is the possession factor.
Two-factor authentication for mobile devices
Smartphones offer a variety of 2FA capabilities, enabling companies to use what works best for them. Some devices can recognize fingerprints, use the built-in camera for facial recognition or iris scanning, and use the microphone for voice recognition. Smartphones equipped with GPS can verify location as an additional factor. Voice or Short Message Service (SMS) may also be used as a channel for out-of-band authentication.
A trusted phone number can be used to receive verification codes by text message or automated phone call. A user has to verify at least one trusted phone number to enroll in mobile 2FA.
Apple iOS, Google Android and Windows 10 all have apps that support 2FA, enabling the phone itself to serve as the physical device to satisfy the possession factor. Duo Security, based in Ann Arbor, Mich., and purchased by Cisco in 2018 for $2.35 billion, has a platform that enables customers to use their trusted devices for 2FA. Duo's platform first establishes that a user is trusted before verifying the mobile device can also be trusted as an authentication factor.
Authenticator apps replace the need to obtain a verification code via text, voice call or email. For example, to access a website or web-based service that supports Google Authenticator, users type in their username and password -- a knowledge factor. Users are then prompted to enter a six-digit number. Instead of having to wait a few seconds to receive a text message, an authenticator generates the number for them. These numbers change every 30 seconds and are different for every login. By entering the correct number, users complete the verification process and prove possession of the correct device -- an ownership factor.
These and other 2FA products offer information on the minimum system requirements necessary to implement 2FA.
Push notifications for 2FA
A push notification is passwordless authentication that verifies a user by sending a notification directly to a secure app on the user's device, alerting the user that an authentication attempt is happening. The user can view details of the authentication attempt and either approve or deny access -- typically, with a single tap. If the user approves the authentication request, the server receives that request and logs the user in to the web app.
Push notifications authenticate the user by confirming that the device registered with the authentication system -- usually a mobile device -- is in the possession of the user. If an attacker compromises the device, the push notifications are also compromised. Push notifications eliminate threats such as man-in-the-middle attacks, unauthorized access and social engineering attacks.
While push notifications are more secure than other forms of authentication methods, there are still security risks. For example, users could accidentally approve a fraudulent authentication request because they are used to tapping approve when they receive push notifications.
Is two-factor authentication secure?
While two-factor authentication does improve security, 2FA schemes are only as secure as their weakest component. For example, hardware tokens depend on the security of the issuer or manufacturer. One of the most high-profile cases of a compromised two-factor system occurred in 2011 when security company RSA security reported its SecurID authentication tokens had been hacked.
The account recovery process itself can also be subverted when it is used to defeat two-factor authentication because it often resets a user's current password and emails a temporary password to allow the user to log in again, bypassing the 2FA process. The business Gmail accounts of the chief executive of Cloudflare were hacked in this way.
Although SMS-based 2FA is inexpensive, easy to implement and considered user-friendly, it is vulnerable to numerous attacks. The National Institute of Standards and Technology (NIST) has discouraged the use of SMS in 2FA services in its Special Publication 800-63-3: Digital Identity Guidelines. NIST concluded that OTPs sent via SMS are too vulnerable due to mobile phone number portability attacks, attacks against the mobile phone network and malware that can be used to intercept or redirect text messages.
Future of authentication
Environments that require higher security may be interested in three-factor authentication, which typically involves possession of a physical token and a password used in conjunction with biometric data, such as fingerprint scans or voiceprints. Factors such as geolocation, type of device and time of day are also being used to help determine whether a user should be authenticated or blocked. Additionally, behavioral biometric identifiers, such as a user's keystroke length, typing speed and mouse movements, can also be discreetly monitored in real time to provide continuous authentication instead of a single one-off authentication check during login.
Relying on passwords as the main method of authentication, while common, often no longer offers the security or user experience that companies and their users demand. And, even though legacy security tools, such as a password manager and MFA, attempt to deal with the problems of usernames and passwords, they depend on an essentially outdated architecture: the password database.
Consequently, many organizations are turning to passwordless authentication. Using methods such as biometrics and secure protocols enables users to securely authenticate themselves in their applications without having to enter passwords. In business, this means employees can access their work without having to enter passwords and IT still maintains total control across every login. The use of blockchain, for example, through decentralized identity or self-sovereign identity, is also gaining attention as an alternative to traditional authentication methods.





