macro virus
What is a macro virus?
A macro virus is a computer virus written in the same macro language used to create software programs such as Microsoft Excel or Word. It centers on software applications and does not depend on the operating system (OS). As a result, it can infect any computer running any kind of OS, including Windows, macOS and Linux.
Macro viruses work by adding their code to the macros associated with documents, spreadsheets and other data files. They target software rather than systems and can infect any OS. Macro viruses have been around since 1995 when the Concept virus first appeared. It was accidentally included on a CD-ROM (compact disc read-only memory) called Microsoft Compatibility Test and shipped by Microsoft to hundreds of corporations.
With the release of Microsoft Office 2000 and all subsequent versions, Microsoft disabled macros by default. Since then, it's become more difficult for bad actors to easily launch macro viruses. However, as long as macros are available to users, the risk of macro viruses remains serious.
In fact, if a macro virus infects a file, it can potentially damage not only the document itself, but the system and other applications. So, security teams should not ignore the risk.
How does a macro virus work and spread?
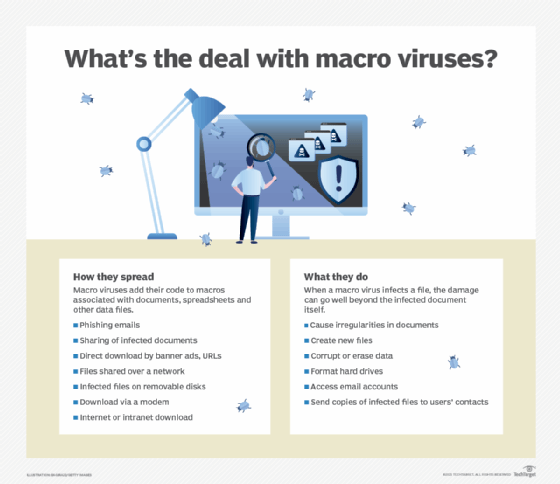
Typically, macro malware is transmitted through phishing emails containing malicious attachments. The macro virus spreads quickly as users share infected documents, often by forwarding the infected email. Its code may also be downloaded to users' computers after they click on malicious links in banner ads or URLs (Uniform Resource Locators).
Other ways macro viruses may spread
- when files are shared over a network
- when infected files are placed on a removable disk and shared among multiple users
- when an infected file is downloaded via a modem and opened
- when an infected file is downloaded via the internet or intranet and opened
So, any program that uses macros can act as the virus host, and any copy of an infected program, regardless of where it resides -- email, hard disk, USB (Universal Serial Bus) drive, etc. -- or which OS supports it, can contain and spread the virus.
Since the virus is dormant until the infected macro is run, it's difficult to detect. In this sense, it is like a Trojan horse, a malicious program. But, unlike a Trojan, a macro virus can replicate automatically and infect other computers quickly.
What can macro viruses do?
When a macro virus infects an application, it executes a series of commands and a sequence of actions that begin automatically when the application is opened. An infected macro that is executed typically infects every document on a user's computer.
The virus can also do the following:
- cause irregularities in text documents, such as inserting or deleting words or pictures;
- create new files;
- corrupt or erase stored data;
- Format hard drives;
- access email accounts; and
- send out copies of infected files to everyone on the user's contact list.
How have macro viruses evolved?
Initially, macro viruses mostly infected Word or Excel documents -- two applications with powerful macro languages and features. And they almost exclusively targeted the Windows OS.
Since then, macro viruses evolved into a dominant type of virus, affecting all kinds of applications, files and OSes that use macros. Additionally, because a macro virus is cross-platform, it can infect both Windows and Mac computers using the same code.
For example, in 2017, MacDownloader, the first Word macro virus for Apple's macOS, was discovered. MacDownloader enabled hackers to use malicious macros in Word documents to install malware on Mac computers to steal users' data, such as browser history logs, webcam files, passwords and encryption keys.
What are examples of macro viruses?
The Concept macro virus spread via infected Word documents with a .doc extension attached to email messages. It didn't inflict damage in the affected computers, but simply displayed an onscreen message when it infected a document.
A more notable macro virus was the Melissa virus. Discovered in 1999, the Melissa virus spread via an email attachment. When users opened an attachment infected with Melissa, it infected their computer and rapidly spread to other email messages using macros in Microsoft Word 97 and 2000, as well as Excel and Outlook. Melissa disrupted more than 1 million email accounts worldwide and cost businesses an estimated $80 million.
The Nuclear macro virus was similar to Concept. Its malicious macros were designated "ExecuteOnly." It displayed a strange message on the last page of a document when it was printed during the last four seconds of any minute. It also caused error messages to appear when a user selected from File > Print or File > Save As.
One of the most well-known macro viruses, first observed in 2014, was Hancitor, also known as Chanitor. This macro-based malware downloader was hidden in Word documents and delivered via phishing emails. Its main purpose was to download malicious payloads, such as banking Trojans and ransomware, on contaminated machines.
There have been Trojans, like Rovnix; malware, like Dridex; and ransomware, like Locky, that have also used malicious macros in Microsoft Word and other applications to hijack systems, log keystrokes, steal data, etc.
A more recent macro virus was called U.S. Allies and Rivals Digest Trump's Victory -- Carnegie Endowment for International Peace.docm. It came via a malicious Word file carrying the MacDownloader macro virus mentioned earlier.
What are signs of a macro virus infection?
A macro virus infection may be difficult to detect. However, it does leave some footprints that could indicate an infection.
For example, the system speed may be affected, or the computer may display strange error messages. The Nuclear macro virus displayed this message: "And finally I would like to say: STOP ALL FRENCH NUCLEAR TESTING IN THE PACIFIC."
Other possible red flags of a macro virus infection include the following:
- if the computer asks the user for a password on a file that doesn't usually require one; and
- if it saves documents as template files.
How are macro viruses removed?
If a system is infected with a macro virus, it's critical to remove it as soon as possible with specific security software tools for macro virus detection and removal. This can stop it from spreading across the network.
The first step in removing macro malware is to reboot the infected computer in safe mode.
Deleting temporary files can speed up virus scanning, free up disk space and remove any malware-infected temp files.
It's also recommended to run a virus scan on the infected computer. If a real-time antivirus program is already running on the machine, an on-demand virus scanner can be used to check for undetected malware. In this scenario, the on-demand scanner is used first, followed by a full scan using real-time antivirus. This should detect and quarantine any macro malware found on the system.
How are macro viruses prevented?
Prevention is always better than cure with macro viruses. By regularly scanning all systems, documents and inbound email attachments, organizations can clean infected assets. This will ensure that no new macro virus is downloaded or, worse, executed across the network.
Other macro virus defense strategies include preventing users from opening dubious files and preventing macros from running by default when documents are opened in Microsoft Word, Excel, Outlook, etc.
More techniques to prevent the spread of macro viruses
- Use a spam filter. The fewer phishing email messages users receive, the less chance their computers will be infected by malware.
- Use a strong antivirus program. Antivirus software warns users when attempting to download suspicious files or open harmful links.
- Upgrade and patch software. Ensure that computers are running current software and OS versions and that all security patches are installed.
- Be wary of attachments. Never open attachments from unknown senders or in suspicious email messages, even if they appear to be from a known source.
Macro viruses are a particularly sneaky type of virus. Nonetheless, the risk is real. By following security best practices, it is possible for organizations to stay ahead of bad actors and prevent macro viruses from wreaking havoc in the enterprise network.