pharming
What is pharming?
Pharming is a scamming practice in which malicious code is installed on a personal computer (PC) or server, misdirecting users to fraudulent websites without their knowledge or consent. The aim is for users to input their personal information. Once information, such as a credit card number, bank account number or password, has been entered at a fraudulent website, criminals have it, and identity theft can be the end result.
How does pharming work?
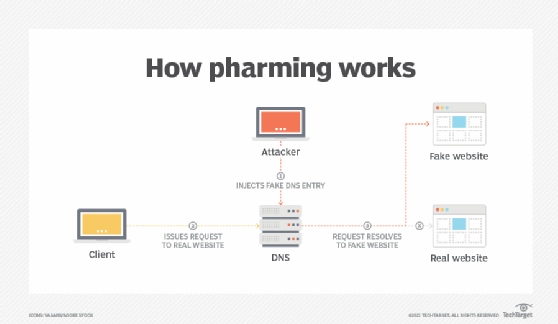
Pharming uses the domain name system (DNS) to redirect users from the intended domain to another website. This can be done by exploiting vulnerabilities in the DNS protocol or by compromising insecure DNS servers and adding entries that redirect traffic.
The DNS server translates domain names, such as google.com, to Internet Protocol (IP) addresses, such as 187.128.30.49. If the IP address of a website in the DNS server is changed by a pharmer, then the computer will have the wrong -- or corrupted -- IP address when accessing that website. By causing the DNS server to give the user the incorrect answer, the pharmer can send users to a fake site for some nefarious purpose.
Pharming techniques
There are a couple different forms of pharming. In one form, code sent in an email modifies local host files on a PC. The host files convert Uniform Resource Locators (URLs) into the IP address that the computer uses to access websites. A computer with a compromised host file will go to the fake site even if a user types in the correct web address or clicks on an affected bookmark entry.
Some spyware removal programs can correct the corruption, but it frequently recurs unless the user changes browsing habits, such as blocking pop-up ads and cookies. For this reason, it is recommended that the user find a reliable software program, such as Norton Internet Security, and install it to both clean the system and protect it.
Another pharming tactic is known as DNS poisoning, in which the DNS table in a server is modified so someone who thinks they are accessing legitimate websites is actually directed toward fraudulent ones. In this method of pharming, individual PC host files don't need to be corrupted. Instead, the problem occurs in the DNS server, which handles millions of internet users' requests for URLs. Victims then end up at a bogus site without any visible indicator of a discrepancy.
Spyware removal programs cannot deal with this type of pharming because nothing is technically wrong with the end users' computers.
What is the difference between pharming and phishing?
Pharming has been called "phishing without a lure." In phishing, the perpetrator sends out legitimate-looking emails -- appearing to come from some of the web's most popular sites -- in an effort to obtain personal and financial information from individual recipients. But, in pharming, larger numbers of computer users can be victimized because it is not necessary to target individuals one by one, and no conscious action is required on the part of the victim.
Phishing is an attempt to extract sensitive information, such as usernames, passwords and credit card details, by masquerading as a trustworthy entity in an electronic communication. Phishing is typically carried out by email spoofing or instant messaging (IM), and it often directs users to enter details at a fake website, whose look and feel are almost identical to the legitimate one.
Phishing is a numbers game: If a hacker sends out 1 million phishing emails, they may get only a handful of responses -- but those responses can still be valuable. For example, a hacker may not get every bank password from a single phishing email, but if they can get one response out of 10,000 unsuspecting victims, their scam succeeded.
Pharming, on the other hand, is a form of phishing that uses a DNS system to send a user to a fake website. Instead of sending an email that looks like it's from a user's bank, pharming directs victims to a website that looks like their bank's website.
Signs of pharming
While there are steps to take to protect a system against pharming, there are two significant signs that pharming may be taking place:
- A slightly different site link and appearance. Pharming websites look slightly different than legitimate sites -- using different colors, logos or graphics -- but they attempt to trick a user into thinking the site is safe to visit. Sophisticated pharmers will try to convince users that they are on a legitimate site by using familiar logos and graphics to make users feel safe and secure. In addition, the website URL might be slightly different. For example, a pharming site might have minor spelling errors.
- An unsecure connection. Although Hypertext Transfer Protocol Secure (HTTPS) is a widely adopted security measure to protect users and their data, pharming scams continue to prey on unsuspecting users by luring them to insecure, fake websites. Pharming sites use a variety of tricks to appear legitimate, including using well-known logos and URL redirects. However, one commonality among all of these sites is the use of http instead of https in their URLs.
Protecting against pharming
There are many steps that can be taken to prevent pharming and other malicious attacks from occurring:
- Keep computers updated. Keeping a computer's operating system (OS) and other software updated is important for protecting against pharming because the latest software patches fix the vulnerabilities that hackers use to attack computers.
- Clear browser cache. While surfing the internet, browsers store information about the sites visited. If the same computer is used with a different internet connection, it is possible for a nefarious user to access the computer's information. To avoid this problem, it's a good idea to clear the cache before using a new internet connection.
- Download antivirus and antimalware software. Using an antivirus program is a common and effective way to protect a computer from online threats and to protect against pharming. Malware is often used to exploit security vulnerabilities in OSes and browsers and usually spreads using malicious code or links to malicious websites.
- Use HTTPS instead of HTTP. HTTPS is the secure communication protocol of the internet. It encrypts data so that it cannot be read by anyone but the intended receivers. HTTP -- the protocol that HTTPS replaces -- is much less secure and was designed before the increase of security risks of the internet.
Read more here on how to encrypt and secure websites using HTTPS.
- Use a virtual private network (VPN). A VPN hides IP addresses from websites and keeps hackers from stealing personal information. VPNs create encrypted connections between a device and an organization's network, so even if the DNS is hijacked, sensitive information will be safe. A VPN service should have reputable DNS servers.
- Use bookmarks. Bookmarking frequently accessed sites and not clicking on links in emails or on social networking sites will reduce the chance of pharming.






